Hot Posts

How To: The Messaging Trick You Never Knew You Needed
Whether you're wielding an iPhone, iPad, Mac, Android phone or tablet, or even a Windows PC, this little-known secret holds the key to effortless assistance and unwavering obedience. Intrigued? I thought so.
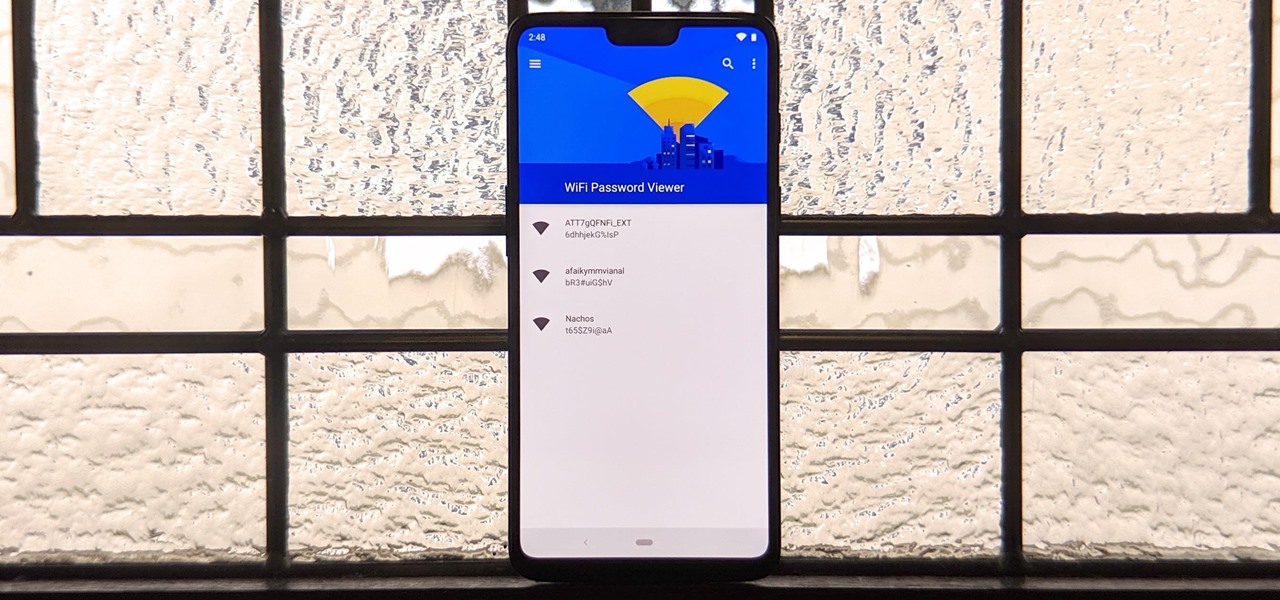
How To: See Passwords for Wi-Fi Networks You've Connected Your Android Device To
You've probably connected your Android device to dozens of Wi-Fi networks since you've had it, and your phone or tablet remembers each of them. Whether it's a hotspot at home, school, work, the gym, a coffee shop, a relative's apartment — or even from a friend's phone — each time you type in a Wi-Fi password, your Android device saves it for safekeeping and easy access later.

How To: Use FaceTime's Secret Hand Gestures and Reaction Buttons to Add Animated On-Screen Effects to Your Video Feed
Apple's Messages app has long had visual effects you could apply manually after long-pressing the send button, and there are even hidden keywords you could use to trigger full-screen effects automatically. FaceTime's latest update also gives you some full-screen effects to play around with during video calls, but the triggers are an entirely different concept — hand gestures.

