SADMIN's Popular Posts
 How To:
Log Wi-Fi Probe Requests from Smartphones & Laptops with Probemon
How To:
Log Wi-Fi Probe Requests from Smartphones & Laptops with Probemon
 How To:
Set Up Kali Linux on the New $10 Raspberry Pi Zero W
How To:
Set Up Kali Linux on the New $10 Raspberry Pi Zero W
 How To:
Buy the Best Wireless Network Adapter for Wi-Fi Hacking in 2019
How To:
Buy the Best Wireless Network Adapter for Wi-Fi Hacking in 2019
 How To:
Wardrive with the Kali Raspberry Pi to Map Wi-Fi Devices
How To:
Wardrive with the Kali Raspberry Pi to Map Wi-Fi Devices
 How To:
Seize Control of a Router with RouterSploit
How To:
Seize Control of a Router with RouterSploit
 How To:
Set Up a Headless Raspberry Pi Hacking Platform Running Kali Linux
How To:
Set Up a Headless Raspberry Pi Hacking Platform Running Kali Linux
 How To:
Wardrive on an Android Phone to Map Vulnerable Networks
How To:
Wardrive on an Android Phone to Map Vulnerable Networks
 How To:
Build a Pumpkin Pi — The Rogue AP & MITM Framework That Fits in Your Pocket
How To:
Build a Pumpkin Pi — The Rogue AP & MITM Framework That Fits in Your Pocket
 How To:
Create Packets from Scratch with Scapy for Scanning & DoSing
How To:
Create Packets from Scratch with Scapy for Scanning & DoSing
 How To:
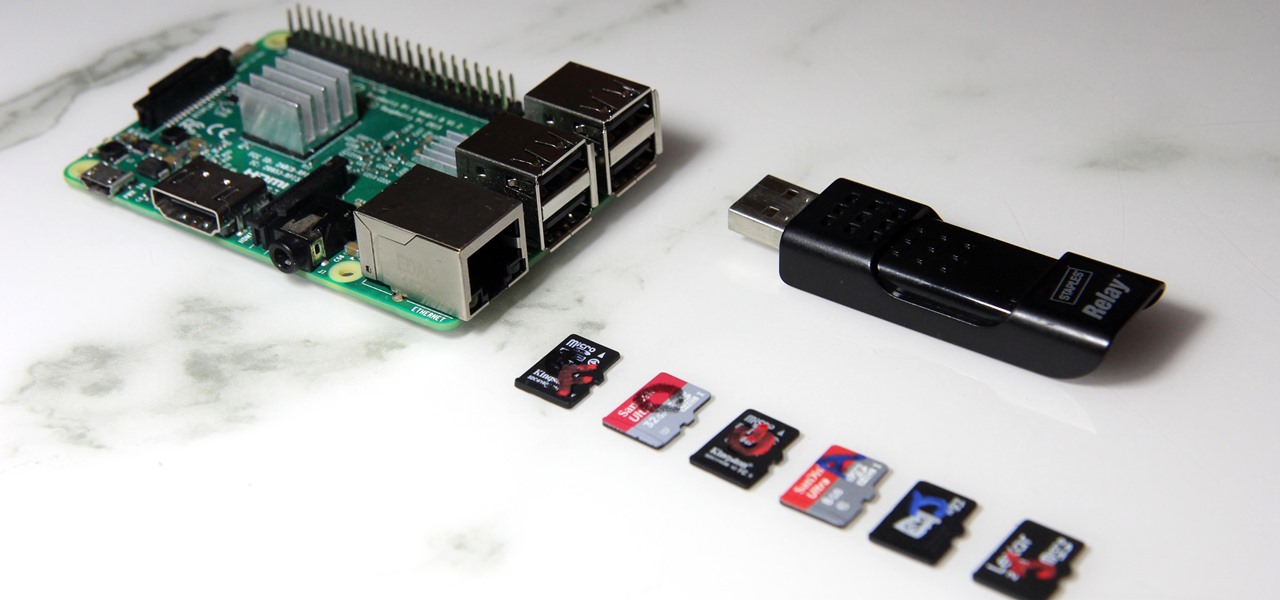
Boot Multiple Operating Systems on the Raspberry Pi with BerryBoot
How To:
Boot Multiple Operating Systems on the Raspberry Pi with BerryBoot
 How To:
Exploit Routers on an Unrooted Android Phone
How To:
Exploit Routers on an Unrooted Android Phone
