About dontrustme
Find me on 0x00sec.org
- Location: Baku, Azerbaijan
dontrustme's Latest Posts
 How To:
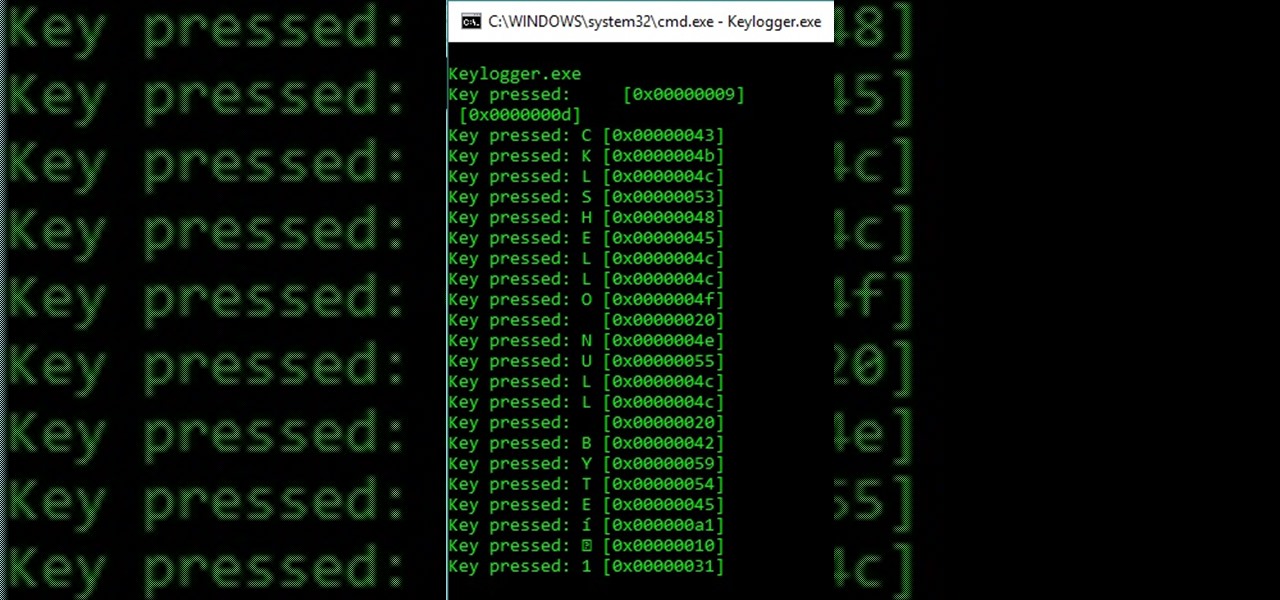
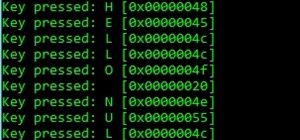
Security-Oriented C Tutorial 0xF9 - I Spy with My Little... Program - Keylogging 101
How To:
Security-Oriented C Tutorial 0xF9 - I Spy with My Little... Program - Keylogging 101
 How To:
Security-Oriented C Tutorial 0x22 - Introduction to the WinAPI
How To:
Security-Oriented C Tutorial 0x22 - Introduction to the WinAPI
 How To:
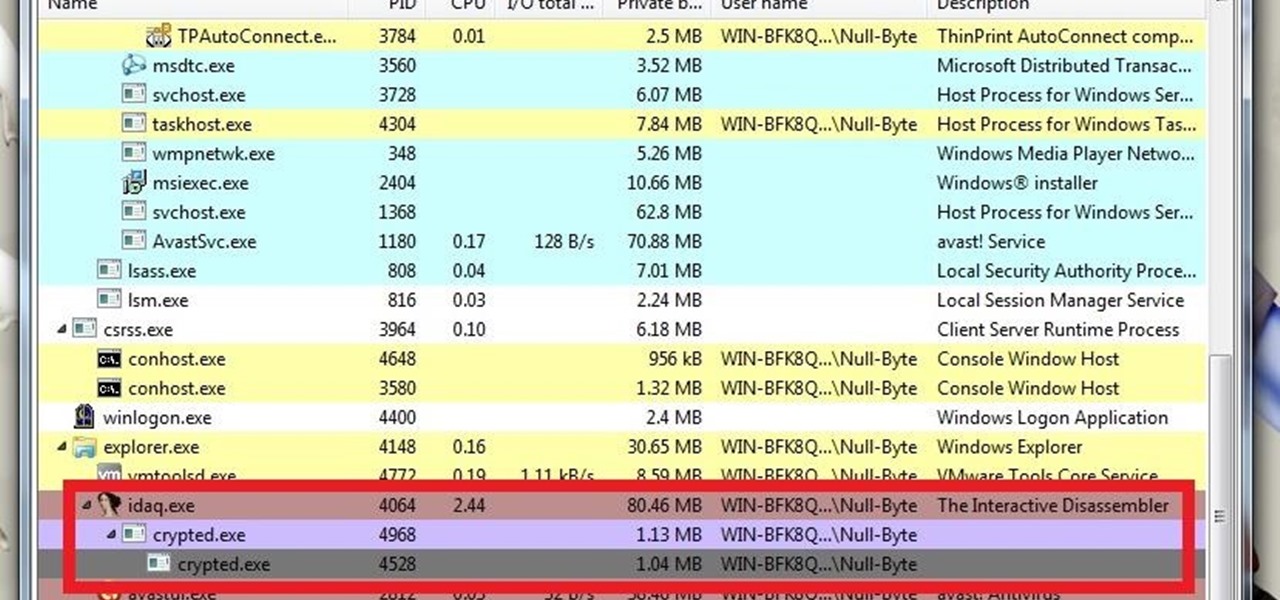
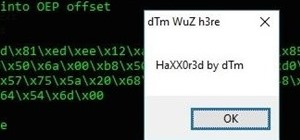
Reversing and Analyzing a Runtime Crypter
How To:
Reversing and Analyzing a Runtime Crypter
 How To:
An Extended Guide on Runtime Crypters
How To:
An Extended Guide on Runtime Crypters
 How To:
A Guide on Runtime Crypters
How To:
A Guide on Runtime Crypters
 How To:
Security-Oriented C Tutorial 0x21 - Linked Lists
How To:
Security-Oriented C Tutorial 0x21 - Linked Lists
 How To:
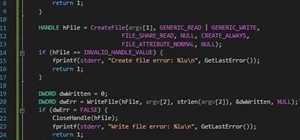
Security-Oriented C Tutorial 0xFA - Enhancing Our Crypter
How To:
Security-Oriented C Tutorial 0xFA - Enhancing Our Crypter
 How To:
Security-Oriented C Tutorial 0x20 - Problems with popen and Shifty system
How To:
Security-Oriented C Tutorial 0x20 - Problems with popen and Shifty system
 How To:
Security-Oriented C Tutorial 0xFB - A Simple Crypter
How To:
Security-Oriented C Tutorial 0xFB - A Simple Crypter
 How To:
Security-Oriented C Tutorial 0xFC - A Simple XOR Encryptor
How To:
Security-Oriented C Tutorial 0xFC - A Simple XOR Encryptor
 How To:
Security-Oriented C Tutorial 0x19 - Functions Part V: Passing by Reference
How To:
Security-Oriented C Tutorial 0x19 - Functions Part V: Passing by Reference
 How To:
