About tokyoneon
Tokyoneon is a certified red team operator with over one-hundred offensive security publications as well as experience exploiting weaknesses in web applications and vulnerabilities in modern infrastructure. eCPPT / eWPTX / OSCP / OSWP / PenTest+ / CySA+ / Security+
- Website: twitter.com
tokyoneon's Latest Posts
 Hacking macOS:
How to Sniff Passwords on a Mac in Real Time, Part 1 (Packet Exfiltration)
Hacking macOS:
How to Sniff Passwords on a Mac in Real Time, Part 1 (Packet Exfiltration)
 How To:
Hack 200 Online User Accounts in Less Than 2 Hours (From Sites Like Twitter, Reddit & Microsoft)
How To:
Hack 200 Online User Accounts in Less Than 2 Hours (From Sites Like Twitter, Reddit & Microsoft)
 Locking Down Linux:
Using Ubuntu as Your Primary OS, Part 4 (Auditing, Antivirus & Monitoring)
Locking Down Linux:
Using Ubuntu as Your Primary OS, Part 4 (Auditing, Antivirus & Monitoring)
 Locking Down Linux:
Using Ubuntu as Your Primary OS, Part 3 (Application Hardening & Sandboxing)
Locking Down Linux:
Using Ubuntu as Your Primary OS, Part 3 (Application Hardening & Sandboxing)
 Locking Down Linux:
Using Ubuntu as Your Primary OS, Part 2 (Network Attack Defense)
Locking Down Linux:
Using Ubuntu as Your Primary OS, Part 2 (Network Attack Defense)
 Locking Down Linux:
Using Ubuntu as Your Primary OS, Part 1 (Physical Attack Defense)
Locking Down Linux:
Using Ubuntu as Your Primary OS, Part 1 (Physical Attack Defense)
 How To:
Hack WPA2 Wi-Fi Passwords Using Jedi Mind Tricks (& USB Dead Drops)
How To:
Hack WPA2 Wi-Fi Passwords Using Jedi Mind Tricks (& USB Dead Drops)
 Hacking macOS:
How to Dump Passwords Stored in Firefox Browsers Remotely
Hacking macOS:
How to Dump Passwords Stored in Firefox Browsers Remotely
 Hacking macOS:
How to Break into a MacBook Encrypted with FileVault
Hacking macOS:
How to Break into a MacBook Encrypted with FileVault
 Hacking macOS:
How to Use One Python Command to Bypass Antivirus Software in 5 Seconds
Hacking macOS:
How to Use One Python Command to Bypass Antivirus Software in 5 Seconds
 Hacking macOS:
How to Secretly Livestream Someone's MacBook Screen Remotely
Hacking macOS:
How to Secretly Livestream Someone's MacBook Screen Remotely
 Hacking Windows 10:
How to Create an Undetectable Payload, Part 2 (Concealing the Payload)
Hacking Windows 10:
How to Create an Undetectable Payload, Part 2 (Concealing the Payload)
 Hacking Windows 10:
How to Create an Undetectable Payload, Part 1 (Bypassing Antivirus Software)
Hacking Windows 10:
How to Create an Undetectable Payload, Part 1 (Bypassing Antivirus Software)
 Hacking macOS:
How to Remotely Eavesdrop in Real Time Using Anyone's MacBook Microphone
Hacking macOS:
How to Remotely Eavesdrop in Real Time Using Anyone's MacBook Microphone
 Hacking macOS:
How to Install a Persistent Empire Backdoor on a MacBook
Hacking macOS:
How to Install a Persistent Empire Backdoor on a MacBook
 Hacking macOS:
How to Create a Fake PDF Trojan with AppleScript, Part 2 (Disguising the Script)
Hacking macOS:
How to Create a Fake PDF Trojan with AppleScript, Part 2 (Disguising the Script)
 Hacking macOS:
How to Create a Fake PDF Trojan with AppleScript, Part 1 (Creating the Stager)
