Hot Posts
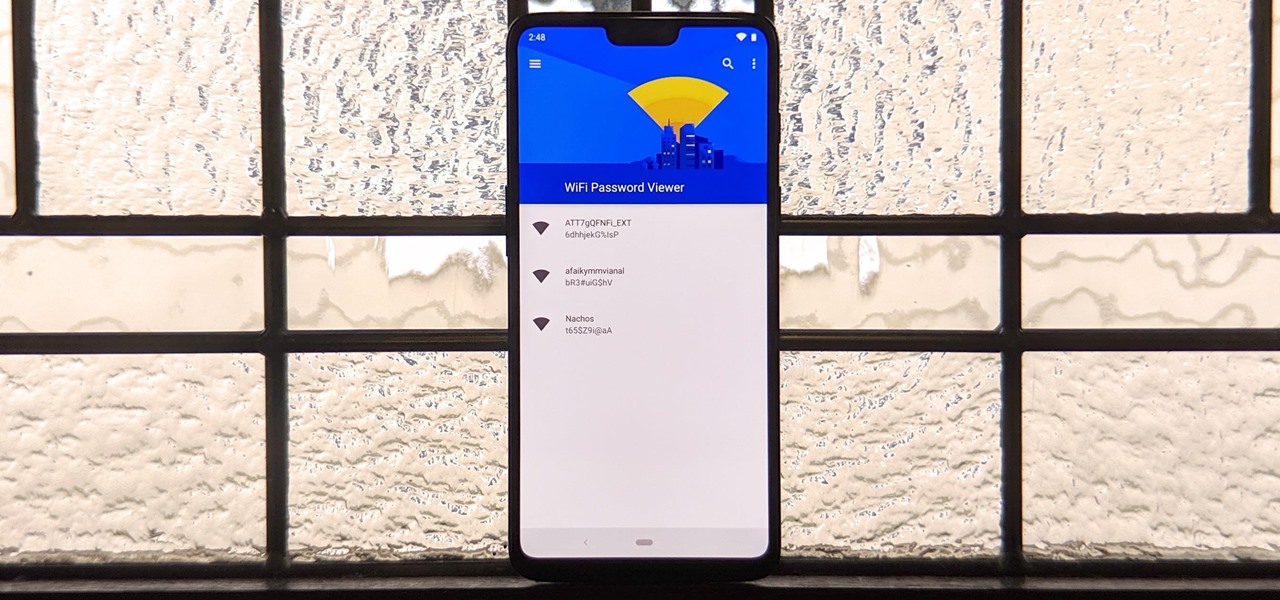
How To: See Passwords for Wi-Fi Networks You've Connected Your Android Device To
You've probably connected your Android device to dozens of Wi-Fi networks since you've had it, and your phone or tablet remembers each of them. Whether it's a hotspot at home, school, work, the gym, a coffee shop, a relative's apartment — or even from a friend's phone — each time you type in a Wi-Fi password, your Android device saves it for safekeeping and easy access later.

News: Apple Pencil 3 Is Almost Here — And It Comes with Squeeze Gestures and These Other Features
Apple's spring event, where the company will announce a new iPad model, is just around the corner. We also expect to see the long-awaited Apple Pencil (3rd generation), also known more simply as Apple Pencil 3, with several significant enhancements that promise to make it an indispensable tool for anyone who uses their iPad for note-taking, sketching, illustrating graphics, and more.

How To: Create an Admin User Account Using CMD Prompt (Windows)
This is a quick tutorial on how to create a new administrator account on a Windows computer. Step 1: Open CMD Prompt...

How To: Make Spoofed Calls Using Any Phone Number You Want Right from Your Smartphone
Spoofed phone calls originate from one source that's disguising its phone number as a different one, and you probably get these calls all the time. Maybe they're numbers from your local area code or for prominent businesses, but the callers are just hijacking those digits to fool you into picking up. Turns out, making a spoofed call is something anybody can do — even you.

