Hot Posts

How To: The Messaging Trick You Never Knew You Needed
Whether you're wielding an iPhone, iPad, Mac, Android phone or tablet, or even a Windows PC, this little-known secret holds the key to effortless assistance and unwavering obedience. Intrigued? I thought so.
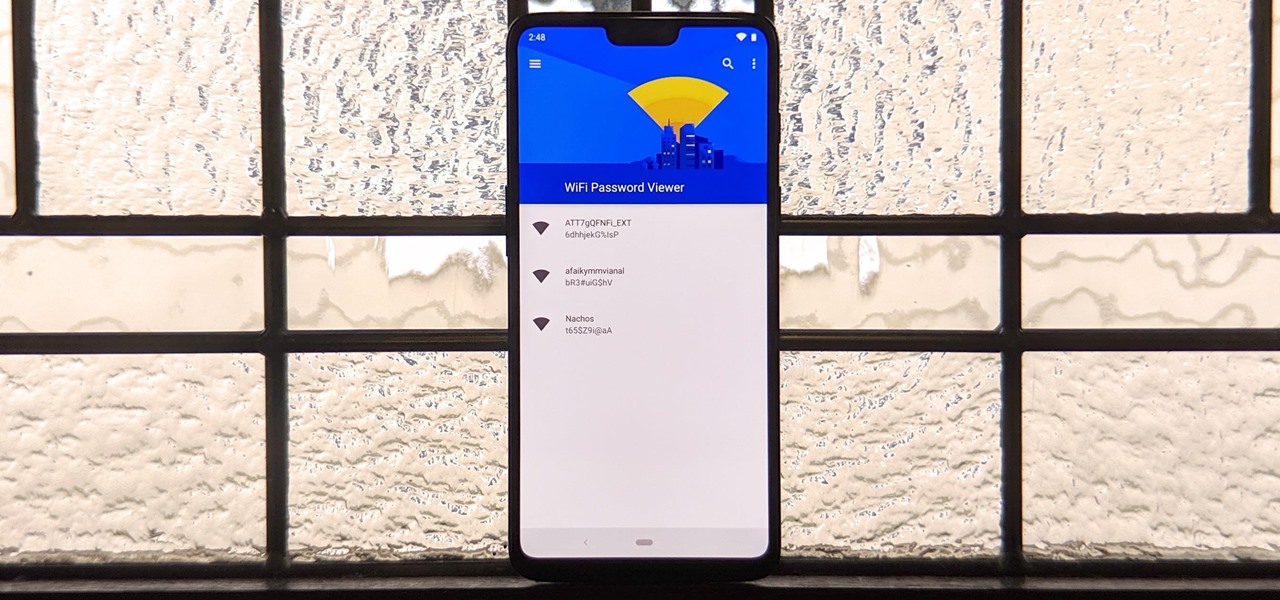
How To: See Passwords for Wi-Fi Networks You've Connected Your Android Device To
You've probably connected your Android device to dozens of Wi-Fi networks since you've had it, and your phone or tablet remembers each of them. Whether it's a hotspot at home, school, work, the gym, a coffee shop, a relative's apartment — or even from a friend's phone — each time you type in a Wi-Fi password, your Android device saves it for safekeeping and easy access later.

How To: Dox Anyone
Doxing is the act of finding one's personal information through research and discovery, with little to no information to start with. You may have seen doxing in the news, for instance when not so long ago, hacker team Anonymous doxed and reported thousands of twitter accounts related to ISIS. Doxing can be useful for finding the address of a coworker, or simply investigating people on the internet. The tutorial I will provide to you now will teach you the basics of doxing and how you can prot...

How To: Use FaceTime's Secret Hand Gestures and Reaction Buttons to Add Animated On-Screen Effects to Your Video Feed
Apple's Messages app has long had visual effects you could apply manually after long-pressing the send button, and there are even hidden keywords you could use to trigger full-screen effects automatically. FaceTime's latest update also gives you some full-screen effects to play around with during video calls, but the triggers are an entirely different concept — hand gestures.

How To: Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
One of the best ways to dig into a website and look for vulnerabilities is by using a proxy. By routing traffic through a proxy like Burp Suite, you can discover hidden flaws quickly, but sometimes it's a pain to turn it on and off manually. Luckily, there is a browser add-on called FoxyProxy that automates this process with a single click of a button.

How To: Find Vulnerable Webcams Across the Globe Using Shodan
Search engines index websites on the web so you can find them more efficiently, and the same is true for internet-connected devices. Shodan indexes devices like webcams, printers, and even industrial controls into one easy-to-search database, giving hackers access to vulnerable devices online across the globe. And you can search its database via its website or command-line library.