Hacking macOS:
How to Create a Fake PDF Trojan with AppleScript, Part 1 (Creating the Stager)
 Hacking macOS:
How to Connect to MacBook Backdoors from Anywhere in the World
Hacking macOS:
How to Connect to MacBook Backdoors from Anywhere in the World
 Hacking macOS:
How to Configure a Backdoor on Anyone's MacBook
Hacking macOS:
How to Configure a Backdoor on Anyone's MacBook
 Hacking Windows 10:
How to Intercept & Decrypt Windows Passwords on a Local Network
Hacking Windows 10:
How to Intercept & Decrypt Windows Passwords on a Local Network
 How To:
Quickly Look Up the Valid Subdomains for Any Website
How To:
Quickly Look Up the Valid Subdomains for Any Website
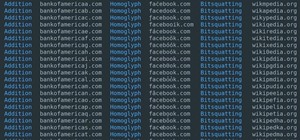
 How To:
Easily Generate Hundreds of Phishing Domains
How To:
Easily Generate Hundreds of Phishing Domains
 Hacking Windows 10:
How to Remotely Record & Listen to the Microphone of a Hacked Computer
Hacking Windows 10:
How to Remotely Record & Listen to the Microphone of a Hacked Computer
 How To:
Automate Brute-Force Attacks for Nmap Scans
How To:
Automate Brute-Force Attacks for Nmap Scans
 How To:
Use Leaked Password Databases to Create Brute-Force Wordlists
How To:
Use Leaked Password Databases to Create Brute-Force Wordlists
 Hacking Windows 10:
How to Capture Keystrokes & Passwords Remotely
Hacking Windows 10:
How to Capture Keystrokes & Passwords Remotely
 Hacking Windows 10:
How to Find Sensitive & 'Deleted' Files Remotely
Hacking Windows 10:
How to Find Sensitive & 'Deleted' Files Remotely
 Hacking Windows 10:
How to Capture & Exfiltrate Screenshots Remotely
Hacking Windows 10:
How to Capture & Exfiltrate Screenshots Remotely
 Hacking Windows 10:
How to Steal & Decrypt Passwords Stored in Chrome & Firefox Remotely
Hacking Windows 10:
How to Steal & Decrypt Passwords Stored in Chrome & Firefox Remotely
 Hacking Windows 10:
How to Break into Somebody's Computer Without a Password (Exploiting the System)
Hacking Windows 10:
How to Break into Somebody's Computer Without a Password (Exploiting the System)
 Hacking Windows 10:
How to Break into Somebody's Computer Without a Password (Setting Up the Payload)
Hacking Windows 10:
How to Break into Somebody's Computer Without a Password (Setting Up the Payload)
 How To:
Stealthfully Sniff Wi-Fi Activity Without Connecting to a Target Router
How To:
Stealthfully Sniff Wi-Fi Activity Without Connecting to a Target Router
 How To:
The White Hat's Guide to Choosing a Virtual Private Server
How To:
The White Hat's Guide to Choosing a Virtual Private Server
 How To:
Hack Anyone's Wi-Fi Password Using a Birthday Card, Part 2 (Executing the Attack)
How To:
Hack Anyone's Wi-Fi Password Using a Birthday Card, Part 2 (Executing the Attack)
 How To:
Hack Anyone's Wi-Fi Password Using a Birthday Card, Part 1 (Creating the Payload)
How To:
Hack Anyone's Wi-Fi Password Using a Birthday Card, Part 1 (Creating the Payload)
 How To:
Hack Your Neighbor with a Post-It Note, Part 3 (Executing the Attack)
How To:
Hack Your Neighbor with a Post-It Note, Part 3 (Executing the Attack)
 How To:
Hack Your Neighbor with a Post-It Note, Part 2 (Setting Up the Attack)
How To:
Hack Your Neighbor with a Post-It Note, Part 2 (Setting Up the Attack)
