Hot Posts

How To: 15 iPhone Tips for Busy Users to Maximize Your Productivity
When they first appeared, smartphones came with a promise to make our lives easier and make us more productive so we could have more free time and energy. But now, the average user spends almost 5 ½ hours daily on their smartphone. If that sounds like you, there are ways to use your iPhone more efficiently — without getting sucked into distractions.
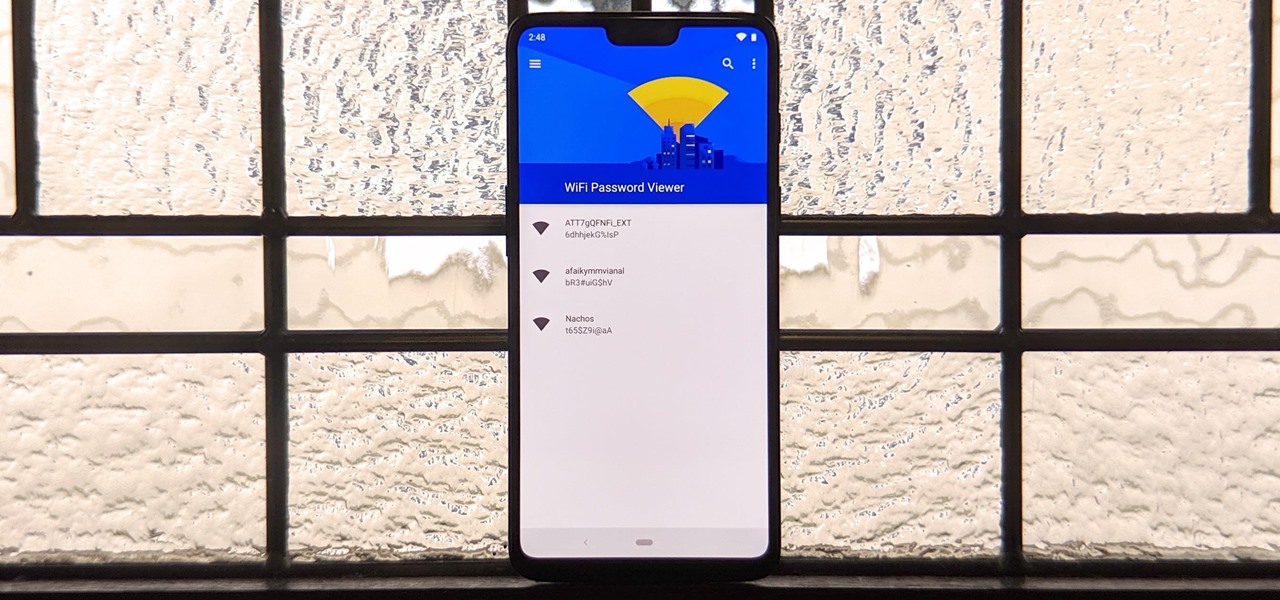
How To: See Passwords for Wi-Fi Networks You've Connected Your Android Device To
You've probably connected your Android device to dozens of Wi-Fi networks since you've had it, and your phone or tablet remembers each of them. Whether it's a hotspot at home, school, work, the gym, a coffee shop, a relative's apartment — or even from a friend's phone — each time you type in a Wi-Fi password, your Android device saves it for safekeeping and easy access later.

How To: Create an Admin User Account Using CMD Prompt (Windows)
This is a quick tutorial on how to create a new administrator account on a Windows computer. Step 1: Open CMD Prompt...

How To: Use FaceTime's Secret Hand Gestures and Reaction Buttons to Add Animated On-Screen Effects to Your Video Feed
Apple's Messages app has long had visual effects you could apply manually after long-pressing the send button, and there are even hidden keywords you could use to trigger full-screen effects automatically. FaceTime's latest update also gives you some full-screen effects to play around with during video calls, but the triggers are an entirely different concept — hand gestures.