How To: Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
Microsoft Office files can be password-protected in order to prevent tampering and ensure data integrity. But password-protected documents from earlier versions of Office are susceptible to having their hashes extracted with a simple program called office2john. Those extracted hashes can then be cracked using John the Ripper and Hashcat.
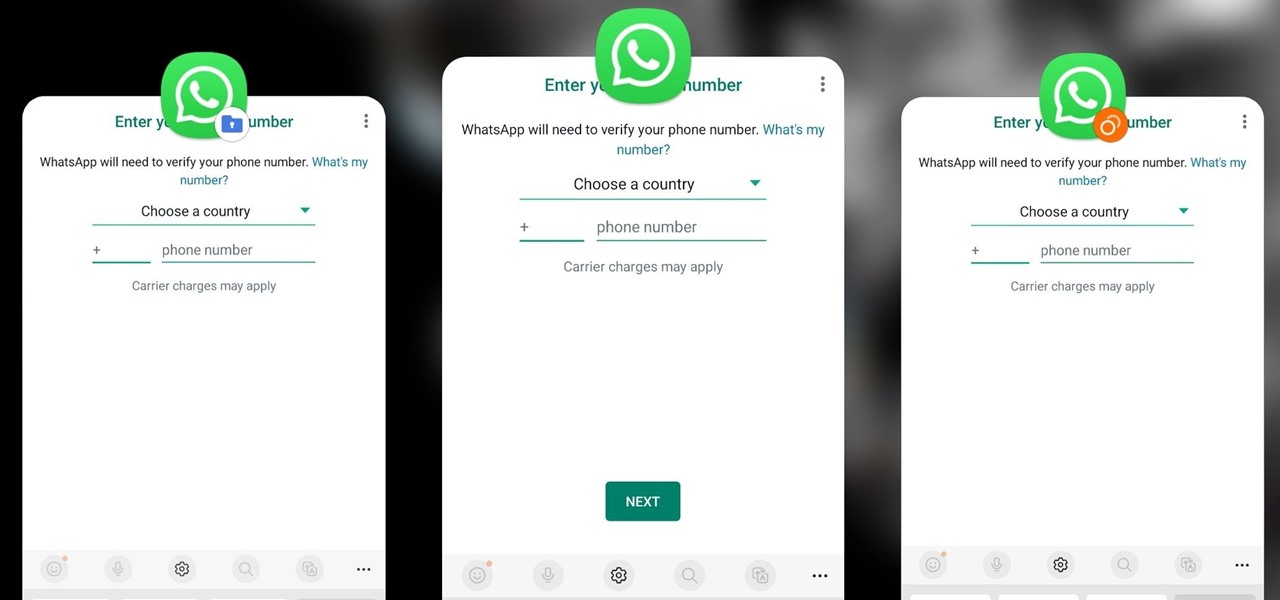
How To: Clone Any Android App on Your Samsung Galaxy Phone Without Using Any Third-Party Tools
Samsung has a cool security feature built into One UI that has an interesting side effect, one that lets you have two separate copies of any Android app on your Galaxy phone. And that's not the only integrated Samsung tool for cloning apps.

How To: Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
To hack a Wi-Fi network, you need your wireless card to support monitor mode and packet injection. Not all wireless cards can do this, but you can quickly test one you already own for compatibility, and you can verify that the chipset inside an adapter you're thinking of purchasing will work for Wi-Fi hacking.
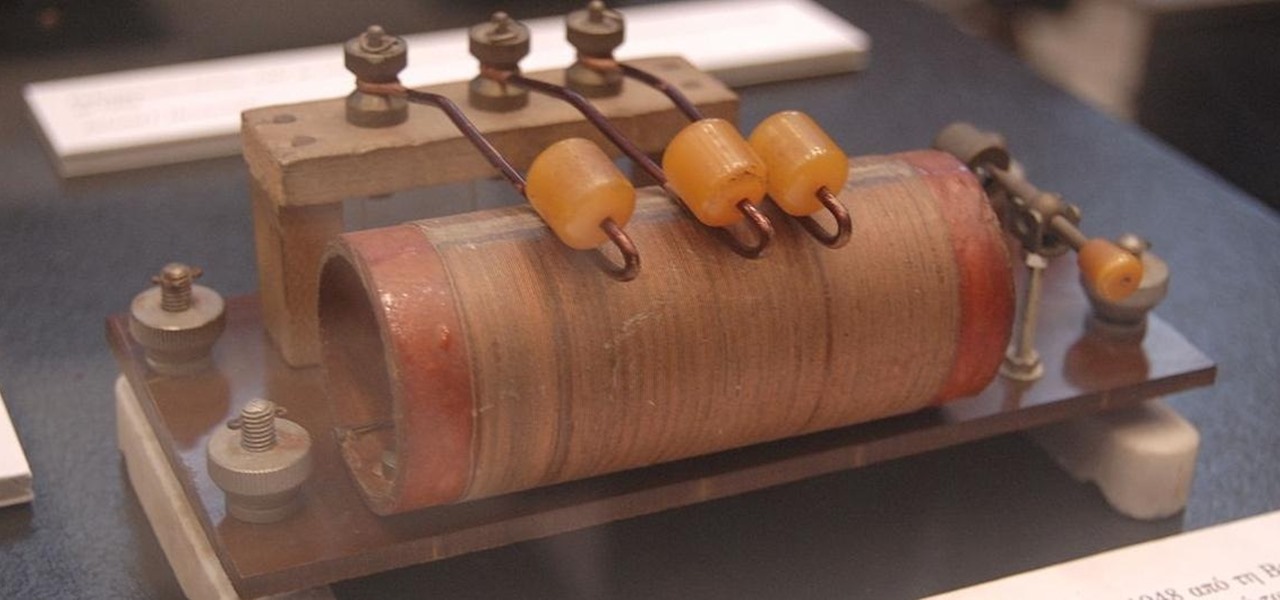
How To: The Complete Guide on How to Build a Crystal Radio—Plus How They Work
There's a lot that goes into making a nice crystal radio set, so this is going to have to be broken down into two parts. The first part is the actual making of a functional radio, and the second part is making the whole arrangement look nice. In this part, I'm actually going to tell you more than just how to make a crystal radio, but I'm also going to explain how and why they work. Crystal radios are pretty Steampunk in and of themselves, since they were first developed in the late 19th centu...