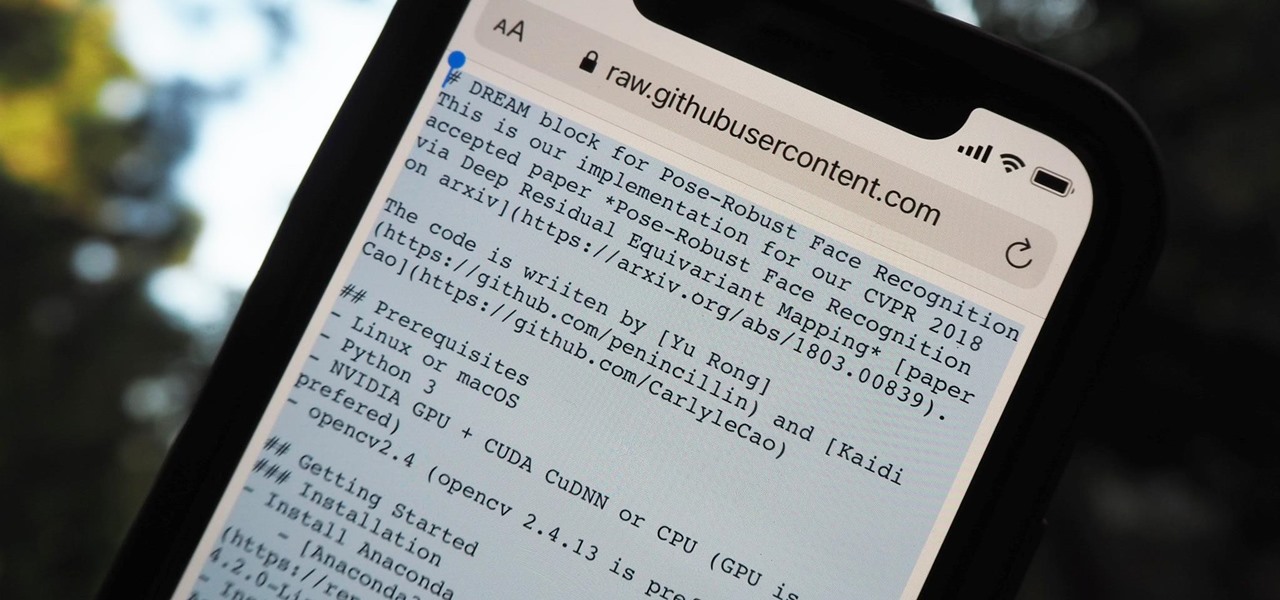
How To: Target Bluetooth Devices with Bettercap
An incredible amount of devices use Bluetooth or Bluetooth Low Energy to communicate. These devices rarely have their radios switched off, and in some cases, are deliberately used as trackers for lost items. While Bluetooth devices support MAC address randomization, many manufacturers do not use it, allowing us to use tools like Bettercap to scan for and track Bluetooth devices.
How To: 27 New Features and Changes Coming to Your iPhone with iOS 17.5
Apple released iOS 17.4 on March 5 with over 30 new features, but now it's iOS 17.5's turn for the spotlight. The update, currently in beta, gives us a few interesting updates and changes for iPhone, including a new word game, and there's even a sneak peek at what could be coming in the stable build.

How To: Clear Your Frequently Used and Recent Emoji from Your iPhone's Keyboard
Despite its name, the Frequently Used section on your iPhone's emoji keyboard features both frequently and recently used emoji, and it may contain emoji you've never even touched. If you want to remove all of those recommendations, there's an easy way to reset what you in Frequently Used to the defaults.

How To: Make This Amazing 9-Layer Density Tower from Things Found in Your Kitchen
Ralph Waldo Emerson once observed that "the seed of science" was "wonder," and taking a look at this nine-layer liquid tower from Steve Spangler's Sick Science! channel, one can't help but do just that — wonder. How is this possible? Is this magic or what?
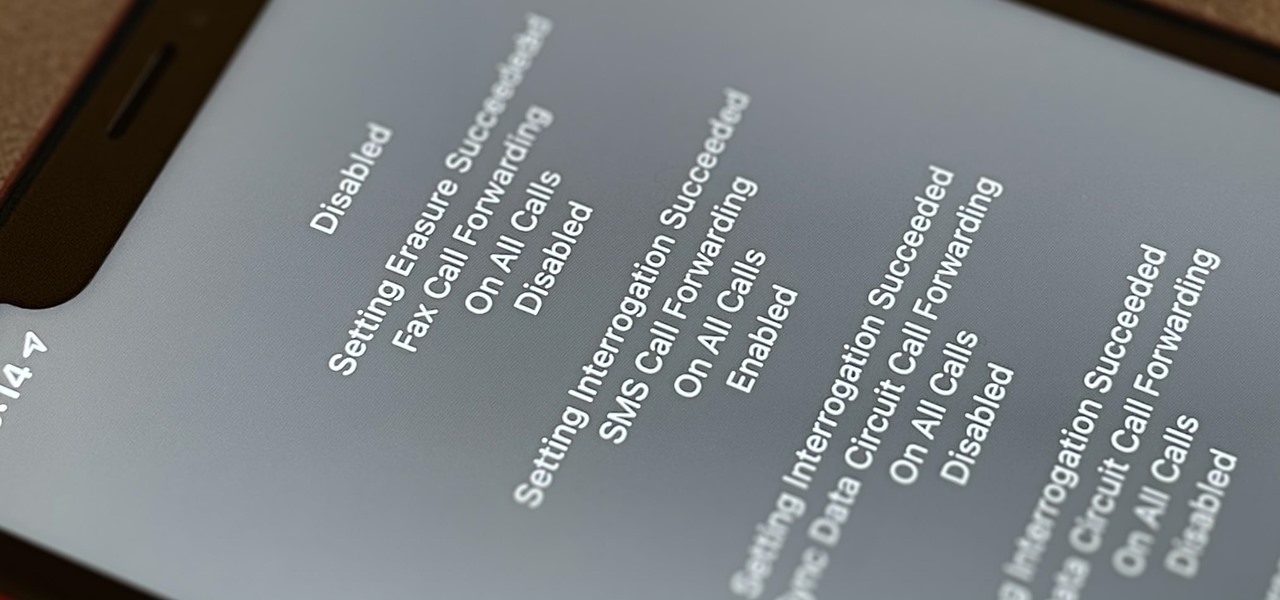
How To: Dial These Secret Codes to See if Someone Is Hijacking Calls & Texts on Your iPhone
Malevolent hackers can divert your incoming calls and texts to any number they want, and they don't need to be a criminal mastermind to do it. Even friends and family members can reroute your incoming calls and messages so that they know exactly who's trying to reach you, and all it takes is seconds of access to your iPhone or wireless account. These secret codes can help uncover them.