How To: Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
One of the best ways to dig into a website and look for vulnerabilities is by using a proxy. By routing traffic through a proxy like Burp Suite, you can discover hidden flaws quickly, but sometimes it's a pain to turn it on and off manually. Luckily, there is a browser add-on called FoxyProxy that automates this process with a single click of a button.
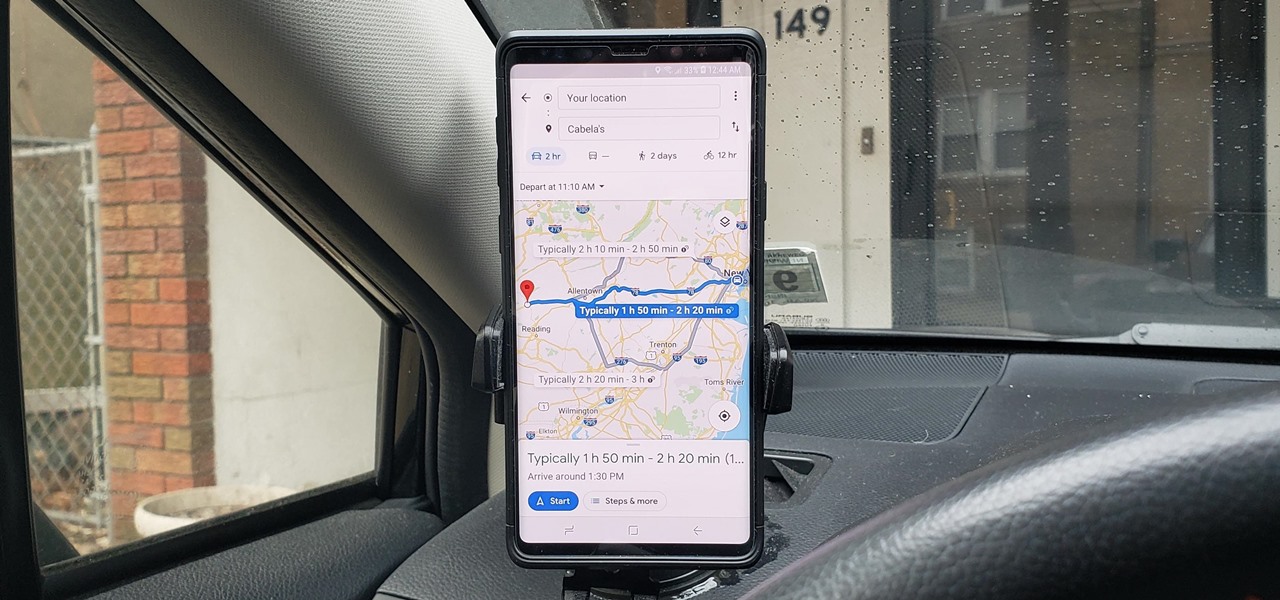
How To: See What Traffic Will Be Like at a Specific Time with Google Maps
As intuitive as Google Maps is for finding the best routes, it never let you choose departure and arrival times in the mobile app. This feature has long been available on the desktop site, allowing you to see what traffic should be like at a certain time and how long your drive would take at a point in the future. Fortunately, Google has finally added this feature to the app for iPhone and Android.

How To: Make This Amazing 9-Layer Density Tower from Things Found in Your Kitchen
Ralph Waldo Emerson once observed that "the seed of science" was "wonder," and taking a look at this nine-layer liquid tower from Steve Spangler's Sick Science! channel, one can't help but do just that — wonder. How is this possible? Is this magic or what?

How To: Keep Your Night Vision Sharp with the iPhone's Hidden Red Screen
Night Shift, Dark Mode, Reduce White Point, and Zoom's Low Light Filter all help reduce the harmful effects on your body's clock that bright iPhone and iPad screens have at night. But there's another option on iOS and iPadOS that turns your entire display red, and it's useful for so much more than just late-night browsing in bed.

How To: Make Spoofed Calls Using Any Phone Number You Want Right from Your Smartphone
Spoofed phone calls originate from one source that's disguising its phone number as a different one, and you probably get these calls all the time. Maybe they're numbers from your local area code or for prominent businesses, but the callers are just hijacking those digits to fool you into picking up. Turns out, making a spoofed call is something anybody can do — even you.

How to Hack a Vending Machine: 9 Tricks to Getting Free Drinks, Snacks & Money
A vending machine is an invaluable yet totally frustrating piece of equipment. It's a godsend whenever your tummy's growling or you need an ice-cold drink on a hot summer day. But when something gets stuck inside or the machine flat-out malfunctions, it quickly becomes your archenemy. And when you're broke, it's basically just one big tease.
Android Basics: How to See What Kind of Processor You Have (ARM, ARM64, or x86)
Starting with the release of Android Lollipop, the process of installing the Xposed Framework got a bit more complicated. Not only are there separate installers for each Android version, but now, you also need to know exactly what type of processor is in your device to make sure you're downloading the right files. In fact, CPU architecture is becoming a factor in more and more scenarios these days, including certain sideloaded app updates and, of course, custom ROMs.