BT Recon: How to Snoop on Bluetooth Devices Using Kali Linux
While many people may use Bluetooth every day, the majority don't know how it works or that it can be hacked. Bluetooth hacking gives a clear window into the world of the target. Nearly every device has Bluetooth capabilities, and people store a great deal of personal info on their phones and tablets. Hack their Bluetooth connection, and you may be able to access all of that data.
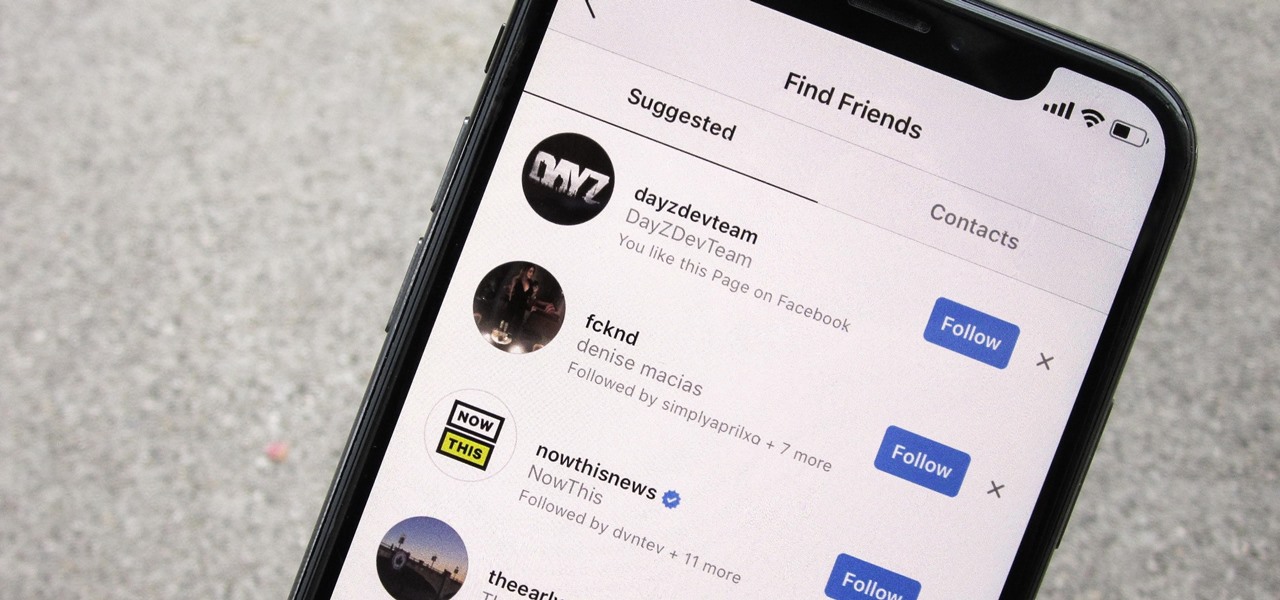
How To: Prevent People Who Have Your Contact Information from Finding Your Instagram Account
Sharing your personal information can come up for any number of reasons: you may want to get in touch with a colleague after work or you've been involved in a car accident and need to stay in contact with the other driver. Unfortunately, giving out information can be the key for others to find your social media accounts, such as Instagram, whether you want it to happen or not.

How to Hack Wi-Fi: Cracking WPA2 Passwords Using the New PMKID Hashcat Attack
Cracking the password for WPA2 networks has been roughly the same for many years, but a newer attack requires less interaction and info than previous techniques and has the added advantage of being able to target access points with no one connected. The latest attack against the PMKID uses Hashcat to crack WPA passwords and allows hackers to find networks with weak passwords more easily.
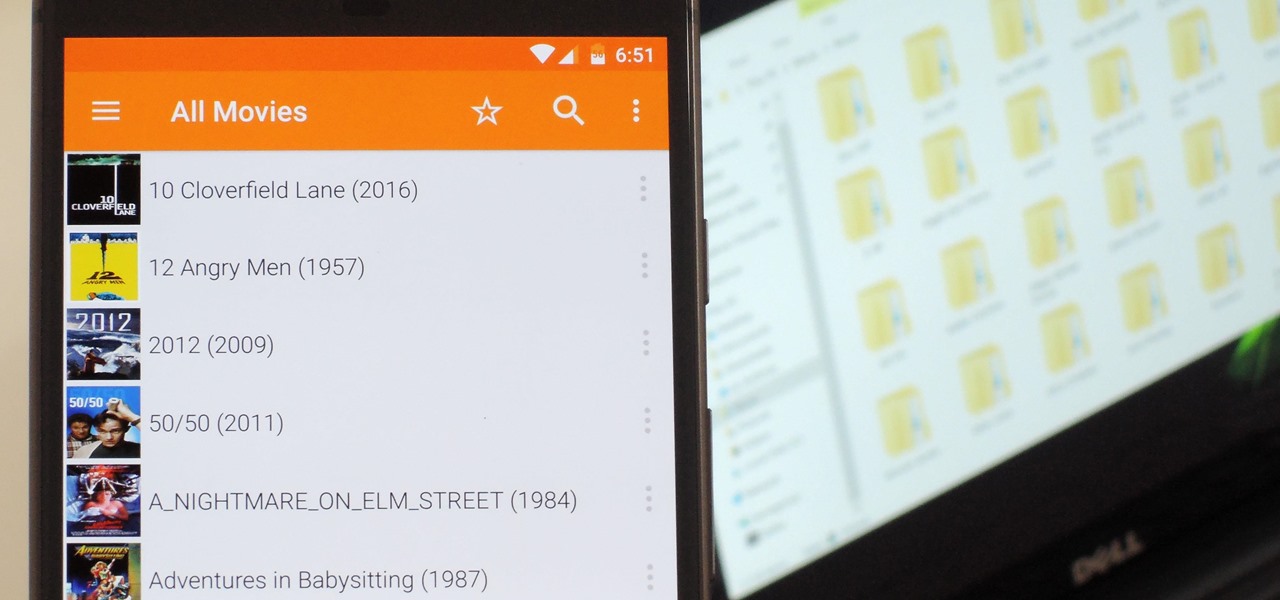
VLC 101: How to Stream Movies from Your Computer to Your Android Phone
Even though your phone has a built-in media player, it's got nothing on VLC. The popular third-party video player supports virtually every codec and file format, and even better, you can use it to stream movies, shows, and other video files from your computer to your phone.