How To: Create an Admin User Account Using CMD Prompt (Windows)
This is a quick tutorial on how to create a new administrator account on a Windows computer. Step 1: Open CMD Prompt...
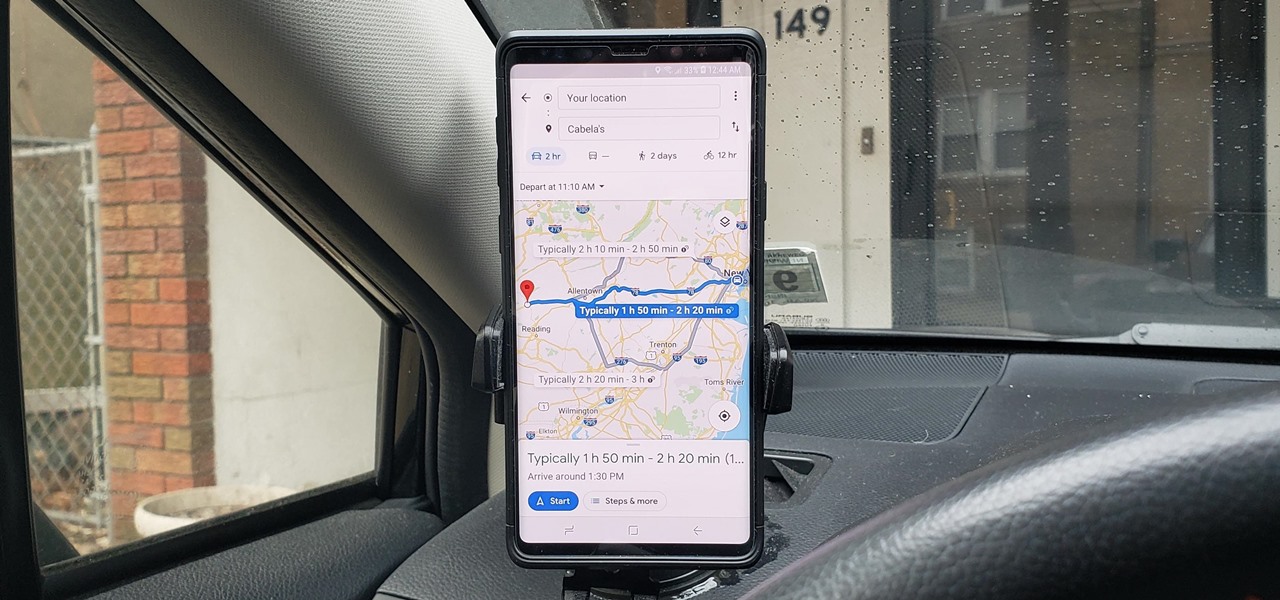
How To: See What Traffic Will Be Like at a Specific Time with Google Maps
As intuitive as Google Maps is for finding the best routes, it never let you choose departure and arrival times in the mobile app. This feature has long been available on the desktop site, allowing you to see what traffic should be like at a certain time and how long your drive would take at a point in the future. Fortunately, Google has finally added this feature to the app for iPhone and Android.

How To: Trigger iMessage Effects with Just a Keyword
One of the coolest aesthetic features of iMessage is its animated message effects. If you're like many users, you might even have discovered them by accident, where wishing your friend a "Happy Birthday!" or congratulating them on a promotion unexpectedly flooded your screen with balloons or confetti.