How To: Crack SSH Private Key Passwords with John the Ripper
Secure Shell is one of the most common network protocols, typically used to manage remote machines through an encrypted connection. However, SSH is prone to password brute-forcing. Key-based authentication is much more secure, and private keys can even be encrypted for additional security. But even that isn't bulletproof since SSH private key passwords can be cracked using John the Ripper.

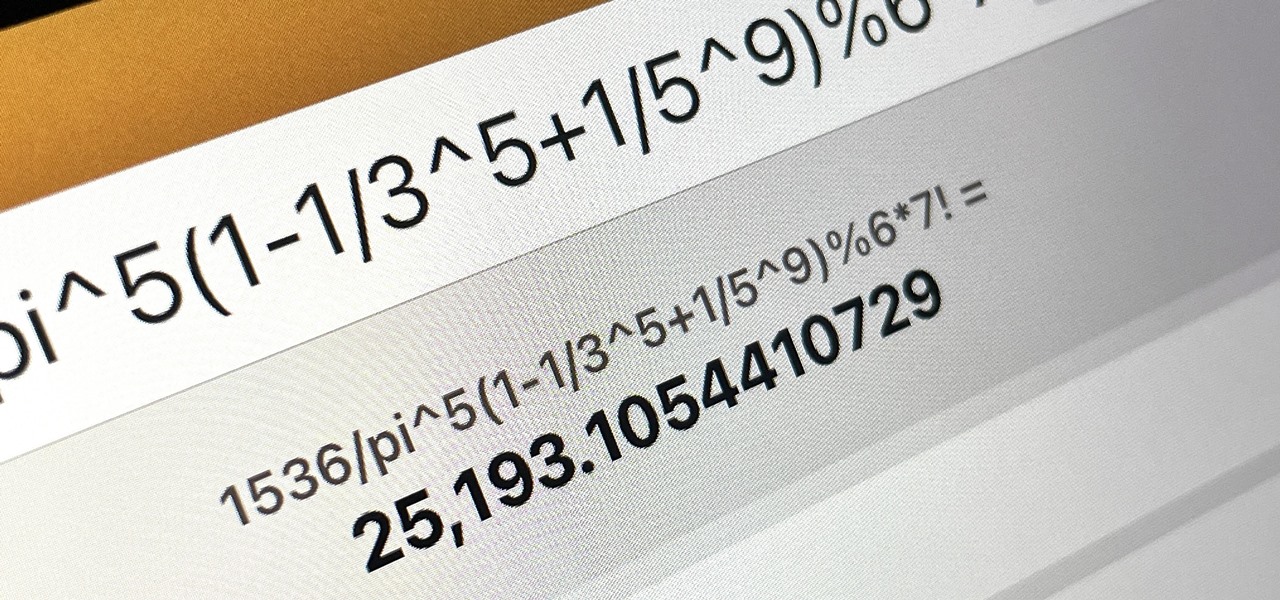
How To: Generate random numbers (with decimals) in Excel
This video shows you how to generate random numbers with decimals in Microsoft Excel.When generating random numbers you must have a lower and upper limit, so that your number will be generated between the two limits. For a number without decimals, you only have to use the "=randbetween" function. If you want to use decimals, you will have to use a different but similar function. Start by typing "=rand()". Next, you multiply this by the difference between the limits and add the lower limit. Fo...

How To: Use FaceTime's Secret Hand Gestures and Reaction Buttons to Add Animated On-Screen Effects to Your Video Feed
Apple's Messages app has long had visual effects you could apply manually after long-pressing the send button, and there are even hidden keywords you could use to trigger full-screen effects automatically. FaceTime's latest update also gives you some full-screen effects to play around with during video calls, but the triggers are an entirely different concept — hand gestures.