How To: Find Out Whether Your Phone Has an LCD or AMOLED Display (& Why It Matters)
When it comes to smartphone screens, there are two predominant technologies—the traditional LCD panel, and the newer AMOLED display. Most phones still use LCD screens, as the tech is more cost-effective due to its longstanding reign as the primary display type in TVs, smartphones, and tablets.

How To: Create an Admin User Account Using CMD Prompt (Windows)
This is a quick tutorial on how to create a new administrator account on a Windows computer. Step 1: Open CMD Prompt...
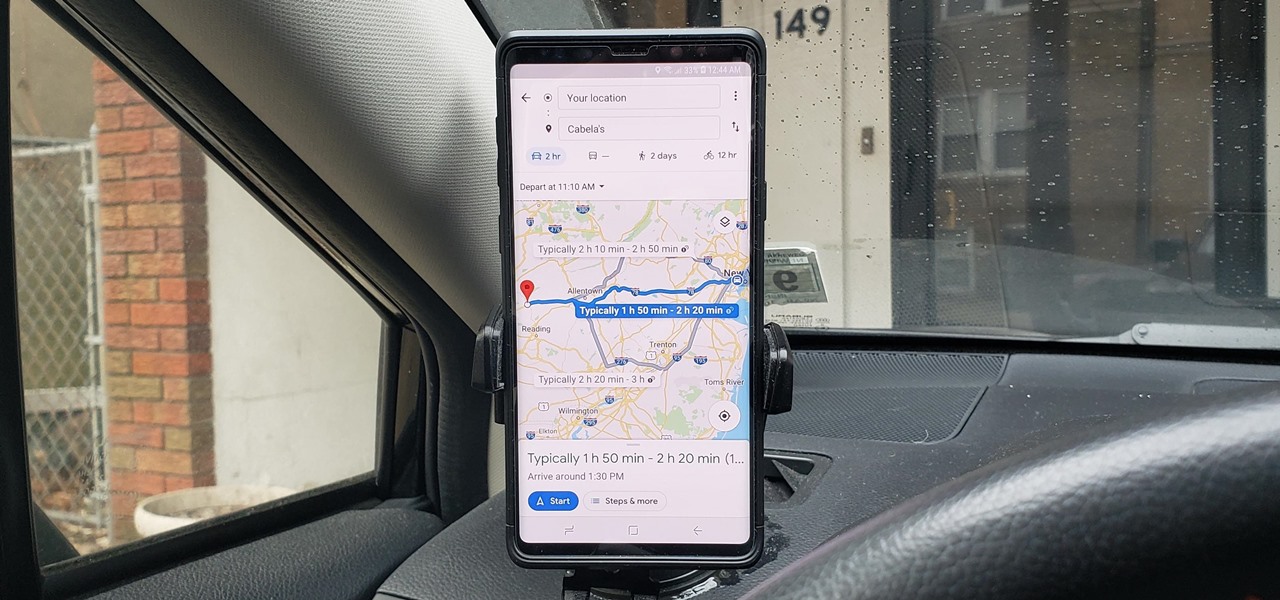
How To: See What Traffic Will Be Like at a Specific Time with Google Maps
As intuitive as Google Maps is for finding the best routes, it never let you choose departure and arrival times in the mobile app. This feature has long been available on the desktop site, allowing you to see what traffic should be like at a certain time and how long your drive would take at a point in the future. Fortunately, Google has finally added this feature to the app for iPhone and Android.

How To: Exploit EternalBlue on Windows Server with Metasploit
Particular vulnerabilities and exploits come along and make headlines with their catchy names and impressive potential for damage. EternalBlue is one of those exploits. Originally tied to the NSA, this zero-day exploited a flaw in the SMB protocol, affecting many Windows machines and wreaking havoc everywhere. Here, we will use EternalBlue to exploit SMB via Metasploit.

How To: Gain SSH Access to Servers by Brute-Forcing Credentials
SSH is one of the most common protocols in use in modern IT infrastructures, and because of this, it can be a valuable attack vector for hackers. One of the most reliable ways to gain SSH access to servers is by brute-forcing credentials. There are a few methods of performing an SSH brute-force attack that will ultimately lead to the discovery of valid login credentials.
Android Basics: How to See What Kind of Processor You Have (ARM, ARM64, or x86)
Starting with the release of Android Lollipop, the process of installing the Xposed Framework got a bit more complicated. Not only are there separate installers for each Android version, but now, you also need to know exactly what type of processor is in your device to make sure you're downloading the right files. In fact, CPU architecture is becoming a factor in more and more scenarios these days, including certain sideloaded app updates and, of course, custom ROMs.

How To: 13 Tips Every Apple Pencil User Needs to Know for iPad
While it doesn't come with any iPad models out of the box, the Apple Pencil is perhaps the best iPad accessory you can get. It's a powerful writing and drawing tool with an intuitive design and user-friendliness that makes it easy to take notes, draw sketches, mark up documents, and more. And there's a lot you can do with it — some of which you may not have noticed yet.

How To: Make Perfectly Circular McMuffin-Style Eggs Without Special Tools
We like our Egg McMuffins around here, albeit homemade with our preferred ingredients: whole wheat (or homemade sourdough) English muffins, a slice of thick Tillamook cheddar cheese, a meat, perhaps, like Canadian bacon, and finally—that perfectly-fried, perfectly-shaped egg.

How To: Uninstall Bloatware Without Root or a PC Using Android's New 'Wireless Debugging' Feature
Bloatware is a problem on Android, and it's not just a Samsung thing. Removing apps that have the Uninstall or Disable button grayed out in Settings has always involved sending ADB commands to your phone from a computer, which itself was always such a pain to set up. Thankfully, that has finally changed.