How To: Keep Your Night Vision Sharp with the iPhone's Hidden Red Screen
Night Shift, Dark Mode, Reduce White Point, and Zoom's Low Light Filter all help reduce the harmful effects on your body's clock that bright iPhone and iPad screens have at night. But there's another option on iOS and iPadOS that turns your entire display red, and it's useful for so much more than just late-night browsing in bed.
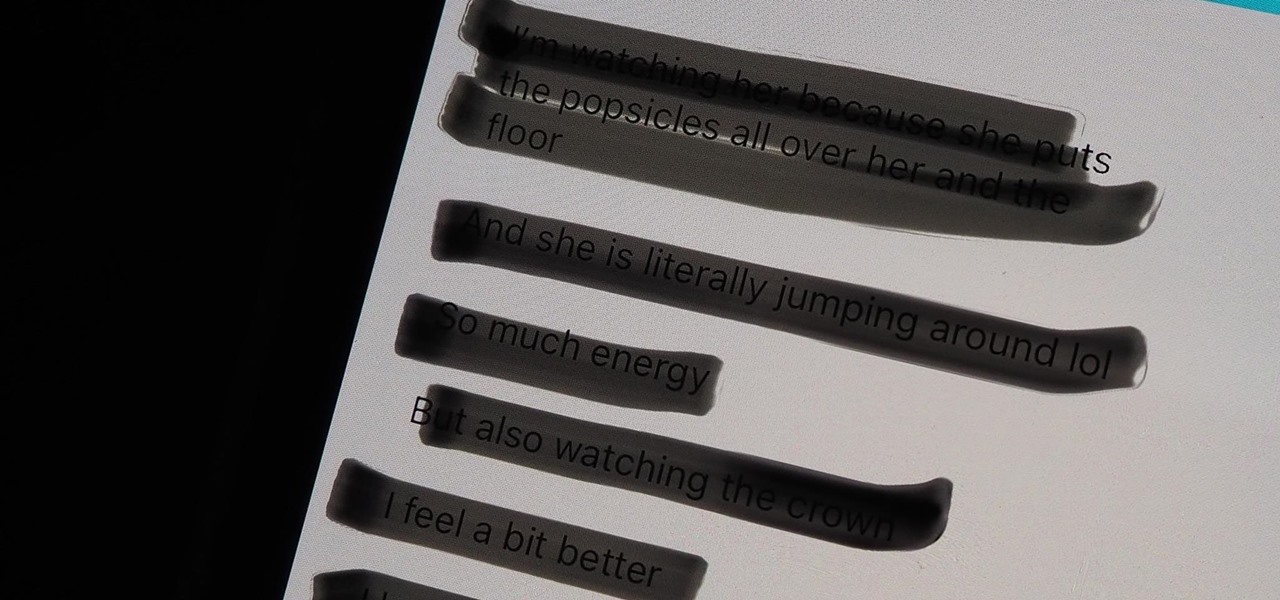
Warning: Sensitive Info You Black Out in Images Can Be Revealed with a Few Quick Edits on Your iPhone
These days, most images we post online or share with others come from our smartphones. Whenever personal data is in them, such as debit card numbers, addresses, phone numbers, passwords, and other sensitive information, it's easy to jump into your iPhone's markup tools to black out the text before sharing. But a digital marker may not hide everything.

How To: Exploit EternalBlue on Windows Server with Metasploit
Particular vulnerabilities and exploits come along and make headlines with their catchy names and impressive potential for damage. EternalBlue is one of those exploits. Originally tied to the NSA, this zero-day exploited a flaw in the SMB protocol, affecting many Windows machines and wreaking havoc everywhere. Here, we will use EternalBlue to exploit SMB via Metasploit.

How To: The Trick That Lets You Link to Specific Start Times in YouTube Videos Right from Your Phone
You can add a timestamp to any YouTube video in just a few clicks from the desktop website on your computer but not from YouTube's iOS or Android app. Until YouTube adds a "start time" when sharing videos from the mobile app, you'll have to use one of these workarounds on your phone or tablet.

How To: If 'Messages' Consumes Too Much iPhone or iCloud Storage, Don't Delete Your Conversations Just Yet
When iOS starts barking at you that you've run out of iCloud or iPhone storage, a quick trip to your settings to see what the culprit is may show that Messages is one of the worst offenders. But if deleting message after message doesn't free up your storage much, it's likely because "Messages" doesn't really mean messages.

How To: Use SQL Injection to Run OS Commands & Get a Shell
One of the ultimate goals in hacking is the ability to obtain shells in order to run system commands and own a target or network. SQL injection is typically only associated with databases and their data, but it can actually be used as a vector to gain a command shell. As a lesson, we'll be exploiting a simple SQL injection flaw to execute commands and ultimately get a reverse shell on the server.