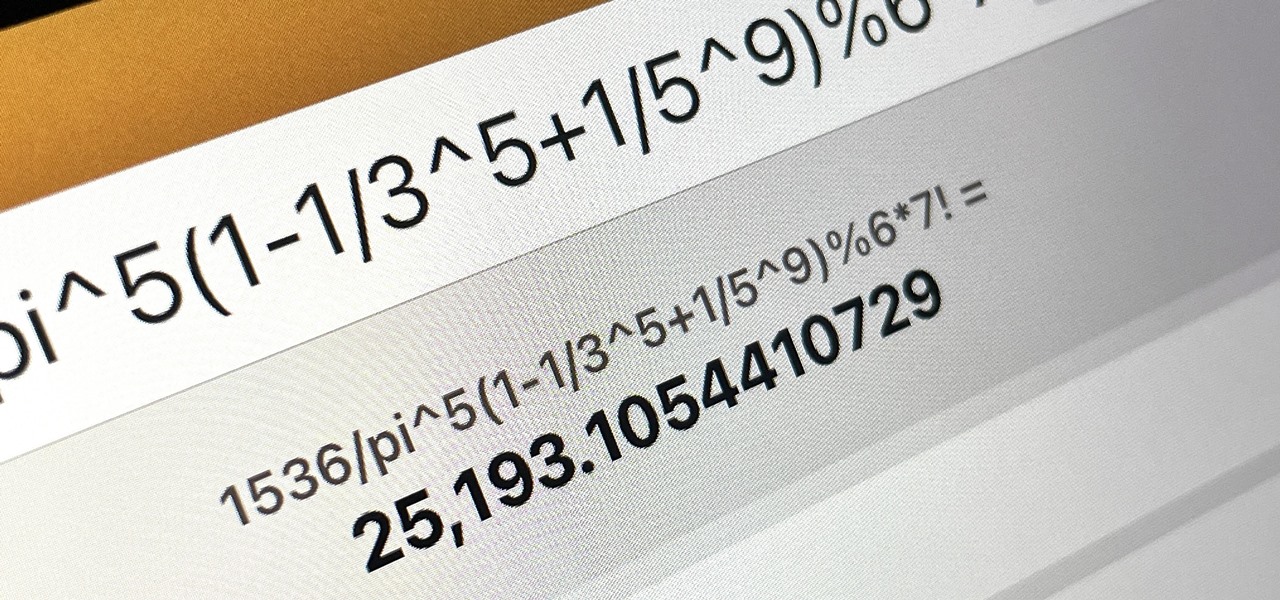
"Pi" meets SCRABBLE: A Metaphysical Religious Journey of Words & Numbers (CRAZIEST)
For as long as I've loved SCRABBLE, I can't believe I've never come across this before. "CRAZIEST" - A short story by Liz Dubelman about words
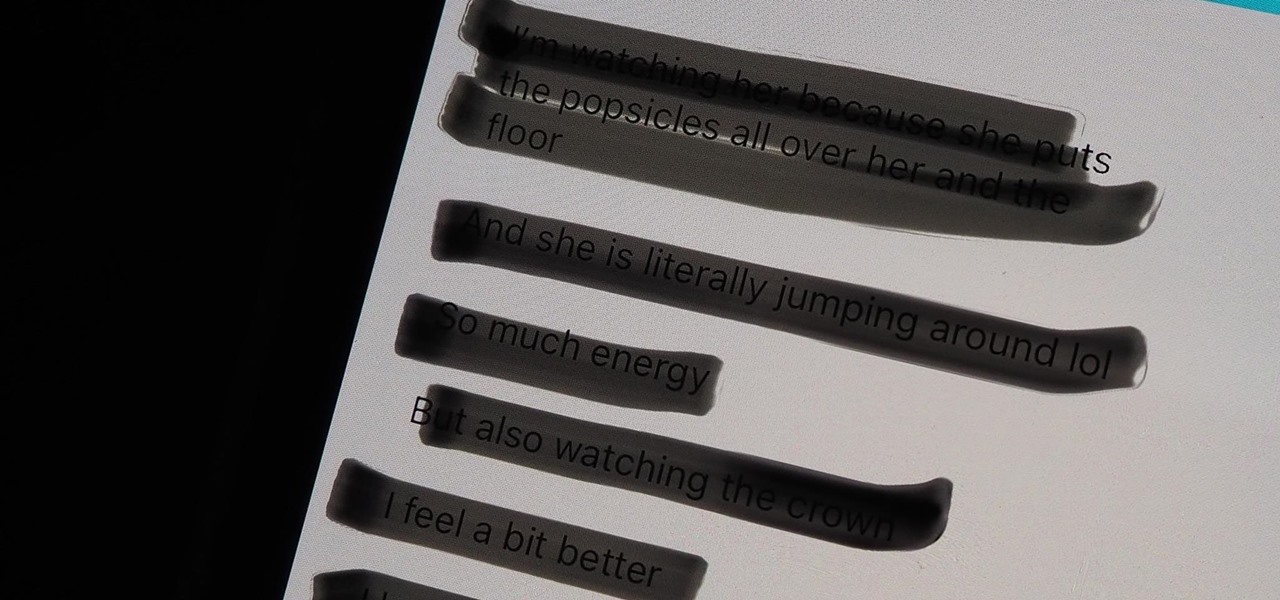
Warning: Sensitive Info You Black Out in Images Can Be Revealed with a Few Quick Edits on Your iPhone
These days, most images we post online or share with others come from our smartphones. Whenever personal data is in them, such as debit card numbers, addresses, phone numbers, passwords, and other sensitive information, it's easy to jump into your iPhone's markup tools to black out the text before sharing. But a digital marker may not hide everything.