How To: Make Spoofed Calls Using Any Phone Number You Want Right from Your Smartphone
Spoofed phone calls originate from one source that's disguising its phone number as a different one, and you probably get these calls all the time. Maybe they're numbers from your local area code or for prominent businesses, but the callers are just hijacking those digits to fool you into picking up. Turns out, making a spoofed call is something anybody can do — even you.
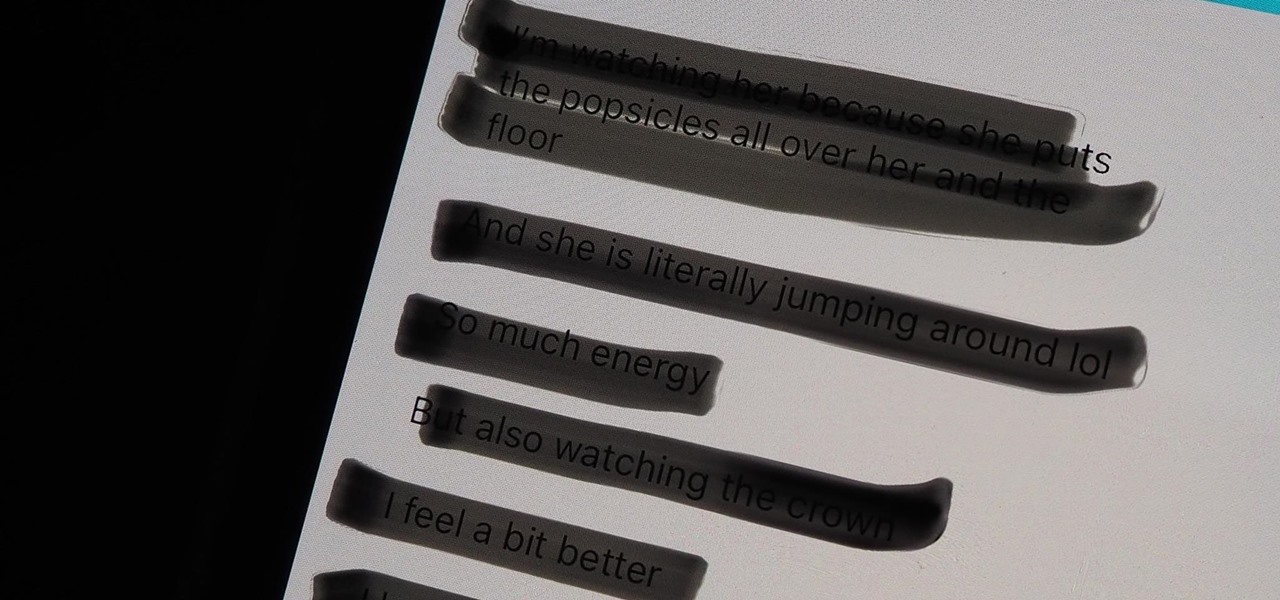
Warning: Sensitive Info You Black Out in Images Can Be Revealed with a Few Quick Edits on Your iPhone
These days, most images we post online or share with others come from our smartphones. Whenever personal data is in them, such as debit card numbers, addresses, phone numbers, passwords, and other sensitive information, it's easy to jump into your iPhone's markup tools to black out the text before sharing. But a digital marker may not hide everything.

How To: Crack SSH Private Key Passwords with John the Ripper
Secure Shell is one of the most common network protocols, typically used to manage remote machines through an encrypted connection. However, SSH is prone to password brute-forcing. Key-based authentication is much more secure, and private keys can even be encrypted for additional security. But even that isn't bulletproof since SSH private key passwords can be cracked using John the Ripper.

How To: Make Siri Say Whatever You Want Every Time You Connect Your iPhone to a Charger
Whenever your iPhone's ringer is on, you'll hear Apple's iconic "Connect Power" chime every time you connect it to a wired or wireless power source, which lets you know that charging has started. There's no way to disable the sound without turning on Silent mode, but there is a way to make Siri automatically say whatever you want after a successful connection.

How To: Crack Shadow Hashes After Getting Root on a Linux System
After gaining access to a root account, the next order of business is using that power to do something more significant. If the user passwords on the system can be obtained and cracked, an attacker can use them to pivot to other machines if the login is the same across systems. There are two tried-and-true password cracking tools that can accomplish this: John the Ripper and Hashcat.