 How To:
Hack Your Neighbor with a Post-It Note, Part 1 (Performing Recon)
How To:
Hack Your Neighbor with a Post-It Note, Part 1 (Performing Recon)
 How To:
Inject Coinhive Miners into Public Wi-Fi Hotspots
How To:
Inject Coinhive Miners into Public Wi-Fi Hotspots
Sites
- Hot
- Latest
-
 Hacking Windows 10:
How to Bypass VirusTotal & AMSI Detection Signatures with Chimera
Hacking Windows 10:
How to Bypass VirusTotal & AMSI Detection Signatures with Chimera
-
 Hacking Windows 10:
How to Evade Detection of Netstat & Tasklist
Hacking Windows 10:
How to Evade Detection of Netstat & Tasklist
-
 Hacking macOS:
How to Identify Antivirus & Firewall Software Installed on Someone's MacBook
Hacking macOS:
How to Identify Antivirus & Firewall Software Installed on Someone's MacBook
-
 Hacking iOS:
How to Embed Payloads into iPhone Packages with Arcane
Hacking iOS:
How to Embed Payloads into iPhone Packages with Arcane
-
 How To:
Identify Antivirus Software Installed on a Target's Windows 10 PC
How To:
Identify Antivirus Software Installed on a Target's Windows 10 PC
-
 Hacking Windows 10:
How to Use SSH Tunnels to Forward Requests & Hack Remote Routers
Hacking Windows 10:
How to Use SSH Tunnels to Forward Requests & Hack Remote Routers
-
 Hacking macOS:
How to Turn Forums into C&C Servers to Control MacBooks
Hacking macOS:
How to Turn Forums into C&C Servers to Control MacBooks
-
 Hacking Windows 10:
How to Hack uTorrent Clients & Backdoor the Operating System
Hacking Windows 10:
How to Hack uTorrent Clients & Backdoor the Operating System
-
 How To:
Break into Router Gateways with Patator
How To:
Break into Router Gateways with Patator
-
 Hacking Windows 10:
How to Dump NTLM Hashes & Crack Windows Passwords
Hacking Windows 10:
How to Dump NTLM Hashes & Crack Windows Passwords
-
 How To:
Pop a Reverse Shell with a Video File by Exploiting Popular Linux File Managers
How To:
Pop a Reverse Shell with a Video File by Exploiting Popular Linux File Managers
-
 How To:
Perform Network-Based Attacks with an SBC Implant
How To:
Perform Network-Based Attacks with an SBC Implant
-
 How To:
Set Up Network Implants with a Cheap SBC (Single-Board Computer)
How To:
Set Up Network Implants with a Cheap SBC (Single-Board Computer)
-
 Hacking macOS:
How to Use Images to Smuggle Data Through Firewalls
Hacking macOS:
How to Use Images to Smuggle Data Through Firewalls
-
 How To:
Use Microsoft.com Domains to Bypass Firewalls & Execute Payloads
How To:
Use Microsoft.com Domains to Bypass Firewalls & Execute Payloads
-
 Hacking macOS:
How to Bypass the LuLu Firewall with Google Chrome Dependencies
Hacking macOS:
How to Bypass the LuLu Firewall with Google Chrome Dependencies
-
 Hacking macOS:
How to Dump 1Password, KeePassX & LastPass Passwords in Plaintext
Hacking macOS:
How to Dump 1Password, KeePassX & LastPass Passwords in Plaintext
-
 Hacking Windows 10:
How to Turn Compromised Windows PCs into Web Proxies
Hacking Windows 10:
How to Turn Compromised Windows PCs into Web Proxies
-
 How To:
Bypass Gatekeeper & Exploit macOS 10.14.5 & Earlier
How To:
Bypass Gatekeeper & Exploit macOS 10.14.5 & Earlier
-
 How To:
Inject Keystrokes into Logitech Keyboards with an nRF24LU1+ Transceiver