 How To:
Steal macOS Files with the USB Rubber Ducky
How To:
Steal macOS Files with the USB Rubber Ducky
 How To:
Map Networks & Connect to Discovered Devices Using Your Phone
How To:
Map Networks & Connect to Discovered Devices Using Your Phone
 How To:
Automate Hacking on the Raspberry Pi with the USB Rubber Ducky
How To:
Automate Hacking on the Raspberry Pi with the USB Rubber Ducky
 How To:
Set Up a Practice Computer to Kill on a Raspberry Pi
How To:
Set Up a Practice Computer to Kill on a Raspberry Pi
 How to Hack Radio Frequencies:
Building a Radio Listening Station to Decode Digital Audio & Police Dispatches
How to Hack Radio Frequencies:
Building a Radio Listening Station to Decode Digital Audio & Police Dispatches
 How to Hack Radio Frequencies:
Hijacking FM Radio with a Raspberry Pi & Wire
How to Hack Radio Frequencies:
Hijacking FM Radio with a Raspberry Pi & Wire
 How To:
Modify the USB Rubber Ducky with Custom Firmware
How To:
Modify the USB Rubber Ducky with Custom Firmware
 How To:
Load & Use Keystroke Injection Payloads on the USB Rubber Ducky
How To:
Load & Use Keystroke Injection Payloads on the USB Rubber Ducky
 Recon:
How to Research a Person or Organization Using the Operative Framework
Recon:
How to Research a Person or Organization Using the Operative Framework
 Social Engineering:
How to Use Persuasion to Compromise a Human Target
Social Engineering:
How to Use Persuasion to Compromise a Human Target
 News:
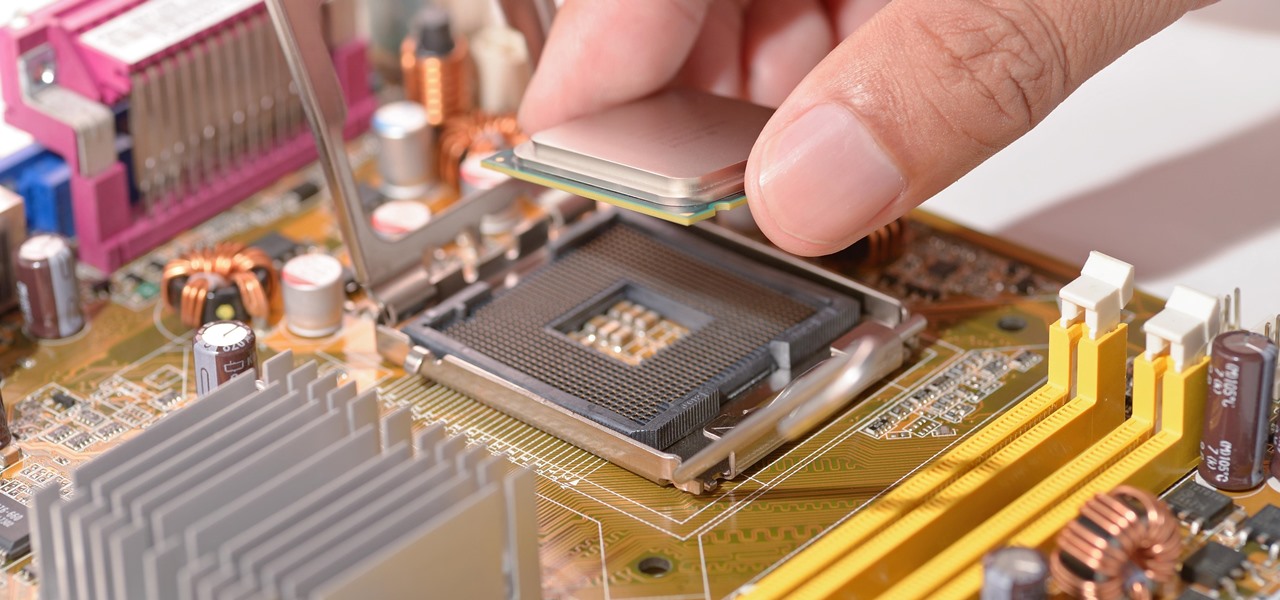
Intel Confirmed Critical Escalation of Privilege Vulnerability — Now What?