How To: Make Your Own Bad USB
Hello, everyone! Many of you don't even know about my existence here on Null Byte, so I thought of contributing something rather interesting. Recently, someone asked how to make your own "Bad USB," and I promised to make a how-to on this topic. In addition, it would be nice to have something related on our WonderHowTo world. So here it is!
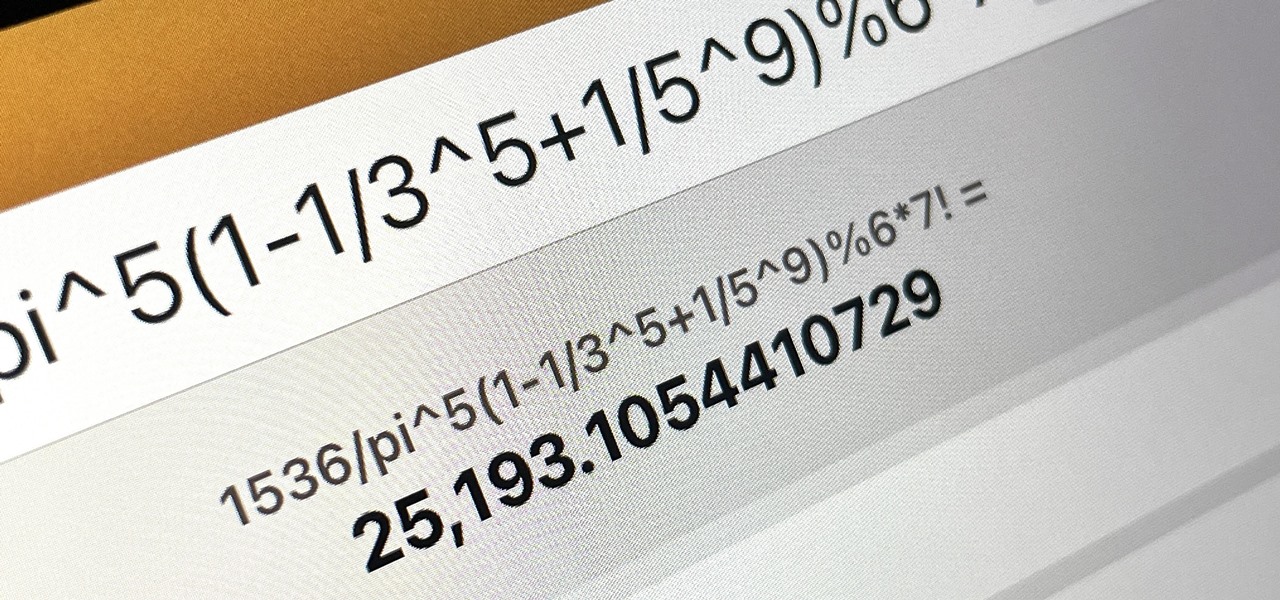
How To: Your iPad Has a Hidden Built-in Calculator You're Not Using — Here's How to Unlock It
There is no iPad version of Apple's Calculator app, so you won't find it on your Home Screen, in your App Library, or as a shortcut in the Control Center. But that doesn't mean your iPad doesn't have an official calculator.
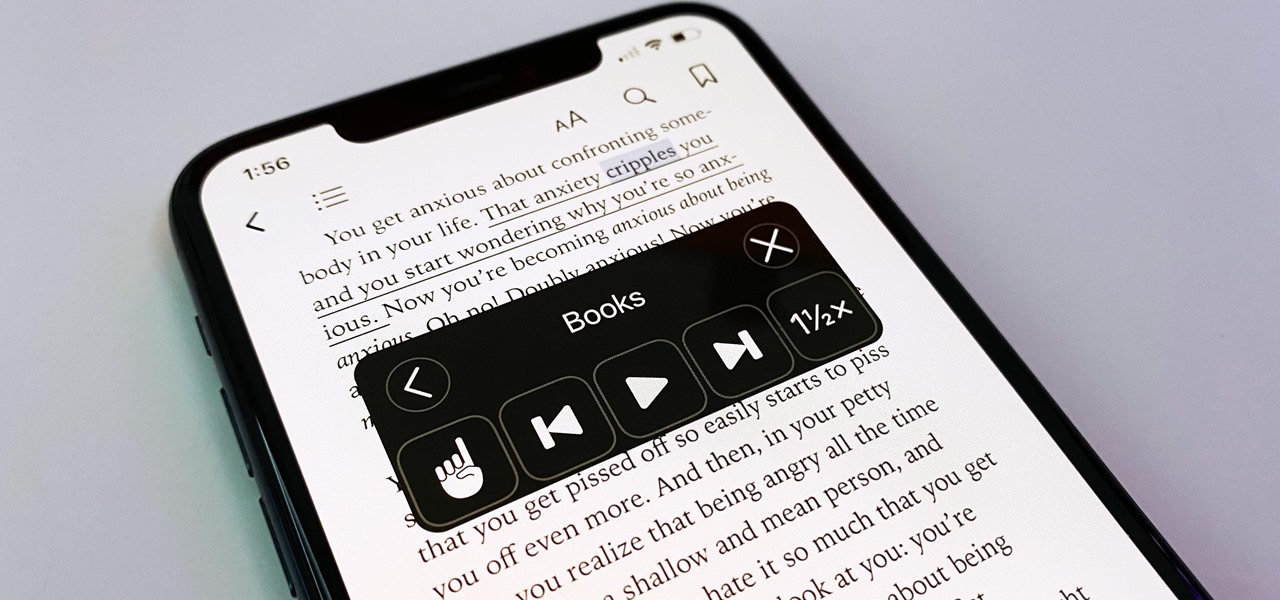
How To: Your iPhone Has a Hidden Text-to-Speech Tool That'll Read Articles, Books, News, and Other Text Out Loud to You
You may prefer reading news stories, web articles, and books on your iPhone over listening to them in spoken form. Still, sometimes it's necessary when driving, walking, cycling, cleaning, working, or performing other activities requiring a little multitasking. To help you out, Apple has a text-to-speech service on your iPhone — you just need to know how to find and set it up.
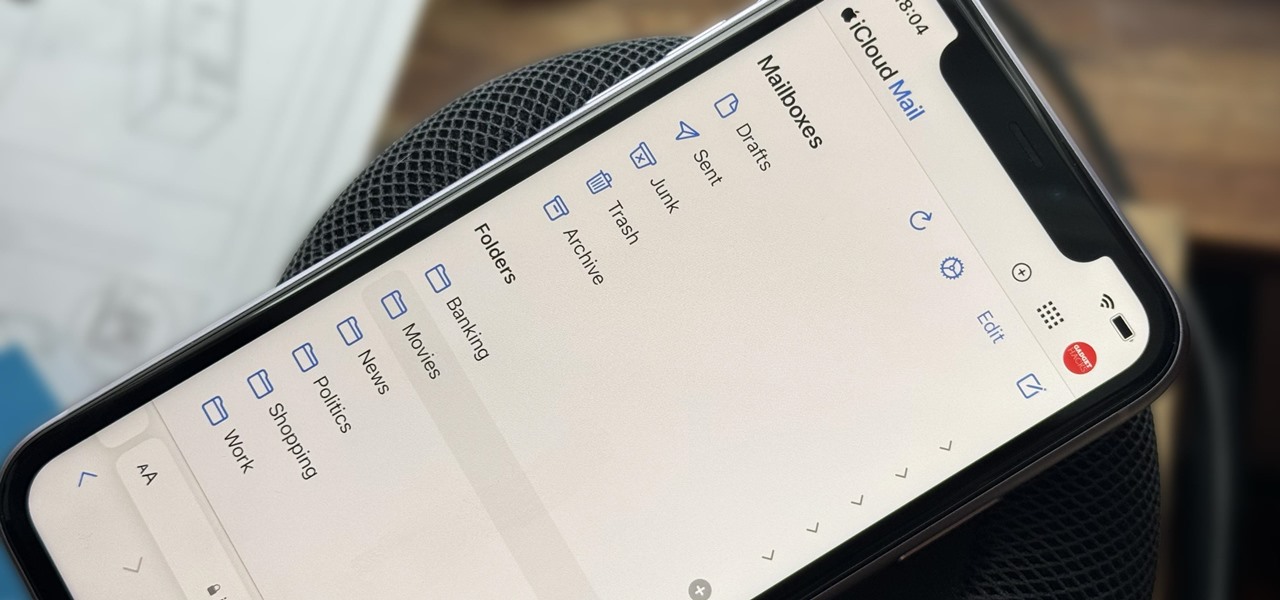
How To: Create Unlimited iCloud Email Address Variations to Take Total Control Over Your iCloud Mail Inbox
Apple includes a lot of helpful features for iCloud email addresses, but one of its best-kept secrets will give you total control over organizing your inbox like a pro.