Security-Oriented C Tutorial 0xFD - Software on Steroids - Upgrading Our Malware
How To:
Security-Oriented C Tutorial 0xFD - Software on Steroids - Upgrading Our Malware
 How To:
Security-Oriented C Tutorial 0x18 - Malloc and the Heap
How To:
Security-Oriented C Tutorial 0x18 - Malloc and the Heap
 How To:
Security-Oriented C Tutorial 0x17 - Structs
How To:
Security-Oriented C Tutorial 0x17 - Structs
 How To:
Security-Oriented C Tutorial 0x16 - Functions Part IV: Recursion
How To:
Security-Oriented C Tutorial 0x16 - Functions Part IV: Recursion
 How To:
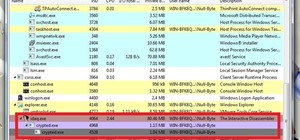
Security-Oriented C Tutorial 0xFF - An Introduction to Malware
How To:
Security-Oriented C Tutorial 0xFF - An Introduction to Malware
 How To:
Security-Oriented C Tutorial 0x15 - File I/O
How To:
Security-Oriented C Tutorial 0x15 - File I/O
 How To:
Security-Oriented C Tutorial 0x14 - Format String Vulnerability Part I: Buffer Overflow's Nasty Little Brother
How To:
Security-Oriented C Tutorial 0x14 - Format String Vulnerability Part I: Buffer Overflow's Nasty Little Brother
 How To:
Security-Oriented C Tutorial 0x13 - Pieces of a Puzzle
How To:
Security-Oriented C Tutorial 0x13 - Pieces of a Puzzle
 How To:
Security-Oriented C Tutorial 0x12 - Scope
How To:
Security-Oriented C Tutorial 0x12 - Scope
 How To:
Security-Oriented C Tutorial 0x11 - Command Line Arguments
How To:
Security-Oriented C Tutorial 0x11 - Command Line Arguments
 How To:
Security-Oriented C Tutorial 0x10 - Pointers and Addresses
How To:
Security-Oriented C Tutorial 0x10 - Pointers and Addresses
 How To:
Security-Oriented C Tutorial 0x0F - Functions Part III: The Stack
How To:
Security-Oriented C Tutorial 0x0F - Functions Part III: The Stack
 How To:
Security-Oriented C Tutorial 0x0E - Functions Part II: Memory
How To:
Security-Oriented C Tutorial 0x0E - Functions Part II: Memory
 How To:
Security-Oriented C Tutorial 0x0D - Functions Part I: Introduction
How To:
Security-Oriented C Tutorial 0x0D - Functions Part I: Introduction
 How To:
Security-Oriented C Tutorial 0x0C - Buffer Overflows Exposed!
How To:
Security-Oriented C Tutorial 0x0C - Buffer Overflows Exposed!
 How To:
Security-Oriented C Tutorial 0x0B - User Input
How To:
Security-Oriented C Tutorial 0x0B - User Input
 How To:
Security-Oriented C Tutorial 0x0A - Man Pages
How To:
Security-Oriented C Tutorial 0x0A - Man Pages
 How To:
Security-Oriented C Tutorial 0x09 - More on Strings
How To:
Security-Oriented C Tutorial 0x09 - More on Strings
 How To:
Security-Oriented C Tutorial 0x08 - A Trip Down Memory Lane
How To:
Security-Oriented C Tutorial 0x08 - A Trip Down Memory Lane
 How To:
Security-Oriented C Tutorial 0x07 - Arrays and Strings
How To:
Security-Oriented C Tutorial 0x07 - Arrays and Strings
 How To:
Security-Oriented C Tutorial 0x06 - Operators
How To:
Security-Oriented C Tutorial 0x06 - Operators
 How To:
Security-Oriented C Tutorial 0x05 - Control Structures Part II: Loops
How To:
Security-Oriented C Tutorial 0x05 - Control Structures Part II: Loops
 How To:
Security-Oriented C Tutorial 0x04 - Control Structures Part I: If Statements
How To:
Security-Oriented C Tutorial 0x04 - Control Structures Part I: If Statements
 How To:
Security-Oriented C Tutorial 0x03 - Bits, Bytes, Broken?
How To:
Security-Oriented C Tutorial 0x03 - Bits, Bytes, Broken?
 How To:
Security-Oriented C Tutorial 0x02 - Variables && Data Types
How To:
Security-Oriented C Tutorial 0x02 - Variables && Data Types
 How To:
Security-Oriented C Tutorial 0x01 - Hello, World!
How To:
Security-Oriented C Tutorial 0x01 - Hello, World!