How To: Gain SSH Access to Servers by Brute-Forcing Credentials
SSH is one of the most common protocols in use in modern IT infrastructures, and because of this, it can be a valuable attack vector for hackers. One of the most reliable ways to gain SSH access to servers is by brute-forcing credentials. There are a few methods of performing an SSH brute-force attack that will ultimately lead to the discovery of valid login credentials.
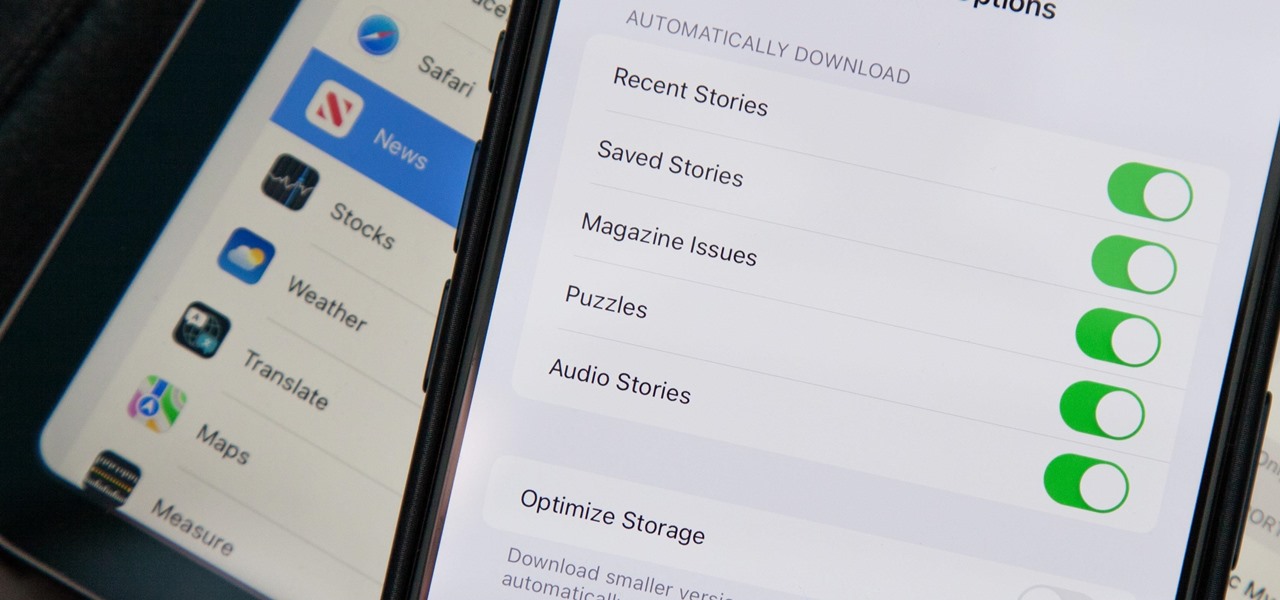
How To: Apple News Gives You More Options for Automatic Downloads on iOS 17.5
In the upcoming iOS 17.5 software update, there are new features for EU countries and mobile device managers only, but there are also more widespread user-facing changes to Books, Podcasts, and other apps. News is one of those other apps, and it's giving us more preferences for automatic downloads.
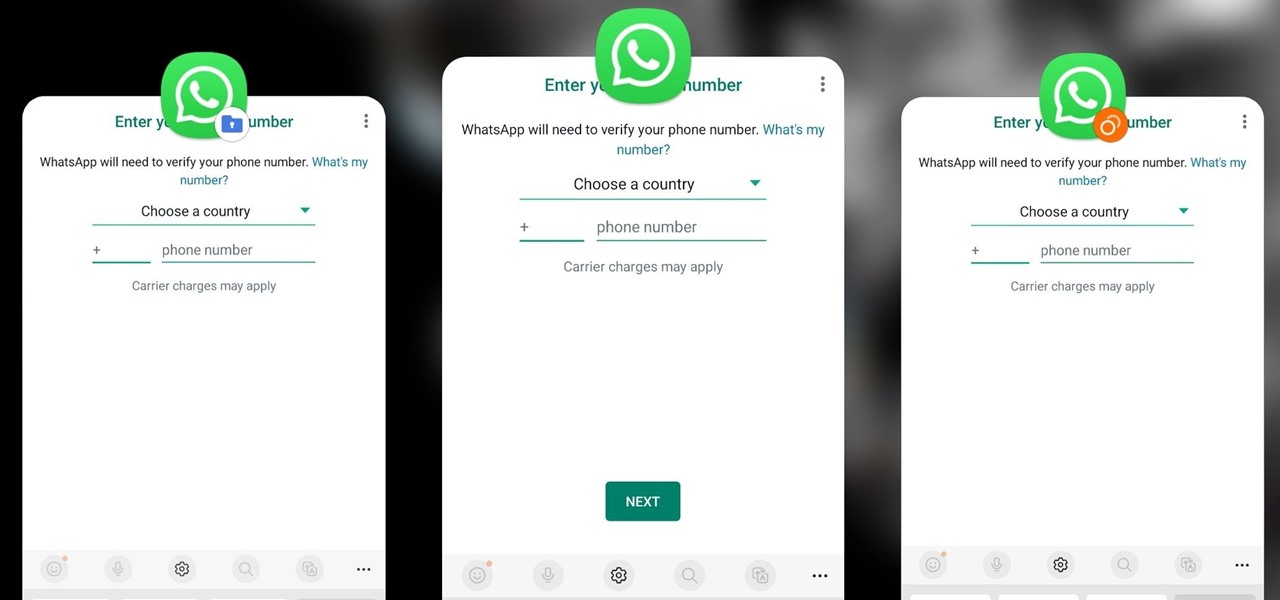
How To: Clone Any Android App on Your Samsung Galaxy Phone Without Using Any Third-Party Tools
Samsung has a cool security feature built into One UI that has an interesting side effect, one that lets you have two separate copies of any Android app on your Galaxy phone. And that's not the only integrated Samsung tool for cloning apps.