How To: Dox Anyone
Doxing is the act of finding one's personal information through research and discovery, with little to no information to start with. You may have seen doxing in the news, for instance when not so long ago, hacker team Anonymous doxed and reported thousands of twitter accounts related to ISIS. Doxing can be useful for finding the address of a coworker, or simply investigating people on the internet. The tutorial I will provide to you now will teach you the basics of doxing and how you can prot...

How To: Crack SSH Private Key Passwords with John the Ripper
Secure Shell is one of the most common network protocols, typically used to manage remote machines through an encrypted connection. However, SSH is prone to password brute-forcing. Key-based authentication is much more secure, and private keys can even be encrypted for additional security. But even that isn't bulletproof since SSH private key passwords can be cracked using John the Ripper.
How To: Your iPad Has a Hidden Built-in Calculator You're Not Using — Here's How to Unlock It
There is no iPad version of Apple's Calculator app, so you won't find it on your Home Screen, in your App Library, or as a shortcut in the Control Center. But that doesn't mean your iPad doesn't have an official calculator.

How To: Find Vulnerable Webcams Across the Globe Using Shodan
Search engines index websites on the web so you can find them more efficiently, and the same is true for internet-connected devices. Shodan indexes devices like webcams, printers, and even industrial controls into one easy-to-search database, giving hackers access to vulnerable devices online across the globe. And you can search its database via its website or command-line library.

How To: Turn Your Gag Reflex Off with Pressure Points
The gag reflex: it can interfere while in the dentist's chair, upon seeing another person throw up, or even just getting a whiff of a disgusting, stomach-twisting scent. Every time this reflex kicks in, it stops us immediately, inducing a choking, gagging, coughing fit.

How To: Scan for Vulnerabilities on Any Website Using Nikto
Before attacking any website, a hacker or penetration tester will first compile a list of target surfaces. After they've used some good recon and found the right places to point their scope at, they'll use a web server scanning tool such as Nikto for hunting down vulnerabilities that could be potential attack vectors.

How To: Brute-Force FTP Credentials & Get Server Access
Hackers often find fascinating files in the most ordinary of places, one of those being FTP servers. Sometimes, luck will prevail, and anonymous logins will be enabled, meaning anyone can just log in. But more often than not, a valid username and password will be required. But there are several methods to brute-force FTP credentials and gain server access.

