Kody's Latest Posts
 How To:
Track Wi-Fi Devices & Connect to Them Using Probequest
How To:
Track Wi-Fi Devices & Connect to Them Using Probequest
 How To:
Use MDK3 for Advanced Wi-Fi Jamming
How To:
Use MDK3 for Advanced Wi-Fi Jamming
 How To:
Use Maltego to Monitor Twitter for Disinformation Campaigns
How To:
Use Maltego to Monitor Twitter for Disinformation Campaigns
 How To:
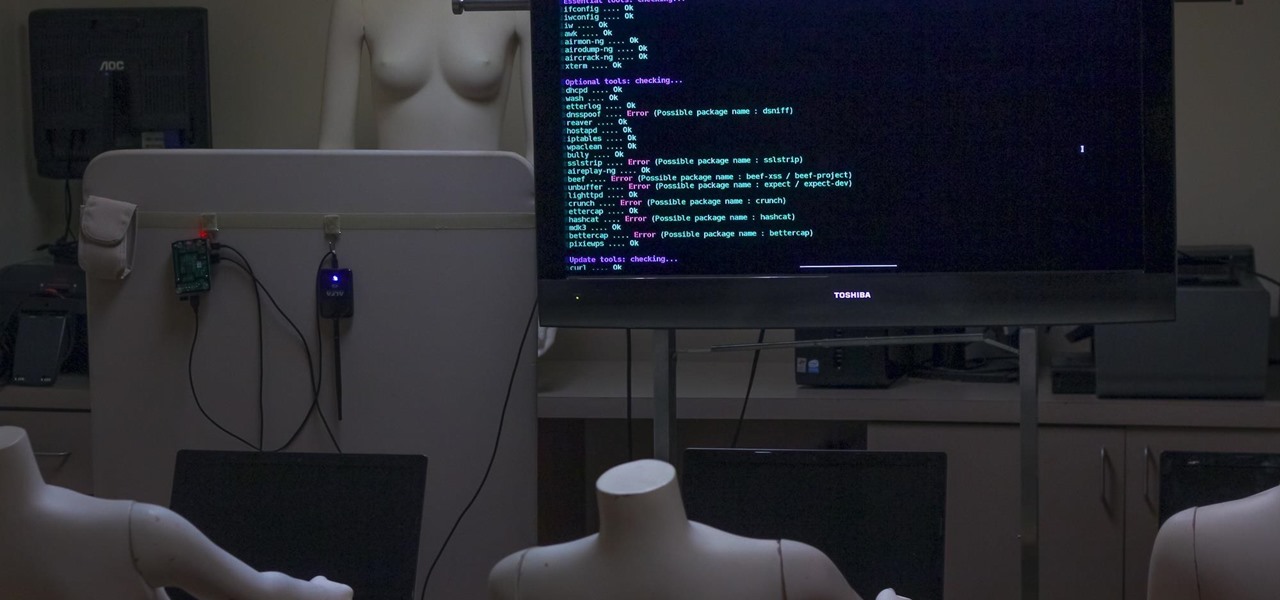
Hack Wi-Fi & Networks More Easily with Lazy Script
How To:
Hack Wi-Fi & Networks More Easily with Lazy Script
 How To:
Use Beginner Python to Build a Brute-Force Tool for SHA-1 Hashes
How To:
Use Beginner Python to Build a Brute-Force Tool for SHA-1 Hashes
 How To:
The Beginner's Guide to Defending Against Wi-Fi Hacking
How To:
The Beginner's Guide to Defending Against Wi-Fi Hacking
 How to Hack Wi-Fi:
Disabling Security Cameras on Any Wireless Network with Aireplay-Ng
How to Hack Wi-Fi:
Disabling Security Cameras on Any Wireless Network with Aireplay-Ng
 How To:
Bypass Locked Windows Computers to Run Kali Linux from a Live USB
How To:
Bypass Locked Windows Computers to Run Kali Linux from a Live USB
 How To:
Use Maltego to Fingerprint an Entire Network Using Only a Domain Name
How To:
Use Maltego to Fingerprint an Entire Network Using Only a Domain Name
 Hacking macOS:
How to Steal Signal Conversations from a MacBook with a USB Rubber Ducky
Hacking macOS:
How to Steal Signal Conversations from a MacBook with a USB Rubber Ducky
 How To:
Use Maltego to Target Company Email Addresses That May Be Vulnerable from Third-Party Breaches
How To:
Use Maltego to Target Company Email Addresses That May Be Vulnerable from Third-Party Breaches
 How To:
Build a Beginner Hacking Kit with the Raspberry Pi 3 Model B+
How To:
Build a Beginner Hacking Kit with the Raspberry Pi 3 Model B+
 How To:
Create Custom Wordlists for Password Cracking Using the Mentalist
How To:
Create Custom Wordlists for Password Cracking Using the Mentalist
 How to Hack Wi-Fi:
Stealing Wi-Fi Passwords with an Evil Twin Attack
How to Hack Wi-Fi:
Stealing Wi-Fi Passwords with an Evil Twin Attack
 How to Hack Wi-Fi:
Hunting Down & Cracking WEP Networks
How to Hack Wi-Fi:
Hunting Down & Cracking WEP Networks
 How To:
Hack WPA & WPA2 Wi-Fi Passwords with a Pixie-Dust Attack Using Airgeddon
How To:
Hack WPA & WPA2 Wi-Fi Passwords with a Pixie-Dust Attack Using Airgeddon
 How To:
Hack Open Hotel, Airplane & Coffee Shop Wi-Fi with MAC Address Spoofing
How To:
Hack Open Hotel, Airplane & Coffee Shop Wi-Fi with MAC Address Spoofing
 How To:
Use U2F Security Keys on Your Smartphone to Access Your Google Account with Advanced Protection
How To:
Use U2F Security Keys on Your Smartphone to Access Your Google Account with Advanced Protection
 How To:
Track Down a Tinder Profile with Location Spoofing on Google Chrome
How To:
Track Down a Tinder Profile with Location Spoofing on Google Chrome
 How To:
Use Google's Advanced Protection Program to Secure Your Account from Phishing
How To:
Use Google's Advanced Protection Program to Secure Your Account from Phishing
 How To:
Use Kismet to Watch Wi-Fi User Activity Through Walls