How To:
Inject Keystrokes into Logitech Keyboards with an nRF24LU1+ Transceiver
-
 How To:
Easily Detect CVEs with Nmap Scripts
How To:
Easily Detect CVEs with Nmap Scripts
-
 Hacking Windows 10:
How to Create an Undetectable Payload, Part 2 (Concealing the Payload)
Hacking Windows 10:
How to Create an Undetectable Payload, Part 2 (Concealing the Payload)
-
 Hacking Windows 10:
How to Dump NTLM Hashes & Crack Windows Passwords
Hacking Windows 10:
How to Dump NTLM Hashes & Crack Windows Passwords
-
 How To:
Stealthfully Sniff Wi-Fi Activity Without Connecting to a Target Router
How To:
Stealthfully Sniff Wi-Fi Activity Without Connecting to a Target Router
-
 Hacking macOS:
How to Create an Undetectable Payload
Hacking macOS:
How to Create an Undetectable Payload
-
 Hacking Windows 10:
How to Bypass VirusTotal & AMSI Detection Signatures with Chimera
Hacking Windows 10:
How to Bypass VirusTotal & AMSI Detection Signatures with Chimera
-
 How To:
Inject Keystrokes into Logitech Keyboards with an nRF24LU1+ Transceiver
How To:
Inject Keystrokes into Logitech Keyboards with an nRF24LU1+ Transceiver
-
 How To:
Automate Brute-Force Attacks for Nmap Scans
How To:
Automate Brute-Force Attacks for Nmap Scans
-
 Hacking macOS:
How to Hack a Mac Password Without Changing It
Hacking macOS:
How to Hack a Mac Password Without Changing It
-
 How To:
Easily Generate Hundreds of Phishing Domains
How To:
Easily Generate Hundreds of Phishing Domains
-
 Android for Hackers:
How to Exfiltrate WPA2 Wi-Fi Passwords Using Android & PowerShell
Android for Hackers:
How to Exfiltrate WPA2 Wi-Fi Passwords Using Android & PowerShell
-
 How To:
Break into Router Gateways with Patator
How To:
Break into Router Gateways with Patator
-
 Hacking Windows 10:
How to Create an Undetectable Payload, Part 1 (Bypassing Antivirus Software)
Hacking Windows 10:
How to Create an Undetectable Payload, Part 1 (Bypassing Antivirus Software)
-
 How To:
Pop a Reverse Shell with a Video File by Exploiting Popular Linux File Managers
How To:
Pop a Reverse Shell with a Video File by Exploiting Popular Linux File Managers
-
 Hacking iOS:
How to Embed Payloads into iPhone Packages with Arcane
Hacking iOS:
How to Embed Payloads into iPhone Packages with Arcane
-
 How To:
Inject Coinhive Miners into Public Wi-Fi Hotspots
How To:
Inject Coinhive Miners into Public Wi-Fi Hotspots
-
 Hacking macOS:
How to Break into a MacBook Encrypted with FileVault
Hacking macOS:
How to Break into a MacBook Encrypted with FileVault
-
 Android for Hackers:
How to Backdoor Windows 10 Using an Android Phone & USB Rubber Ducky
Android for Hackers:
How to Backdoor Windows 10 Using an Android Phone & USB Rubber Ducky
-
 Hacking macOS:
How to Create a Fake PDF Trojan with AppleScript, Part 1 (Creating the Stager)
Hacking macOS:
How to Create a Fake PDF Trojan with AppleScript, Part 1 (Creating the Stager)
-
 Hacking macOS:
How to Configure a Backdoor on Anyone's MacBook
Hacking macOS:
How to Configure a Backdoor on Anyone's MacBook
-
 Hacking Windows 10:
How to Break into Somebody's Computer Without a Password (Setting Up the Payload)
Hacking Windows 10:
How to Break into Somebody's Computer Without a Password (Setting Up the Payload)