How To: Make Delicious Thai Sticky Rice Without a Steamer or Rice Cooker
If you're a fan of Thai food, I'm sure you're familiar with sticky rice. There is something so special about its chewy texture and sweet flavor. If you have a desire to make it in your own kitchen but don't have the proper tools such as a traditional bamboo basket or stackable steamer, there are several other methods that work just as well. Once you try these alternative methods, I'm sure you'll be "sticking" to them for a while. What Makes Sticky Rice So Sticky?
How To: Brute-Force WPA/WPA2 via GPU
Most of you lot would be aware what WPA/WPA2 is so I won't bang on about the encryption or protocols a great deal. In short WPA and WPA2 both have a maximum of 256bit encrypted with a maximum of 64 characters in the password. The encryption is really only 64bit but x 4 because of the way the authentication functions as a 4 way handshake.
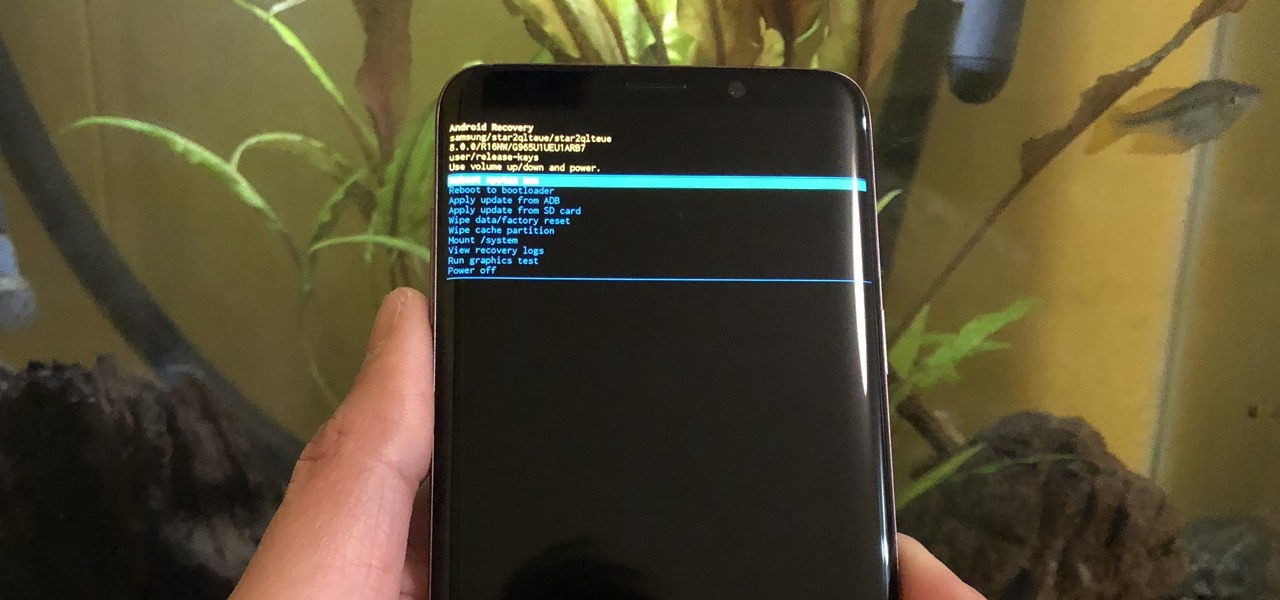
How To: Boot Your Galaxy S9 or S9+ into Recovery Mode or Download Mode
From veteran modders to casual tinkerers, booting into either recovery mode or download mode is something every Galaxy S9 owner should know about. These two pre-boot menus serve a very important purpose — recovery mode is the go-to solution for soft bricks, while download mode allows you to flash firmware files using utilities like Odin and Smart Switch, which can truly be a lifesaver.

Scrabble Challenge #20: What Would You Do with a Rack Full of Vowels?
You're currently playing a heated game of Scrabble or Words with Friends. The game is close, too close for comfort. But you're not sweating because you're confident. You play a huge word that puts you in the lead, but then when your letter tiles are drawn...

Hack Like a Pro: How to Scan for Vulnerabilities with Nessus
Welcome back, my tenderfoot hackers! Generally, you will want to perform a vulnerability scan before doing a penetration test. Vulnerability scanners contain a database of all known vulnerabilities and will scan your machine or network to see whether those vulnerabilities appear to exist. If they do, it is your job to test whether they are real and can be exploited.

How To: The Trick That Lets You Link to Specific Start Times in YouTube Videos Right from Your Phone
You can add a timestamp to any YouTube video in just a few clicks from the desktop website on your computer but not from YouTube's iOS or Android app. Until YouTube adds a "start time" when sharing videos from the mobile app, you'll have to use one of these workarounds on your phone or tablet.
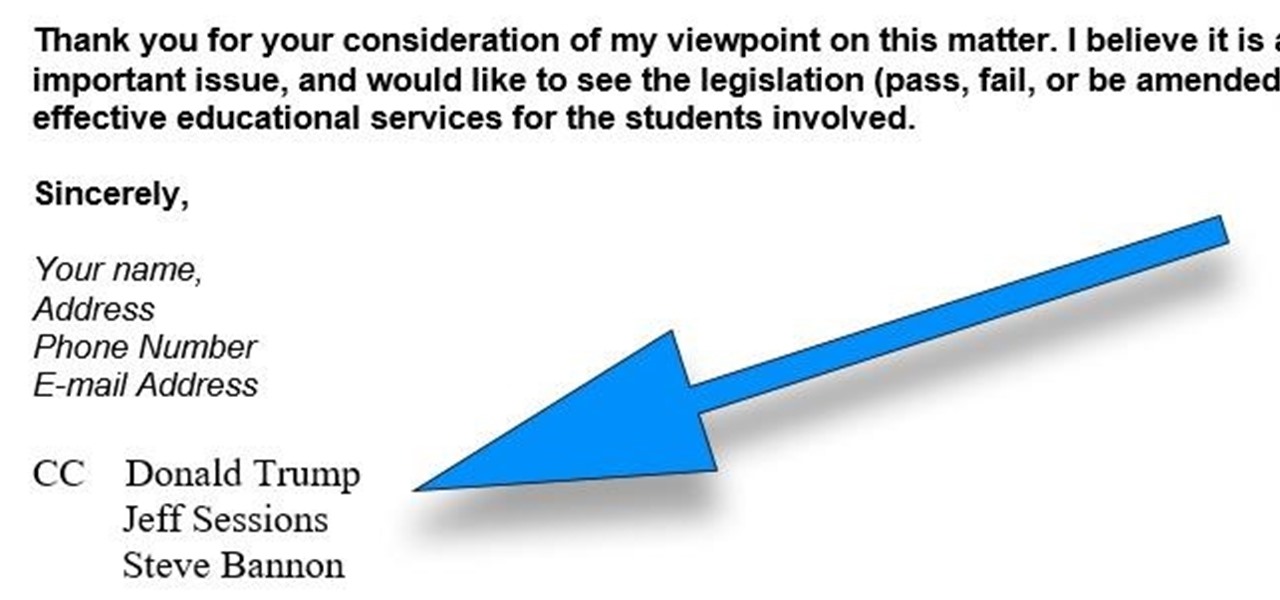
How To: CC in a Physical Business Letter
CC, which stands for "carbon copy", is a familiar phrase in email, but can also be used in business letters and legal documents. This can be especially useful for letters you want to spend up a company or organizational chain, letting each recipient know exactly who else received the same document.