How To:
Use Kismet to Watch Wi-Fi User Activity Through Walls
 Video:
How to Crack Weak Wi-Fi Passwords in Seconds with Airgeddon on Parrot OS
Video:
How to Crack Weak Wi-Fi Passwords in Seconds with Airgeddon on Parrot OS
 Video:
How to Use Maltego to Research & Mine Data Like an Analyst
Video:
How to Use Maltego to Research & Mine Data Like an Analyst
 How To:
Dump a MacOS User's Chrome Passwords with EvilOSX
How To:
Dump a MacOS User's Chrome Passwords with EvilOSX
 How To:
Null Byte & Null Space Labs Present: Wi-Fi Hacking, MITM Attacks & the USB Rubber Ducky
How To:
Null Byte & Null Space Labs Present: Wi-Fi Hacking, MITM Attacks & the USB Rubber Ducky
 How to Hack Wi-Fi:
Build a Software-Based Wi-Fi Jammer with Airgeddon
How to Hack Wi-Fi:
Build a Software-Based Wi-Fi Jammer with Airgeddon
 How to Hack Wi-Fi:
Automating Wi-Fi Hacking with Besside-ng
How to Hack Wi-Fi:
Automating Wi-Fi Hacking with Besside-ng
 How to Hack Wi-Fi:
Capturing WPA Passwords by Targeting Users with a Fluxion Attack
How to Hack Wi-Fi:
Capturing WPA Passwords by Targeting Users with a Fluxion Attack
 How to Hack Wi-Fi:
Get Anyone's Wi-Fi Password Without Cracking Using Wifiphisher
How to Hack Wi-Fi:
Get Anyone's Wi-Fi Password Without Cracking Using Wifiphisher
Next Page
Prev Page Sites
- Hot
- Latest
-
 How To:
Change a Phone's Coordinates by Spoofing Wi-Fi Geolocation Hotspots
How To:
Change a Phone's Coordinates by Spoofing Wi-Fi Geolocation Hotspots
-
 How To:
Hunt Down Wi-Fi Devices with a Directional Antenna
How To:
Hunt Down Wi-Fi Devices with a Directional Antenna
-
 How To:
Hack 5 GHz Wi-Fi Networks with an Alfa Wi-Fi Adapter
How To:
Hack 5 GHz Wi-Fi Networks with an Alfa Wi-Fi Adapter
-
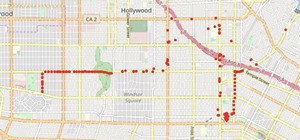 How To:
Map Wardriving Data with Jupyter Notebook
How To:
Map Wardriving Data with Jupyter Notebook
-
 How To:
Pick an Antenna for Wi-Fi Hacking
How To:
Pick an Antenna for Wi-Fi Hacking
-
 How to Hack with Arduino:
Defeat VPNs & Track a MacOS Computer Remotely
How to Hack with Arduino:
Defeat VPNs & Track a MacOS Computer Remotely
-
 How to Hack with Arduino:
Tracking Which Networks a Mac Has Connected To & When
How to Hack with Arduino:
Tracking Which Networks a Mac Has Connected To & When
-
 How To:
Spy on SSH Sessions with SSHPry2.0
How To:
Spy on SSH Sessions with SSHPry2.0
-
 How To:
Analyze Wi-Fi Data Captures with Jupyter Notebook
How To:
Analyze Wi-Fi Data Captures with Jupyter Notebook
-
 How to Hack with Arduino:
Building MacOS Payloads for Inserting a Wi-Fi Backdoor
How to Hack with Arduino:
Building MacOS Payloads for Inserting a Wi-Fi Backdoor
-
 How To:
Hack Wi-Fi Networks with Bettercap
How To:
Hack Wi-Fi Networks with Bettercap
-
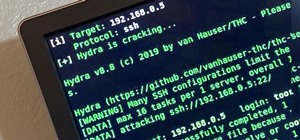
 How To:
Brute-Force SSH, FTP, VNC & More with BruteDum
How To:
Brute-Force SSH, FTP, VNC & More with BruteDum
-
 How To:
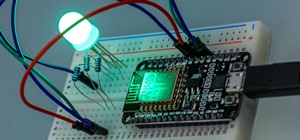
Program MicroPython NeoPixel Holiday Lights to Animate However You Want
How To:
Program MicroPython NeoPixel Holiday Lights to Animate However You Want
-
 How To:
Get Started with MicroPython for ESP8266 Microcontrollers