 How To:
Security-Oriented C Tutorial 0x00 - Introduction
How To:
Security-Oriented C Tutorial 0x00 - Introduction
Next Page
Prev Page
Sites
- Hot
- Latest
-
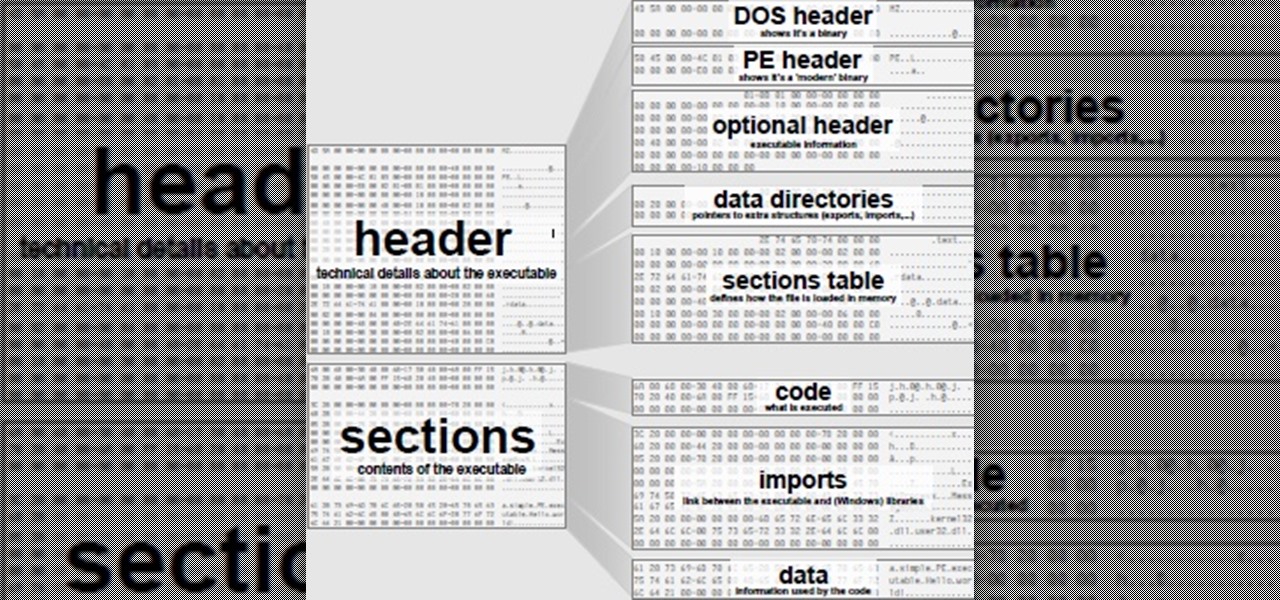
 How To:
Security-Oriented C Tutorial 0xF8 - PE File Infection
How To:
Security-Oriented C Tutorial 0xF8 - PE File Infection
-
 How To:
Security-Oriented C Tutorial 0xF9 - I Spy with My Little... Program - Keylogging 101
How To:
Security-Oriented C Tutorial 0xF9 - I Spy with My Little... Program - Keylogging 101
-
 How To:
Security-Oriented C Tutorial 0x22 - Introduction to the WinAPI
How To:
Security-Oriented C Tutorial 0x22 - Introduction to the WinAPI
-
 How To:
Reversing and Analyzing a Runtime Crypter
How To:
Reversing and Analyzing a Runtime Crypter
-
 How To:
An Extended Guide on Runtime Crypters
How To:
An Extended Guide on Runtime Crypters
-
 How To:
A Guide on Runtime Crypters
How To:
A Guide on Runtime Crypters
-
 How To:
Security-Oriented C Tutorial 0x21 - Linked Lists
How To:
Security-Oriented C Tutorial 0x21 - Linked Lists
-
 How To:
Security-Oriented C Tutorial 0xFA - Enhancing Our Crypter
How To:
Security-Oriented C Tutorial 0xFA - Enhancing Our Crypter
-
 How To:
Security-Oriented C Tutorial 0x20 - Problems with popen and Shifty system
How To:
Security-Oriented C Tutorial 0x20 - Problems with popen and Shifty system
-
 How To:
Security-Oriented C Tutorial 0xFB - A Simple Crypter
How To:
Security-Oriented C Tutorial 0xFB - A Simple Crypter
-
 How To:
Security-Oriented C Tutorial 0xFC - A Simple XOR Encryptor
How To:
Security-Oriented C Tutorial 0xFC - A Simple XOR Encryptor
-
 How To:
Security-Oriented C Tutorial 0x19 - Functions Part V: Passing by Reference
How To:
Security-Oriented C Tutorial 0x19 - Functions Part V: Passing by Reference
-
 How To:
Security-Oriented C Tutorial 0xFD - Software on Steroids - Upgrading Our Malware
How To:
Security-Oriented C Tutorial 0xFD - Software on Steroids - Upgrading Our Malware
-
 How To:
Security-Oriented C Tutorial 0x18 - Malloc and the Heap
How To:
Security-Oriented C Tutorial 0x18 - Malloc and the Heap
-
 How To:
Security-Oriented C Tutorial 0x17 - Structs