Modular Origami: How to Make a Cube, Octahedron & Icosahedron from Sonobe Units
Modular origami is a technique that can be used to build some pretty interesting and impressive models of mathematical objects. In modular origami, you combine multiple units folded from single pieces of paper into more complicated forms. The Sonobe unit is a simple example unit from modular origami that is both easy to fold and compatible for constructing a large variety of models. Below are a few models that are easy to make using this unit.

How To: 16 Harry Potter Spells for Siri That Turn Your iPhone into a Magical Elder Wand
Your days as an ordinary Muggle are over — as long as you have an iPhone. With just a word or two, you can use your iPhone and newfound Muggle-born powers to cast spells or utilize charms just like Harry Potter and team. Only your "wand" is from Apple, not Ollivanders in Diagon Alley.

How To: Find Identifying Information from a Phone Number Using OSINT Tools
Phone numbers often contain clues to the owner's identity and can bring up a lot of data during an OSINT investigation. Starting with a phone number, we can search through a large number of online databases with only a few clicks to discover information about a phone number. It can include the carrier, the owner's name and address, and even connected online accounts.

How To: There's an Easy Way to See All the Unsent Messages in Your iMessage Conversations
While you can quickly see the edit history of a modified iMessage in the Messages app, there's no way to view an iMessage that somebody in the conversation deleted unless you happened to see it before it disappeared. But that's only true if you didn't implement these security measures on your iPhone.

How To: Revive a Stale Baguette Using the Miraculous Water Trick
Everyone talks about how great sliced bread is, but there's nothing better than the taste of a just-baked loaf of crusty French bread. Like most beautiful things in life, however, the beauty of the baguette doesn't last. The next day, it's rock-hard, and good for very little except for croutons or breadcrumbs. But there is a trick to make it like fresh again.

How To: 19 Harry Potter Spells Your Android Phone Can Cast Using Google Assistant
Apple's Siri is well-versed in the spells of the Wizarding World of Harry Potter, but it's not like Android users are Muggles. Google Assistant, Android's virtual concierge, can cast a few spells out of the box, and it can learn the spells it doesn't know quicker than a year of studying at Hogwarts.

How To: 100+ Secret Dialer Codes for Your iPhone
There's a lot more to your iPhone's dialer screen than just entering phone numbers and hitting the green call button. It's not very obvious, but there are secret codes that you can enter on the dialer to find out information about your device, help troubleshoot issues, and mask outgoing calls, to name just a few things.