How To:
Get Started with MicroPython for ESP8266 Microcontrollers
-
 How To:
Crack WPA & WPA2 Wi-Fi Passwords with Pyrit
How To:
Crack WPA & WPA2 Wi-Fi Passwords with Pyrit
-
 How To:
Use Hash-Identifier to Determine Hash Types for Password Cracking
How To:
Use Hash-Identifier to Determine Hash Types for Password Cracking
-
 How To:
Spy on Traffic from a Smartphone with Wireshark
How To:
Spy on Traffic from a Smartphone with Wireshark
-
 How To:
Securely Sniff Wi-Fi Packets with Sniffglue
How To:
Securely Sniff Wi-Fi Packets with Sniffglue
-
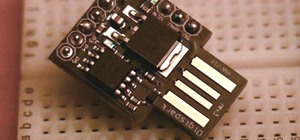
 How To:
Hack MacOS with Digispark Ducky Script Payloads
How To:
Hack MacOS with Digispark Ducky Script Payloads
-
 How To:
Run Your Favorite Graphical X Applications Over SSH
How To:
Run Your Favorite Graphical X Applications Over SSH
-
 How To:
Scan for Vulnerabilities on Any Website Using Nikto
How To:
Scan for Vulnerabilities on Any Website Using Nikto
-
 How To:
Find Vulnerable Webcams Across the Globe Using Shodan
How To:
Find Vulnerable Webcams Across the Globe Using Shodan
-
 How to Hack Wi-Fi:
Stealing Wi-Fi Passwords with an Evil Twin Attack
How to Hack Wi-Fi:
Stealing Wi-Fi Passwords with an Evil Twin Attack
-
 How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
How To:
Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
-
 How to Hack Wi-Fi:
Cracking WPA2 Passwords Using the New PMKID Hashcat Attack
How to Hack Wi-Fi:
Cracking WPA2 Passwords Using the New PMKID Hashcat Attack
-
 How To:
Spy on Traffic from a Smartphone with Wireshark
How To:
Spy on Traffic from a Smartphone with Wireshark
-
 How To:
Hack Wi-Fi Networks with Bettercap
How To:
Hack Wi-Fi Networks with Bettercap
-
 How To:
Hack 5 GHz Wi-Fi Networks with an Alfa Wi-Fi Adapter
How To:
Hack 5 GHz Wi-Fi Networks with an Alfa Wi-Fi Adapter
-
 How To:
Use MDK3 for Advanced Wi-Fi Jamming
How To:
Use MDK3 for Advanced Wi-Fi Jamming
-
 How To:
Control Network Traffic with Evil Limiter to Throttle or Kick Off Devices
How To:
Control Network Traffic with Evil Limiter to Throttle or Kick Off Devices
-
 How To:
Program a $6 NodeMCU to Detect Wi-Fi Jamming Attacks in the Arduino IDE
How To:
Program a $6 NodeMCU to Detect Wi-Fi Jamming Attacks in the Arduino IDE
-
 How To:
Brute-Force Nearly Any Website Login with Hatch
How To:
Brute-Force Nearly Any Website Login with Hatch
-
 How To:
Use Kismet to Watch Wi-Fi User Activity Through Walls
How To:
Use Kismet to Watch Wi-Fi User Activity Through Walls
-
 How To:
Find Identifying Information from a Phone Number Using OSINT Tools
How To:
Find Identifying Information from a Phone Number Using OSINT Tools
-
 How To:
Find Passwords in Exposed Log Files with Google Dorks
How To:
Find Passwords in Exposed Log Files with Google Dorks
-
 How to Hack Wi-Fi:
Get Anyone's Wi-Fi Password Without Cracking Using Wifiphisher
How to Hack Wi-Fi:
Get Anyone's Wi-Fi Password Without Cracking Using Wifiphisher
-
 How To:
Use Ettercap to Intercept Passwords with ARP Spoofing
How To:
Use Ettercap to Intercept Passwords with ARP Spoofing
-
 How To:
Automate Wi-Fi Hacking with Wifite2
How To:
Automate Wi-Fi Hacking with Wifite2
-
 How To:
Hack Wi-Fi & Networks More Easily with Lazy Script
How To:
Hack Wi-Fi & Networks More Easily with Lazy Script
-
 How To:
Phish for Social Media & Other Account Passwords with BlackEye
How To:
Phish for Social Media & Other Account Passwords with BlackEye
-
 Video:
How to Crack Weak Wi-Fi Passwords in Seconds with Airgeddon on Parrot OS
Video:
How to Crack Weak Wi-Fi Passwords in Seconds with Airgeddon on Parrot OS
-
 How To:
Spy on SSH Sessions with SSHPry2.0
How To:
Spy on SSH Sessions with SSHPry2.0
-
 How To:
Intercept Images from a Security Camera Using Wireshark
How To:
Intercept Images from a Security Camera Using Wireshark
-
 How To:
Use Hash-Identifier to Determine Hash Types for Password Cracking
How To:
Use Hash-Identifier to Determine Hash Types for Password Cracking
-
 How To:
Create Custom Wordlists for Password Cracking Using the Mentalist
How To:
Create Custom Wordlists for Password Cracking Using the Mentalist
-
 How To:
Target Bluetooth Devices with Bettercap
How To:
Target Bluetooth Devices with Bettercap
-
 How To:
Pick an Antenna for Wi-Fi Hacking
How To:
Pick an Antenna for Wi-Fi Hacking
-
 How To:
Scan, Fake & Attack Wi-Fi Networks with the ESP8266-Based WiFi Deauther
How To:
Scan, Fake & Attack Wi-Fi Networks with the ESP8266-Based WiFi Deauther
-
 How To:
Enable Monitor Mode & Packet Injection on the Raspberry Pi
How To:
Enable Monitor Mode & Packet Injection on the Raspberry Pi
-
 How To:
Crack WPA & WPA2 Wi-Fi Passwords with Pyrit
How To:
Crack WPA & WPA2 Wi-Fi Passwords with Pyrit
-
 How to Hack Wi-Fi:
Capturing WPA Passwords by Targeting Users with a Fluxion Attack
How to Hack Wi-Fi:
Capturing WPA Passwords by Targeting Users with a Fluxion Attack
-
 How To:
Load Kali Linux on the Raspberry Pi 4 for the Ultimate Miniature Hacking Station
How To:
Load Kali Linux on the Raspberry Pi 4 for the Ultimate Miniature Hacking Station
-
 How to Hack Wi-Fi:
Disabling Security Cameras on Any Wireless Network with Aireplay-Ng
How to Hack Wi-Fi:
Disabling Security Cameras on Any Wireless Network with Aireplay-Ng
-
 How To:
Hack WPA & WPA2 Wi-Fi Passwords with a Pixie-Dust Attack Using Airgeddon
How To:
Hack WPA & WPA2 Wi-Fi Passwords with a Pixie-Dust Attack Using Airgeddon
-
 How To:
Hunt Down Social Media Accounts by Usernames with Sherlock
How To:
Hunt Down Social Media Accounts by Usernames with Sherlock
-
 How To:
Build a Beginner Hacking Kit with the Raspberry Pi 3 Model B+
How To:
Build a Beginner Hacking Kit with the Raspberry Pi 3 Model B+
-
 How To:
Tactical Nmap for Beginner Network Reconnaissance
How To:
Tactical Nmap for Beginner Network Reconnaissance
-
 How To:
Use & Abuse the Address Resolution Protocol (ARP) to Locate Hosts on a Network
How To:
Use & Abuse the Address Resolution Protocol (ARP) to Locate Hosts on a Network
-
 How To:
Use Maltego to Fingerprint an Entire Network Using Only a Domain Name
How To:
Use Maltego to Fingerprint an Entire Network Using Only a Domain Name
-
 How To:
Create Malicious QR Codes to Hack Phones & Other Scanners
How To:
Create Malicious QR Codes to Hack Phones & Other Scanners