How To: Create the Most Compact 2x2 Hidden Piston Door in Under 50 Seconds!
Every once in a while, Minecrafters want to create a simple hidden piston door to secretly hide all their valuable items. Now, it's possible with only 18 redstone, 2 repeaters, 12 sticky pistons, and ONLY 20 blocks of any kind!

How To: Use MinGW to Compile Windows Exploits on Kali Linux
Cross-compilation allows you to develop for one platform (like Kali) and compile to run on a different platform (such as Windows). For developers, it means that they can work on their platform of choice and compile their code for their target platform. For hackers, it means we can compile exploit code for Windows from Kali.
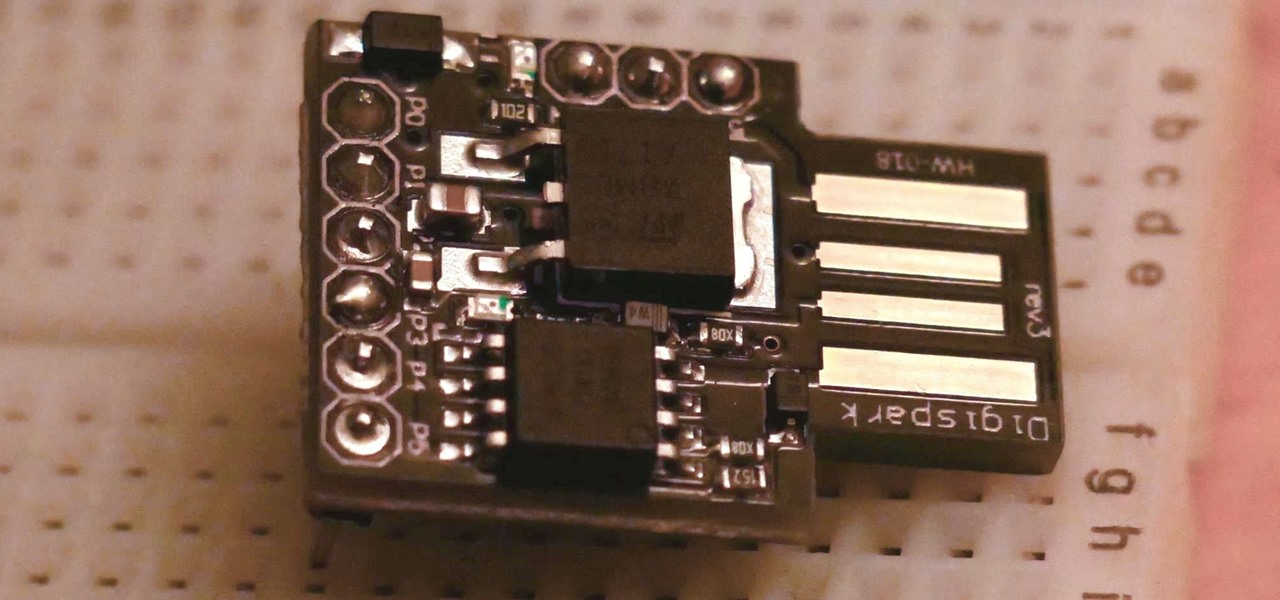
How To: Run USB Rubber Ducky Scripts on a Super Inexpensive Digispark Board
The USB Rubber Ducky is a famous attack tool that looks like a USB flash drive but acts like a keyboard when plugged into any unlocked device. The Ducky Script language used to control it is simple and powerful, and it works with Arduino and can run on boards like the ultra-cheap Digispark board.