How To: Generate random numbers (with decimals) in Excel
This video shows you how to generate random numbers with decimals in Microsoft Excel.When generating random numbers you must have a lower and upper limit, so that your number will be generated between the two limits. For a number without decimals, you only have to use the "=randbetween" function. If you want to use decimals, you will have to use a different but similar function. Start by typing "=rand()". Next, you multiply this by the difference between the limits and add the lower limit. Fo...
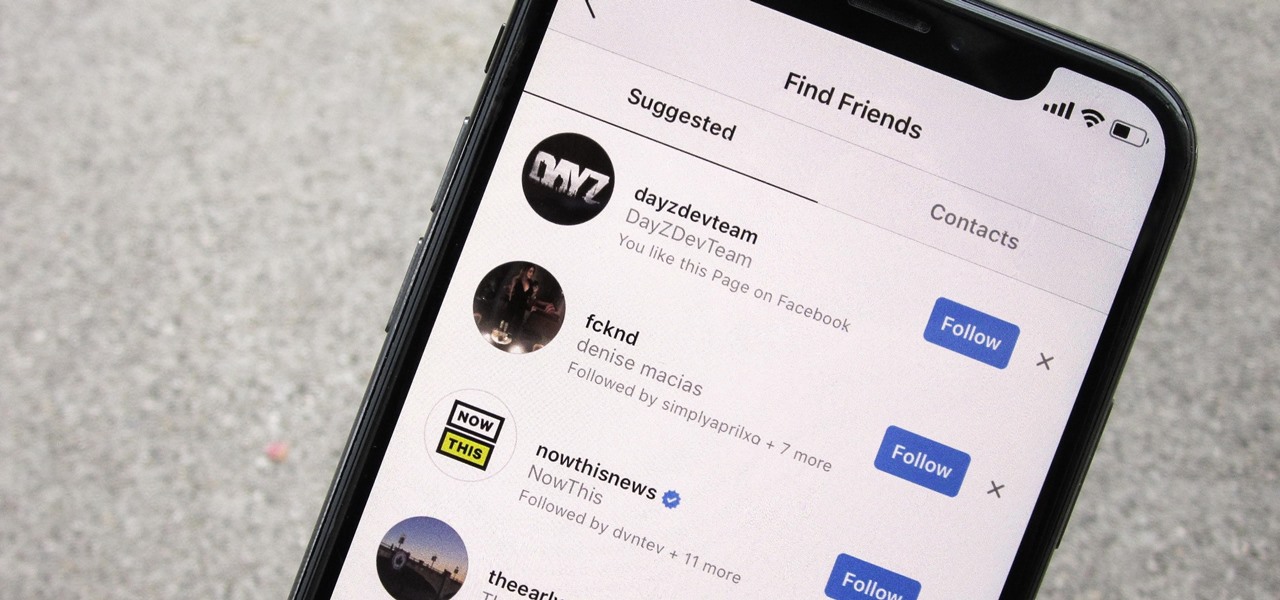
How To: Prevent People Who Have Your Contact Information from Finding Your Instagram Account
Sharing your personal information can come up for any number of reasons: you may want to get in touch with a colleague after work or you've been involved in a car accident and need to stay in contact with the other driver. Unfortunately, giving out information can be the key for others to find your social media accounts, such as Instagram, whether you want it to happen or not.
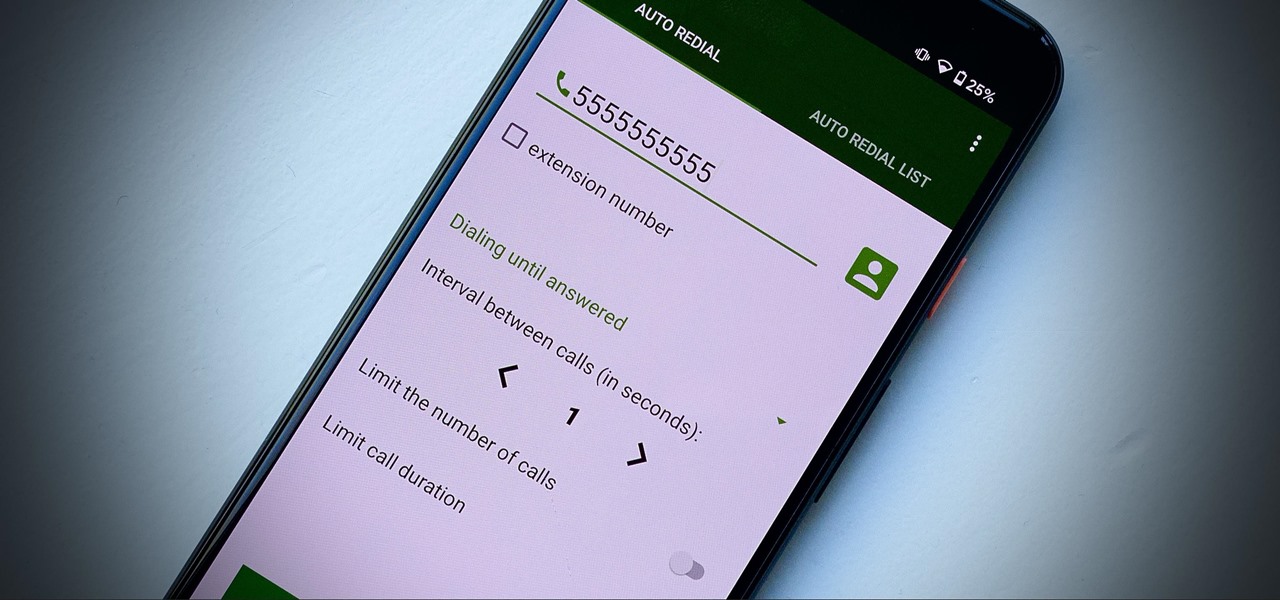
How To: These Auto-Redial Apps Can Call Busy Phone Lines Over and Over Again Until You Get Through
Some phone lines make it nearly impossible to get past the busy tone, whether it's a viral call-in giveaway, your state's unemployment office, your local post office during the holidays, or the repair office for a broken warrantied product you have. Thankfully, there are apps you can use to help break through the noise.