How To:
Security-Oriented C Tutorial 0x17 - Structs
-
 How To:
Security-Oriented C Tutorial 0x16 - Functions Part IV: Recursion
How To:
Security-Oriented C Tutorial 0x16 - Functions Part IV: Recursion
-
 How To:
Security-Oriented C Tutorial 0xFF - An Introduction to Malware
How To:
Security-Oriented C Tutorial 0xFF - An Introduction to Malware
-
 How To:
Security-Oriented C Tutorial 0x15 - File I/O
How To:
Security-Oriented C Tutorial 0x15 - File I/O
-
 How To:
Security-Oriented C Tutorial 0x14 - Format String Vulnerability Part I: Buffer Overflow's Nasty Little Brother
How To:
Security-Oriented C Tutorial 0x14 - Format String Vulnerability Part I: Buffer Overflow's Nasty Little Brother
-
 How To:
Security-Oriented C Tutorial 0x13 - Pieces of a Puzzle
How To:
Security-Oriented C Tutorial 0x13 - Pieces of a Puzzle
-
 How To:
Security-Oriented C Tutorial 0x01 - Hello, World!
How To:
Security-Oriented C Tutorial 0x01 - Hello, World!
-
 How To:
Security-Oriented C Tutorial 0x21 - Linked Lists
How To:
Security-Oriented C Tutorial 0x21 - Linked Lists
-
 How To:
Security-Oriented C Tutorial 0x17 - Structs
How To:
Security-Oriented C Tutorial 0x17 - Structs
-
 How To:
Security-Oriented C Tutorial 0x06 - Operators
How To:
Security-Oriented C Tutorial 0x06 - Operators
-
 How To:
A Guide on Runtime Crypters
How To:
A Guide on Runtime Crypters
-
 How To:
Security-Oriented C Tutorial 0xFC - A Simple XOR Encryptor
How To:
Security-Oriented C Tutorial 0xFC - A Simple XOR Encryptor
-
 How To:
Security-Oriented C Tutorial 0x14 - Format String Vulnerability Part I: Buffer Overflow's Nasty Little Brother
How To:
Security-Oriented C Tutorial 0x14 - Format String Vulnerability Part I: Buffer Overflow's Nasty Little Brother
-
 How To:
Security-Oriented C Tutorial 0x12 - Scope
How To:
Security-Oriented C Tutorial 0x12 - Scope
-
 How To:
Security-Oriented C Tutorial 0x11 - Command Line Arguments
How To:
Security-Oriented C Tutorial 0x11 - Command Line Arguments
-
 How To:
Security-Oriented C Tutorial 0x0C - Buffer Overflows Exposed!
How To:
Security-Oriented C Tutorial 0x0C - Buffer Overflows Exposed!