How To: Exploit EternalBlue on Windows Server with Metasploit
Particular vulnerabilities and exploits come along and make headlines with their catchy names and impressive potential for damage. EternalBlue is one of those exploits. Originally tied to the NSA, this zero-day exploited a flaw in the SMB protocol, affecting many Windows machines and wreaking havoc everywhere. Here, we will use EternalBlue to exploit SMB via Metasploit.

How To: Crack Password-Protected Microsoft Office Files, Including Word Docs & Excel Spreadsheets
Microsoft Office files can be password-protected in order to prevent tampering and ensure data integrity. But password-protected documents from earlier versions of Office are susceptible to having their hashes extracted with a simple program called office2john. Those extracted hashes can then be cracked using John the Ripper and Hashcat.

How To: Crack Shadow Hashes After Getting Root on a Linux System
After gaining access to a root account, the next order of business is using that power to do something more significant. If the user passwords on the system can be obtained and cracked, an attacker can use them to pivot to other machines if the login is the same across systems. There are two tried-and-true password cracking tools that can accomplish this: John the Ripper and Hashcat.

How To: Check if Your Wireless Network Adapter Supports Monitor Mode & Packet Injection
To hack a Wi-Fi network, you need your wireless card to support monitor mode and packet injection. Not all wireless cards can do this, but you can quickly test one you already own for compatibility, and you can verify that the chipset inside an adapter you're thinking of purchasing will work for Wi-Fi hacking.

How To: Brute-Force FTP Credentials & Get Server Access
Hackers often find fascinating files in the most ordinary of places, one of those being FTP servers. Sometimes, luck will prevail, and anonymous logins will be enabled, meaning anyone can just log in. But more often than not, a valid username and password will be required. But there are several methods to brute-force FTP credentials and gain server access.

How To: The Top 80+ Websites Available in the Tor Network
There are nearly 100,000 unique onion service addresses online with over two million people using Tor every single day. Join me as I explore a small fraction of what the Tor network has to offer.