How To: Make Delicious Thai Sticky Rice Without a Steamer or Rice Cooker
If you're a fan of Thai food, I'm sure you're familiar with sticky rice. There is something so special about its chewy texture and sweet flavor. If you have a desire to make it in your own kitchen but don't have the proper tools such as a traditional bamboo basket or stackable steamer, there are several other methods that work just as well. Once you try these alternative methods, I'm sure you'll be "sticking" to them for a while. What Makes Sticky Rice So Sticky?

How To: Embed a Metasploit Payload in an Original .Apk File | Part 2 – Do It Manually
UPDATE: This post is outdated, the latest version with the correct links and updated instructions can be found at my blog, here - https://techkernel.org/2015/12/19/embed-metasploit-payload-in-apk-manually/

How To: Make Spoofed Calls Using Any Phone Number You Want Right from Your Smartphone
Spoofed phone calls originate from one source that's disguising its phone number as a different one, and you probably get these calls all the time. Maybe they're numbers from your local area code or for prominent businesses, but the callers are just hijacking those digits to fool you into picking up. Turns out, making a spoofed call is something anybody can do — even you.

How To: Scan for Vulnerabilities on Any Website Using Nikto
Before attacking any website, a hacker or penetration tester will first compile a list of target surfaces. After they've used some good recon and found the right places to point their scope at, they'll use a web server scanning tool such as Nikto for hunting down vulnerabilities that could be potential attack vectors.

How To: Brute-Force Nearly Any Website Login with Hatch
The tactic of brute-forcing a login, i.e., trying many passwords very quickly until the correct one is discovered, can be easy for services like SSH or Telnet. For something like a website login page, we must identify different elements of the page first. Thanks to a Python tool for brute-forcing websites called Hatch, this process has been simplified to the point that even a beginner can try it.

How To: Crack Shadow Hashes After Getting Root on a Linux System
After gaining access to a root account, the next order of business is using that power to do something more significant. If the user passwords on the system can be obtained and cracked, an attacker can use them to pivot to other machines if the login is the same across systems. There are two tried-and-true password cracking tools that can accomplish this: John the Ripper and Hashcat.
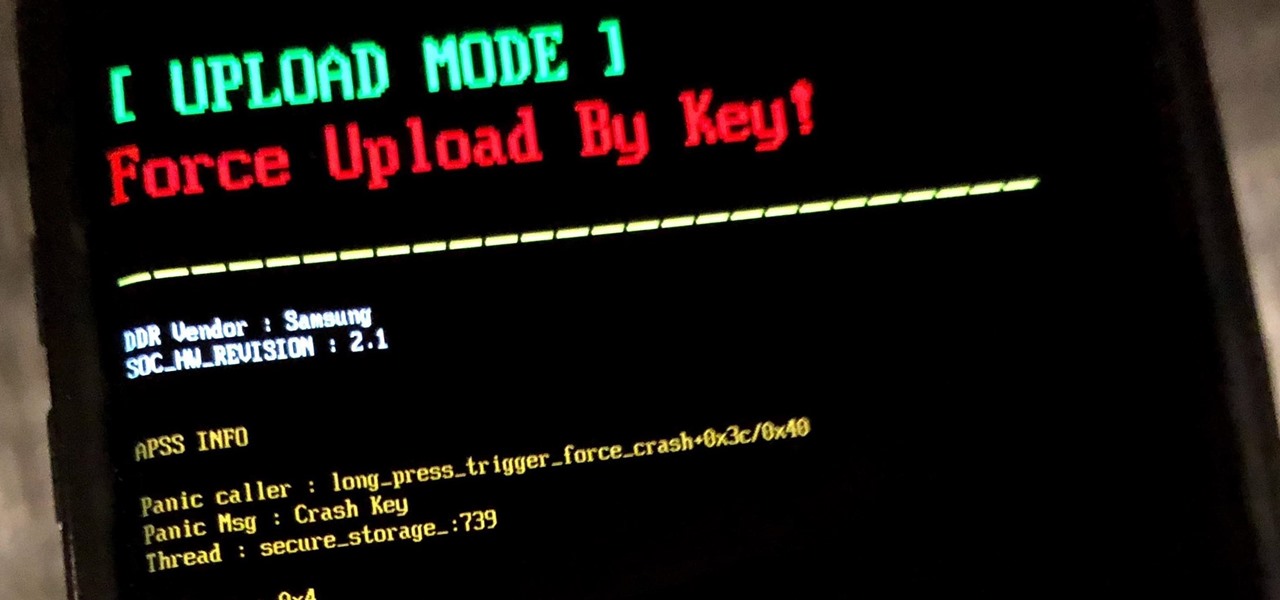
How To: Use Odin to Flash Samsung Galaxy Stock Firmware
If you own a Samsung phone and enjoy rooting or modding your device, flashing official firmware can be very useful. Odin is Samsung's own internal program for loading such updates for testing purposes, and it's quite easy to use for your own custom modification needs.