-
 How To:
Security-Oriented C Tutorial 0x00 - Introduction
How To:
Security-Oriented C Tutorial 0x00 - Introduction
-
 How To:
Security-Oriented C Tutorial 0xF8 - PE File Infection
How To:
Security-Oriented C Tutorial 0xF8 - PE File Infection
-
 How To:
Security-Oriented C Tutorial 0xF9 - I Spy with My Little... Program - Keylogging 101
How To:
Security-Oriented C Tutorial 0xF9 - I Spy with My Little... Program - Keylogging 101
-
 How To:
Security-Oriented C Tutorial 0x22 - Introduction to the WinAPI
How To:
Security-Oriented C Tutorial 0x22 - Introduction to the WinAPI
-
 How To:
Reversing and Analyzing a Runtime Crypter
How To:
Reversing and Analyzing a Runtime Crypter
-
 How To:
An Extended Guide on Runtime Crypters
How To:
An Extended Guide on Runtime Crypters
-
 How To:
Security-Oriented C Tutorial 0xFA - Enhancing Our Crypter
How To:
Security-Oriented C Tutorial 0xFA - Enhancing Our Crypter
-
 How To:
Security-Oriented C Tutorial 0x20 - Problems with popen and Shifty system
How To:
Security-Oriented C Tutorial 0x20 - Problems with popen and Shifty system
-
 How To:
Security-Oriented C Tutorial 0xFB - A Simple Crypter
How To:
Security-Oriented C Tutorial 0xFB - A Simple Crypter
-
 How To:
Security-Oriented C Tutorial 0x19 - Functions Part V: Passing by Reference
How To:
Security-Oriented C Tutorial 0x19 - Functions Part V: Passing by Reference
-
 How To:
Security-Oriented C Tutorial 0xFD - Software on Steroids - Upgrading Our Malware
How To:
Security-Oriented C Tutorial 0xFD - Software on Steroids - Upgrading Our Malware
-
 How To:
Security-Oriented C Tutorial 0x18 - Malloc and the Heap
How To:
Security-Oriented C Tutorial 0x18 - Malloc and the Heap
-
 How To:
Security-Oriented C Tutorial 0x16 - Functions Part IV: Recursion
How To:
Security-Oriented C Tutorial 0x16 - Functions Part IV: Recursion
-
 How To:
Security-Oriented C Tutorial 0xFF - An Introduction to Malware
How To:
Security-Oriented C Tutorial 0xFF - An Introduction to Malware
-
 How To:
Security-Oriented C Tutorial 0x15 - File I/O
How To:
Security-Oriented C Tutorial 0x15 - File I/O
-
 How To:
Security-Oriented C Tutorial 0x13 - Pieces of a Puzzle
How To:
Security-Oriented C Tutorial 0x13 - Pieces of a Puzzle
-
 How To:
Security-Oriented C Tutorial 0x10 - Pointers and Addresses
How To:
Security-Oriented C Tutorial 0x10 - Pointers and Addresses
-
 How To:
Security-Oriented C Tutorial 0x0F - Functions Part III: The Stack
How To:
Security-Oriented C Tutorial 0x0F - Functions Part III: The Stack
-
 How To:
Security-Oriented C Tutorial 0x0E - Functions Part II: Memory
How To:
Security-Oriented C Tutorial 0x0E - Functions Part II: Memory
-
 How To:
Security-Oriented C Tutorial 0x0D - Functions Part I: Introduction
How To:
Security-Oriented C Tutorial 0x0D - Functions Part I: Introduction
-
 How To:
Security-Oriented C Tutorial 0x0B - User Input
How To:
Security-Oriented C Tutorial 0x0B - User Input
-
 How To:
Security-Oriented C Tutorial 0x0A - Man Pages
How To:
Security-Oriented C Tutorial 0x0A - Man Pages
-
 How To:
Security-Oriented C Tutorial 0x09 - More on Strings
How To:
Security-Oriented C Tutorial 0x09 - More on Strings
-
 How To:
Security-Oriented C Tutorial 0x08 - A Trip Down Memory Lane
How To:
Security-Oriented C Tutorial 0x08 - A Trip Down Memory Lane
-
 How To:
Security-Oriented C Tutorial 0x07 - Arrays and Strings
How To:
Security-Oriented C Tutorial 0x07 - Arrays and Strings
-
 How To:
Security-Oriented C Tutorial 0x05 - Control Structures Part II: Loops
How To:
Security-Oriented C Tutorial 0x05 - Control Structures Part II: Loops
-
 How To:
Security-Oriented C Tutorial 0x04 - Control Structures Part I: If Statements
How To:
Security-Oriented C Tutorial 0x04 - Control Structures Part I: If Statements
-
 How To:
Security-Oriented C Tutorial 0x03 - Bits, Bytes, Broken?
How To:
Security-Oriented C Tutorial 0x03 - Bits, Bytes, Broken?
-
 How To:
Security-Oriented C Tutorial 0x02 - Variables && Data Types
How To:
Security-Oriented C Tutorial 0x02 - Variables && Data Types