How To: Crack WPA & WPA2 Wi-Fi Passwords with Pyrit
Pyrit is one of the most powerful WPA/WPA2 cracking tools in a hacker's arsenal, with the ability to benchmark a computer's CPU speeds, analyze capture files for crackable handshakes, and even tap into GPU password-cracking power. To demonstrate how quickly it can hack a WPA/WPA2 password, we'll use it to play a Wi-Fi hacking CTF game anyone can practice for less than $10.
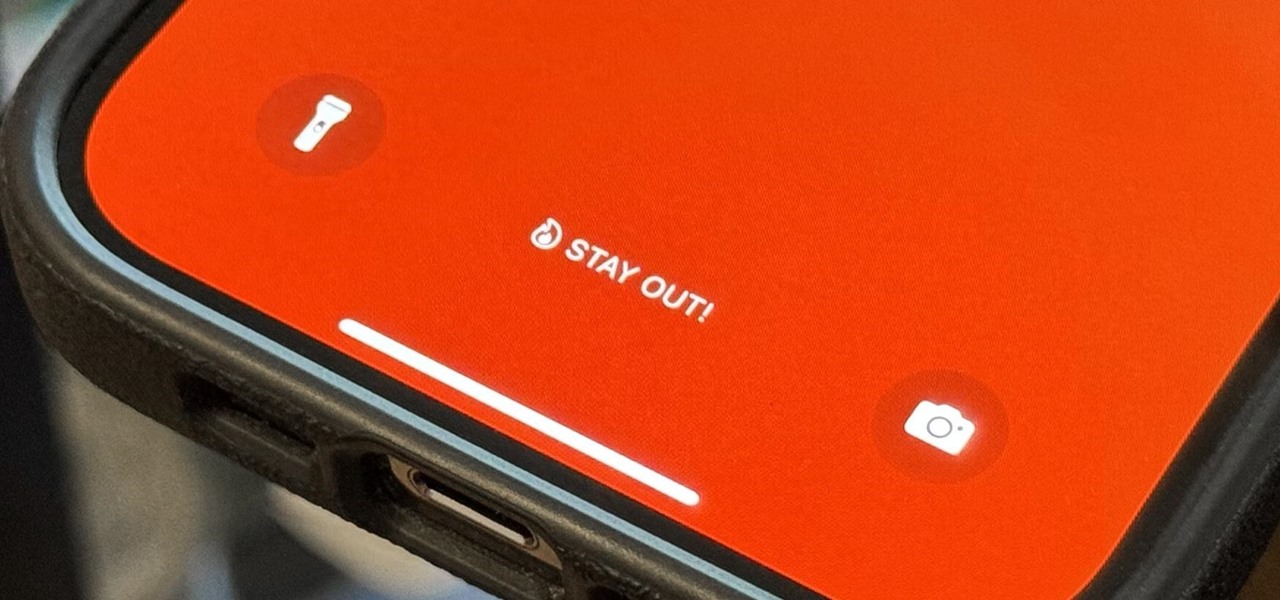
How To: Update Your iPhone's Lock Screen with an Attention-Grabbing Note, Reminder, Warning, or Other Custom Message
There's a lot you can customize on your iPhone's Lock Screen — wallpapers and photos, widgets, the display mode, notifications, and even the time's font and color. But there's another feature that lets you add custom text for whatever you want, whether it's an inspiring quote, a reminder, a warning to anyone who dares touch your iPhone, or even just your name.

How To: Convert Multiple Live Photos into 1 Continuous Video on Your iPhone
Live Photos capture the seconds before and after you take a photo, creating a fuller and also unique moment to share with friends and family. Unfortunately, it has been nearly impossible to share Live Photos with non-iPhone users — until now. Thanks to iOS 13, you can easily convert a Live Photo into a video, and even stitch multiple Live Photos together to create one long video.

How To: Enable or Disable Chat Heads in Facebook Messenger on Android for Quick Access to Conversations
Popular chat apps like Messenger allow us to communicate with friends and family across iOS and Android phones alike. However, that interconnectivity doesn't mean both apps are the same. While Facebook has made strides to close gaps between these two platforms, chat heads remain an exclusive feature for Android devices, and they let you keep Messenger threads close by.
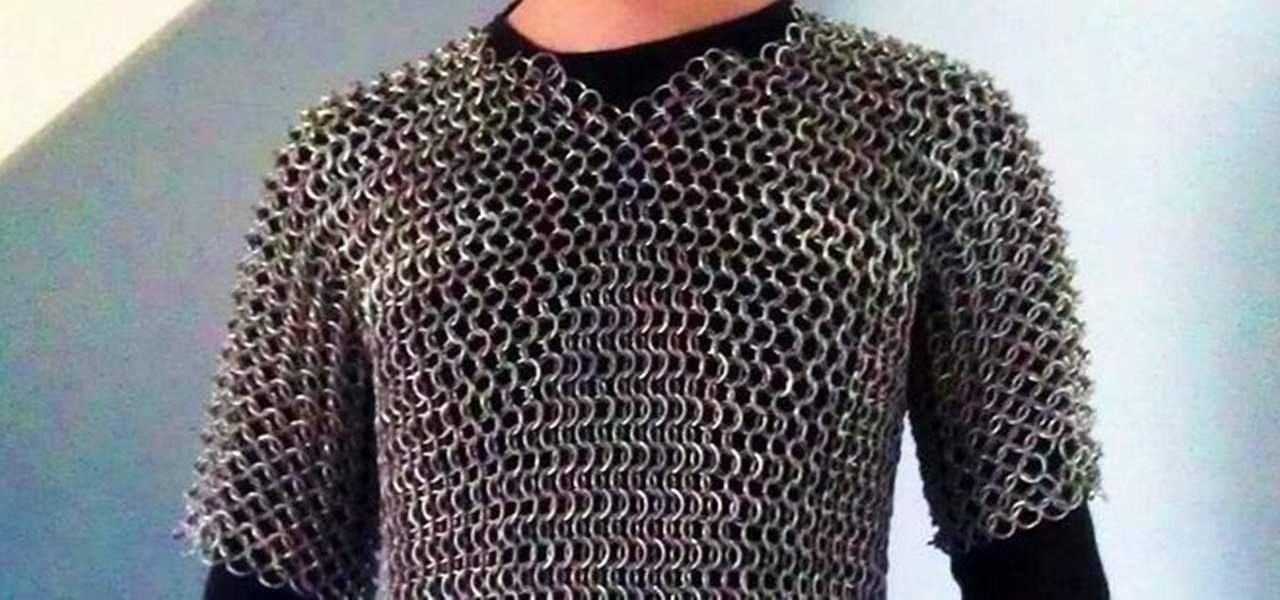
How To: Make Chain Mail Armor from Start to Finish
This article is a guide for making Chainmail Armor from start (simple wire) to finish (a finished chainmail shirt). We will be using the European 4 in 1 weave, as this is the most common weave. This is the weave that you usually see in movies. There are several sections to this guide: Materials, Making the Rings, Weaving the Rings, and Making the shirt.