How To: 13 Tips Every Apple Pencil User Needs to Know for iPad
While it doesn't come with any iPad models out of the box, the Apple Pencil is perhaps the best iPad accessory you can get. It's a powerful writing and drawing tool with an intuitive design and user-friendliness that makes it easy to take notes, draw sketches, mark up documents, and more. And there's a lot you can do with it — some of which you may not have noticed yet.

How To: Gain SSH Access to Servers by Brute-Forcing Credentials
SSH is one of the most common protocols in use in modern IT infrastructures, and because of this, it can be a valuable attack vector for hackers. One of the most reliable ways to gain SSH access to servers is by brute-forcing credentials. There are a few methods of performing an SSH brute-force attack that will ultimately lead to the discovery of valid login credentials.
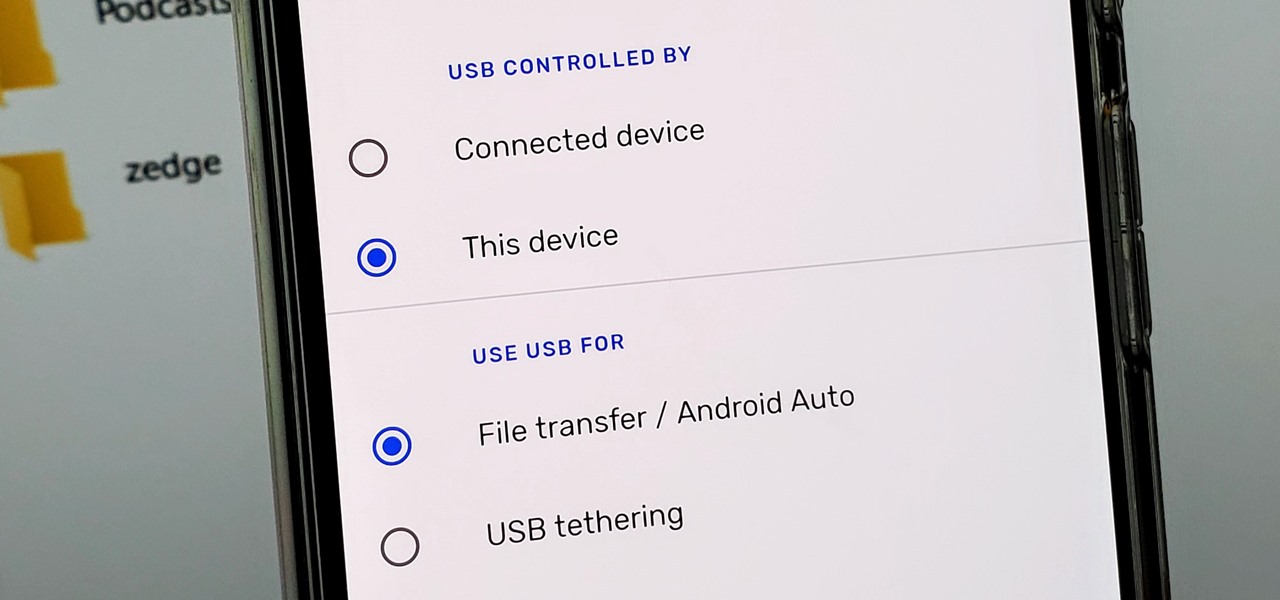
How To: Make the USB Connection on Your Android Phone Default to File Transfer Mode
Back in the earlier days of Android, you were able to connect your phone to a computer, and it would mount automatically. This meant once the USB connection was made, your internal storage would pop up on the computer and you could go about your business. But recent versions of Android changed that to help increase security.

How to Hack a Vending Machine: 9 Tricks to Getting Free Drinks, Snacks & Money
A vending machine is an invaluable yet totally frustrating piece of equipment. It's a godsend whenever your tummy's growling or you need an ice-cold drink on a hot summer day. But when something gets stuck inside or the machine flat-out malfunctions, it quickly becomes your archenemy. And when you're broke, it's basically just one big tease.