How To: Steam Food Without a Steamer Basket
I'm not a big fan of single-use tools, especially ones that don't get used particularly often. And I'm especially not a big fan of seldom used single-use tools that take up a large amount of space.
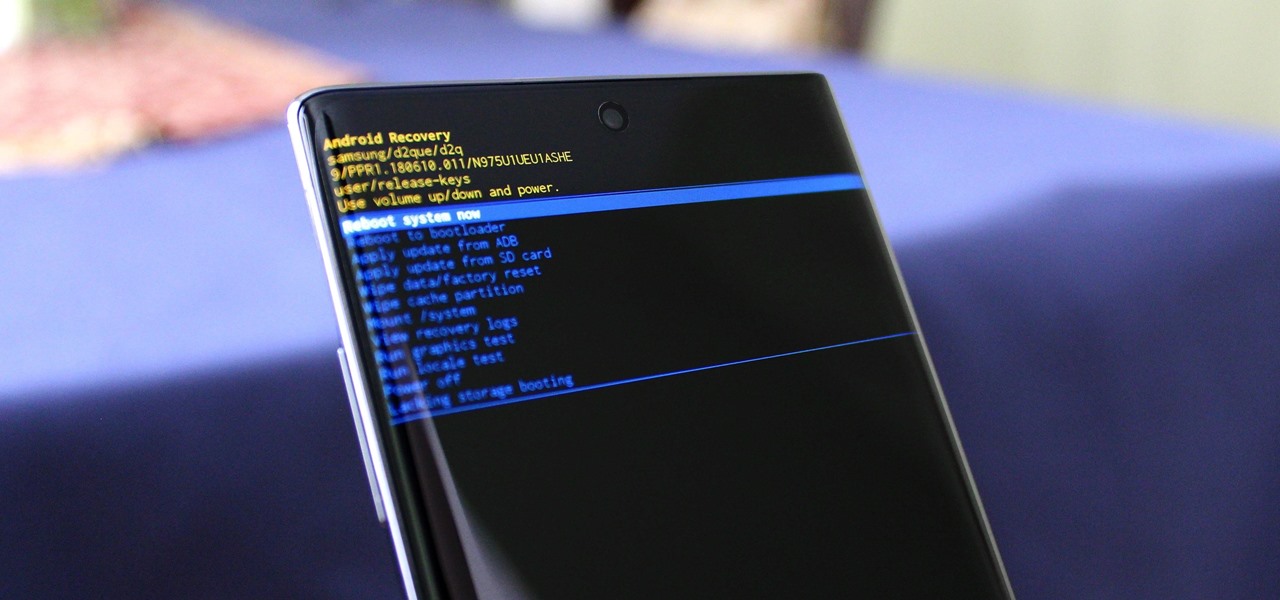
How To: Boot into Recovery Mode & Download Mode on the Galaxy Note 10+
You can't call yourself an Android pro without knowing about Recovery or Download Mode. These menus are critical to do more advanced tasks on your phone, include sideloading software updates and un-bricking a device. But this year, Samsung changed the button combinations that will get you there.

How To: Make Your Android Auto-Wipe Your Data When Stolen
Losing your phone is a much bigger ordeal today than it was just 10 years ago. Our smartphones carry with them lots of sensitive data that, in the wrong hands, is capable of being used for identity theft and fraud.

Scrabble Challenge #7: Can You Solve This Bingo Parallel Play for 150+ Points?
If you haven't noticed yet, I've started dishing out some "Scrabble Bingo of the Day" articles that showcase interesting and somewhat unusual seven-letter words (or longer) that could give you an extra 50-point bonus on the board, as long as you empty your rack. So, for this week's Scrabble Challenge you'll have to get your brain in gear, because it's a tough one based of high-scoring bingo plays.

How To: Use Burp & FoxyProxy to Easily Switch Between Proxy Settings
One of the best ways to dig into a website and look for vulnerabilities is by using a proxy. By routing traffic through a proxy like Burp Suite, you can discover hidden flaws quickly, but sometimes it's a pain to turn it on and off manually. Luckily, there is a browser add-on called FoxyProxy that automates this process with a single click of a button.