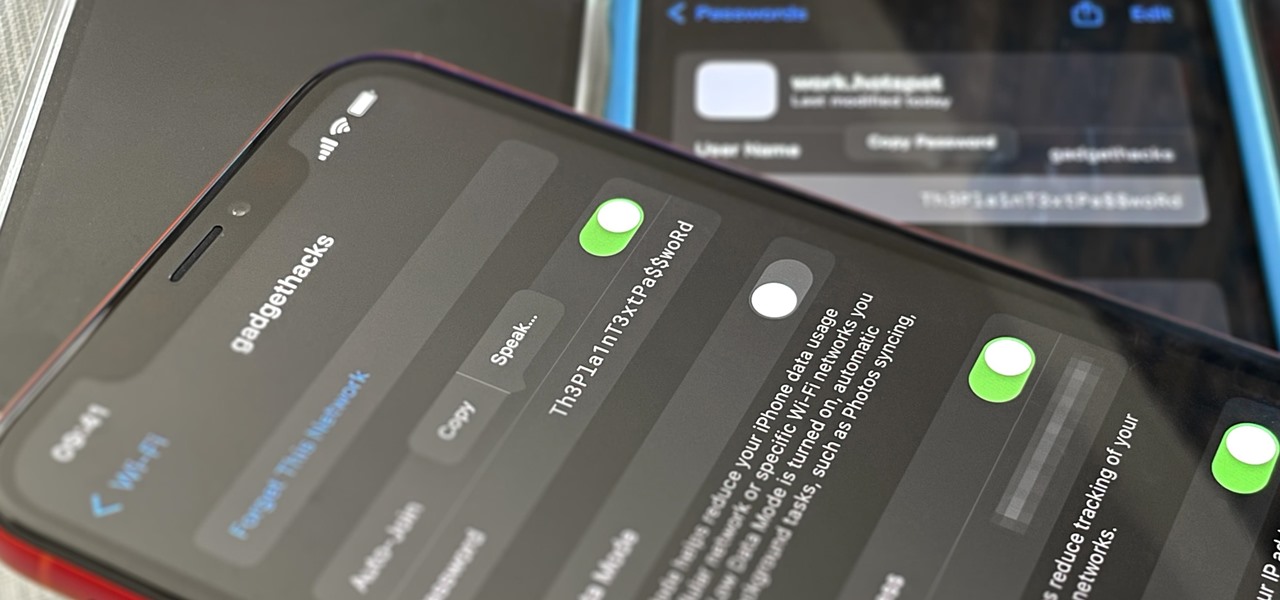
How To: See Passwords for All the Wi-Fi Networks You've Connected Your iPhone To
Your iPhone goes with you pretty much everywhere you go, and unless you have unlimited data on your cellular plan, you've probably connected to dozens of Wi-Fi hotspots over the years. Wi-Fi passwords are saved to your iPhone so you can auto-connect to the router or personal hotspot again, but finding the plain text password for a network hasn't always been easy.

How To: Customize and Use Control Center on Your iPhone for Quick Access to Your Most-Used Apps, Features, and Settings
If you're not using Control Center on your iPhone, you're missing out on a powerful tool that can streamline how you interact with your device, make certain tasks more efficient, and give you quick access to system tools, switches, and sliders for quick changes no matter where you are or what app you're in.

Redstone Logic Gates: Mastering the Fundamental Building Blocks for Creating In-Game Machines
Many people get so discouraged by their failures with redstone that they give up using it entirely, or never progress beyond using simple switches. However, by incorporating logic gates into your redstone designs, the applications are nearly limitless. The ability to add multiple switches to your machines is just a small part of what logic gates can do. Most importantly, they give you control.