News:
Intel Confirmed Critical Escalation of Privilege Vulnerability — Now What?
 News:
How Governments Around the World Are Undermining Citizens' Privacy & Security to Stockpile Cyberweapons
News:
How Governments Around the World Are Undermining Citizens' Privacy & Security to Stockpile Cyberweapons
Next Page
Prev Page
Sites
- Hot
- Latest
-
 How To:
Create Packets from Scratch with Scapy for Scanning & DoSing
How To:
Create Packets from Scratch with Scapy for Scanning & DoSing
-
 How To:
Map Networks & Connect to Discovered Devices Using Your Phone
How To:
Map Networks & Connect to Discovered Devices Using Your Phone
-
 How To:
Wardrive on an Android Phone to Map Vulnerable Networks
How To:
Wardrive on an Android Phone to Map Vulnerable Networks
-
 How To:
Exploit Routers on an Unrooted Android Phone
How To:
Exploit Routers on an Unrooted Android Phone
-
 How To:
Steal macOS Files with the USB Rubber Ducky
How To:
Steal macOS Files with the USB Rubber Ducky
-
 Recon:
How to Research a Person or Organization Using the Operative Framework
Recon:
How to Research a Person or Organization Using the Operative Framework
-
 How To:
Buy the Best Wireless Network Adapter for Wi-Fi Hacking in 2019
How To:
Buy the Best Wireless Network Adapter for Wi-Fi Hacking in 2019
-
 How To:
Build a Pumpkin Pi — The Rogue AP & MITM Framework That Fits in Your Pocket
How To:
Build a Pumpkin Pi — The Rogue AP & MITM Framework That Fits in Your Pocket
-
 How To:
Boot Multiple Operating Systems on the Raspberry Pi with BerryBoot
How To:
Boot Multiple Operating Systems on the Raspberry Pi with BerryBoot
-
 How To:
Modify the USB Rubber Ducky with Custom Firmware
How To:
Modify the USB Rubber Ducky with Custom Firmware
-
 How To:
Scrape Target Email Addresses with TheHarvester
How To:
Scrape Target Email Addresses with TheHarvester
-
 How To:
Seize Control of a Router with RouterSploit
How To:
Seize Control of a Router with RouterSploit
-
 How To:
Wardrive with the Kali Raspberry Pi to Map Wi-Fi Devices
How To:
Wardrive with the Kali Raspberry Pi to Map Wi-Fi Devices
-
 How To:
Set Up a Practice Computer to Kill on a Raspberry Pi
How To:
Set Up a Practice Computer to Kill on a Raspberry Pi
-
 Social Engineering:
How to Use Persuasion to Compromise a Human Target
Social Engineering:
How to Use Persuasion to Compromise a Human Target
-
 How To:
Log Wi-Fi Probe Requests from Smartphones & Laptops with Probemon
How To:
Log Wi-Fi Probe Requests from Smartphones & Laptops with Probemon
-
 How To:
Automate Hacking on the Raspberry Pi with the USB Rubber Ducky
How To:
Automate Hacking on the Raspberry Pi with the USB Rubber Ducky
-
 How to Hack Radio Frequencies:
Hijacking FM Radio with a Raspberry Pi & Wire
How to Hack Radio Frequencies:
Hijacking FM Radio with a Raspberry Pi & Wire
-
 How to Hack Radio Frequencies:
Building a Radio Listening Station to Decode Digital Audio & Police Dispatches
How to Hack Radio Frequencies:
Building a Radio Listening Station to Decode Digital Audio & Police Dispatches
-
 How To:
Load & Use Keystroke Injection Payloads on the USB Rubber Ducky
How To:
Load & Use Keystroke Injection Payloads on the USB Rubber Ducky
-
 How To:
Scrape Target Email Addresses with TheHarvester
How To:
Scrape Target Email Addresses with TheHarvester
-
 How To:
Log Wi-Fi Probe Requests from Smartphones & Laptops with Probemon