Redstone Logic Gates: Mastering the Fundamental Building Blocks for Creating In-Game Machines
Many people get so discouraged by their failures with redstone that they give up using it entirely, or never progress beyond using simple switches. However, by incorporating logic gates into your redstone designs, the applications are nearly limitless. The ability to add multiple switches to your machines is just a small part of what logic gates can do. Most importantly, they give you control.

How To: 20 Surprisingly Practical Uses for Apple AirTags
Apple AirTags are super helpful for keeping track of your keys, backpack, and other frequently misplaced items, but there are some pretty clever things you can do with them beyond finding your stuff.
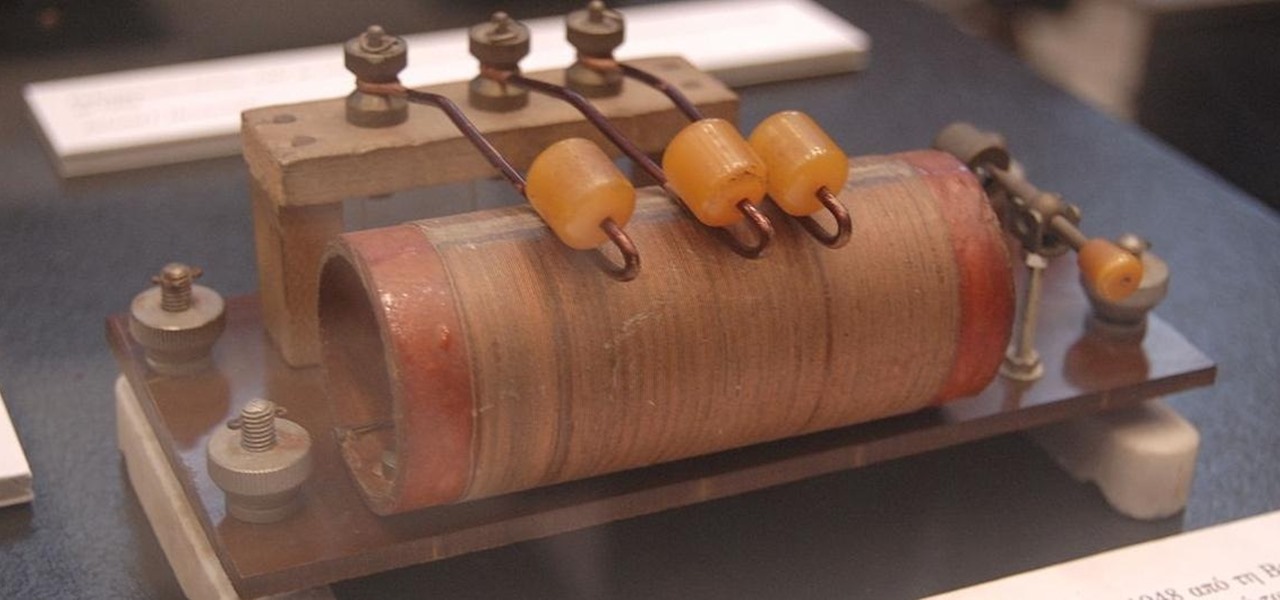
How To: The Complete Guide on How to Build a Crystal Radio—Plus How They Work
There's a lot that goes into making a nice crystal radio set, so this is going to have to be broken down into two parts. The first part is the actual making of a functional radio, and the second part is making the whole arrangement look nice. In this part, I'm actually going to tell you more than just how to make a crystal radio, but I'm also going to explain how and why they work. Crystal radios are pretty Steampunk in and of themselves, since they were first developed in the late 19th centu...

How to Hack Wi-Fi: Stealing Wi-Fi Passwords with an Evil Twin Attack
While Wi-Fi networks can be set up by smart IT people, that doesn't mean the users of the system are similarly tech-savvy. We'll demonstrate how an evil twin attack can steal Wi-Fi passwords by kicking a user off their trusted network while creating a nearly identical fake one. This forces the victim to connect to the fake network and supply the Wi-Fi password to regain internet access.

How To: 19 Harry Potter Spells Your Android Phone Can Cast Using Google Assistant
Apple's Siri is well-versed in the spells of the Wizarding World of Harry Potter, but it's not like Android users are Muggles. Google Assistant, Android's virtual concierge, can cast a few spells out of the box, and it can learn the spells it doesn't know quicker than a year of studying at Hogwarts.
How To: Get a 'Select All' Button for Webpages in Safari on Your iPhone
It should be simple to select and copy all text on a webpage in Safari, but it won't work as it does in other apps. Usually, you can press-and-hold down anywhere on a page and choose "Select All" from the edit menu, but that functionality is disabled in Safari and WebKit-based browsers by default — including in the latest iOS 14 version. Luckily, there is a workaround to getting a "Select All" button back.