-
 How To:
Steal Ubuntu & MacOS Sudo Passwords Without Any Cracking
How To:
Steal Ubuntu & MacOS Sudo Passwords Without Any Cracking
-
 How To:
Use Leaked Password Databases to Create Brute-Force Wordlists
How To:
Use Leaked Password Databases to Create Brute-Force Wordlists
-
 How To:
Hack Anyone's Wi-Fi Password Using a Birthday Card, Part 1 (Creating the Payload)
How To:
Hack Anyone's Wi-Fi Password Using a Birthday Card, Part 1 (Creating the Payload)
-
 Hacking macOS:
How to Bypass Mojave's Elevated Privileges Prompt by Pretending to Be a Trusted App
Hacking macOS:
How to Bypass Mojave's Elevated Privileges Prompt by Pretending to Be a Trusted App
-
 Hacking macOS:
How to Remotely Eavesdrop in Real Time Using Anyone's MacBook Microphone
Hacking macOS:
How to Remotely Eavesdrop in Real Time Using Anyone's MacBook Microphone
-
 Hacking macOS:
How to Dump 1Password, KeePassX & LastPass Passwords in Plaintext
Hacking macOS:
How to Dump 1Password, KeePassX & LastPass Passwords in Plaintext
-
 Hacking Windows 10:
How to Remotely Record & Listen to the Microphone of a Hacked Computer
Hacking Windows 10:
How to Remotely Record & Listen to the Microphone of a Hacked Computer
-
 How To:
Use Microsoft.com Domains to Bypass Firewalls & Execute Payloads
How To:
Use Microsoft.com Domains to Bypass Firewalls & Execute Payloads
-
 Locking Down Linux:
Using Ubuntu as Your Primary OS, Part 4 (Auditing, Antivirus & Monitoring)
Locking Down Linux:
Using Ubuntu as Your Primary OS, Part 4 (Auditing, Antivirus & Monitoring)
-
 Hacking macOS:
How to Sniff Passwords on a Mac in Real Time, Part 2 (Packet Analysis)
Hacking macOS:
How to Sniff Passwords on a Mac in Real Time, Part 2 (Packet Analysis)
-
 Hacking Windows 10:
How to Steal & Decrypt Passwords Stored in Chrome & Firefox Remotely
Hacking Windows 10:
How to Steal & Decrypt Passwords Stored in Chrome & Firefox Remotely
-
 How To:
The Ultimate Guide to Hacking macOS
How To:
The Ultimate Guide to Hacking macOS
-
 Hacking macOS:
How to Create a Fake PDF Trojan with AppleScript, Part 2 (Disguising the Script)
Hacking macOS:
How to Create a Fake PDF Trojan with AppleScript, Part 2 (Disguising the Script)
-
 Android for Hackers:
How to Backdoor Windows 10 & Livestream the Desktop (Without RDP)
Android for Hackers:
How to Backdoor Windows 10 & Livestream the Desktop (Without RDP)
-
 Hacking macOS:
How to Secretly Livestream Someone's MacBook Screen Remotely
Hacking macOS:
How to Secretly Livestream Someone's MacBook Screen Remotely
-
 Hacking macOS:
How to Connect to MacBook Backdoors from Anywhere in the World
Hacking macOS:
How to Connect to MacBook Backdoors from Anywhere in the World
-
 Hacking Windows 10:
How to Break into Somebody's Computer Without a Password (Exploiting the System)
Hacking Windows 10:
How to Break into Somebody's Computer Without a Password (Exploiting the System)
-
 How To:
The White Hat's Guide to Choosing a Virtual Private Server
How To:
The White Hat's Guide to Choosing a Virtual Private Server
-
 Locking Down Linux:
Using Ubuntu as Your Primary OS, Part 1 (Physical Attack Defense)
Locking Down Linux:
Using Ubuntu as Your Primary OS, Part 1 (Physical Attack Defense)