How To:
Log Wi-Fi Probe Requests from Smartphones & Laptops with Probemon
-
 How To:
Set Up Kali Linux on the New $10 Raspberry Pi Zero W
How To:
Set Up Kali Linux on the New $10 Raspberry Pi Zero W
-
 How To:
Buy the Best Wireless Network Adapter for Wi-Fi Hacking in 2019
How To:
Buy the Best Wireless Network Adapter for Wi-Fi Hacking in 2019
-
 How To:
Wardrive with the Kali Raspberry Pi to Map Wi-Fi Devices
How To:
Wardrive with the Kali Raspberry Pi to Map Wi-Fi Devices
-
 How To:
Seize Control of a Router with RouterSploit
How To:
Seize Control of a Router with RouterSploit
-
 How To:
Set Up a Headless Raspberry Pi Hacking Platform Running Kali Linux
How To:
Set Up a Headless Raspberry Pi Hacking Platform Running Kali Linux
-
 How To:
Wardrive on an Android Phone to Map Vulnerable Networks
How To:
Wardrive on an Android Phone to Map Vulnerable Networks
-
 How To:
Build a Pumpkin Pi — The Rogue AP & MITM Framework That Fits in Your Pocket
How To:
Build a Pumpkin Pi — The Rogue AP & MITM Framework That Fits in Your Pocket
-
 How To:
Create Packets from Scratch with Scapy for Scanning & DoSing
How To:
Create Packets from Scratch with Scapy for Scanning & DoSing
-
 How To:
Boot Multiple Operating Systems on the Raspberry Pi with BerryBoot
How To:
Boot Multiple Operating Systems on the Raspberry Pi with BerryBoot
-
 How To:
Exploit Routers on an Unrooted Android Phone
How To:
Exploit Routers on an Unrooted Android Phone
-
 How To:
Steal macOS Files with the USB Rubber Ducky
How To:
Steal macOS Files with the USB Rubber Ducky
-
 How To:
Map Networks & Connect to Discovered Devices Using Your Phone
How To:
Map Networks & Connect to Discovered Devices Using Your Phone
-
 How To:
Automate Hacking on the Raspberry Pi with the USB Rubber Ducky
How To:
Automate Hacking on the Raspberry Pi with the USB Rubber Ducky
-
 How To:
Set Up a Practice Computer to Kill on a Raspberry Pi
How To:
Set Up a Practice Computer to Kill on a Raspberry Pi
-
 How to Hack Radio Frequencies:
Building a Radio Listening Station to Decode Digital Audio & Police Dispatches
How to Hack Radio Frequencies:
Building a Radio Listening Station to Decode Digital Audio & Police Dispatches
-
 How to Hack Radio Frequencies:
Hijacking FM Radio with a Raspberry Pi & Wire
How to Hack Radio Frequencies:
Hijacking FM Radio with a Raspberry Pi & Wire
-
 How To:
Modify the USB Rubber Ducky with Custom Firmware
How To:
Modify the USB Rubber Ducky with Custom Firmware
-
 How To:
Load & Use Keystroke Injection Payloads on the USB Rubber Ducky
How To:
Load & Use Keystroke Injection Payloads on the USB Rubber Ducky
-
 Recon:
How to Research a Person or Organization Using the Operative Framework
Recon:
How to Research a Person or Organization Using the Operative Framework
-
 Social Engineering:
How to Use Persuasion to Compromise a Human Target
Social Engineering:
How to Use Persuasion to Compromise a Human Target
-
 News:
Intel Confirmed Critical Escalation of Privilege Vulnerability — Now What?
News:
Intel Confirmed Critical Escalation of Privilege Vulnerability — Now What?
-
 News:
How Governments Around the World Are Undermining Citizens' Privacy & Security to Stockpile Cyberweapons
News:
How Governments Around the World Are Undermining Citizens' Privacy & Security to Stockpile Cyberweapons