How To: See Your iPhone's Actual Signal Strength for Cellular Reception
The signal bars in your iPhone's status bar are great visual indicators for knowing how good your cellular reception is, but they're not very accurate. Instead of showing the actual amount of signal you're receiving, they just give you a general range, and you'll have no idea if three out of four bars is actually a good connection or not. But there is a trick to see the real numbers.

How To: Set a GIF as a Live Wallpaper for Your iPhone's Lock Screen Background
In iOS, Apple provides a few live wallpapers that you can use for the background on your iPhone's lock screen, but these animated options are just wavy color shifts and ink-in-water effects. To really customize your lock screen, you can use a Live Photo for your wallpaper. If you can't find the right Live Photo, GIFs are the next best thing, and experimenting with them feels like a game almost.

Android for Hackers: How to Turn an Android Phone into a Hacking Device Without Root
With just a few taps, an Android phone can be weaponized into a covert hacking device capable of running tools such as Nmap, Nikto, and Netcat — all without rooting the device.
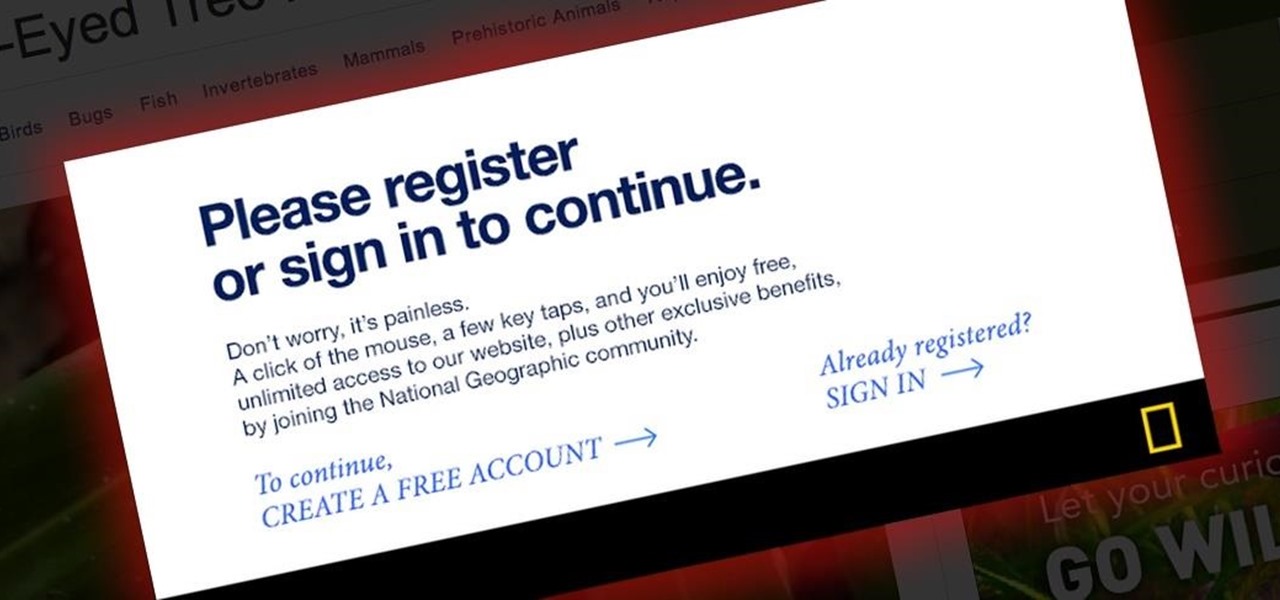
Popup Killer: How to Bypass Website Barriers Without Signing Up or Completing Surveys
Last night, I was reading a riveting National Geographic article on the green-eyed tree frog, until I was quickly interrupted by an annoying popup asking me to "create a free account" or "sign in." Really, I'd like to do neither. I just want to read about tree frogs.

Android 101: How to Sideload Apps by Enabling 'Unknown Sources' or 'Install Unknown Apps'
One of Android's biggest strengths relative to iOS is how simple it is to sideload apps that aren't on the official app store. Rather than having to sign IPA files or tell your phone you trust a developer every two weeks, you can just enable a setting and be done with it.

How To: You Can Run Shortcuts Right from Your iPhone's Lock Screen & Here Are 6 Ways to Do It
Shortcuts are meant to make your life easier, and iPhone shortcuts are no exception. They can use different triggers, manual or automated, to perform actions in the background, allowing you to do things like send a prewritten text message during a bad date or change your wallpaper at certain times of the day. However, sometimes it's not only about the shortcut itself but about how fast you can run it.