How To: The Trick That Lets You Link to Specific Start Times in YouTube Videos Right from Your Phone
You can add a timestamp to any YouTube video in just a few clicks from the desktop website on your computer but not from YouTube's iOS or Android app. Until YouTube adds a "start time" when sharing videos from the mobile app, you'll have to use one of these workarounds on your phone or tablet.
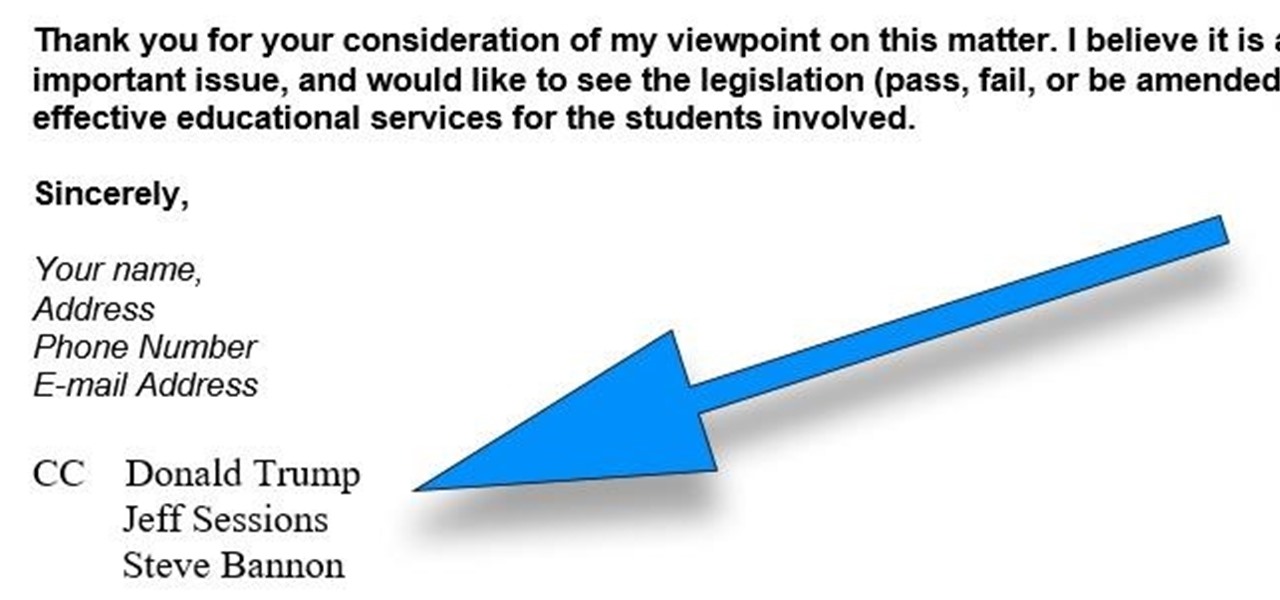
How To: CC in a Physical Business Letter
CC, which stands for "carbon copy", is a familiar phrase in email, but can also be used in business letters and legal documents. This can be especially useful for letters you want to spend up a company or organizational chain, letting each recipient know exactly who else received the same document.

How To: Clear Your Frequently Used and Recent Emoji from Your iPhone's Keyboard
Despite its name, the Frequently Used section on your iPhone's emoji keyboard features both frequently and recently used emoji, and it may contain emoji you've never even touched. If you want to remove all of those recommendations, there's an easy way to reset what you in Frequently Used to the defaults.

How To: Scan for Vulnerabilities on Any Website Using Nikto
Before attacking any website, a hacker or penetration tester will first compile a list of target surfaces. After they've used some good recon and found the right places to point their scope at, they'll use a web server scanning tool such as Nikto for hunting down vulnerabilities that could be potential attack vectors.

How To: 16 Harry Potter Spells for Siri That Turn Your iPhone into a Magical Elder Wand
Your days as an ordinary Muggle are over — as long as you have an iPhone. With just a word or two, you can use your iPhone and newfound Muggle-born powers to cast spells or utilize charms just like Harry Potter and team. Only your "wand" is from Apple, not Ollivanders in Diagon Alley.
How To: Your iPad Has a Hidden Built-in Calculator You're Not Using — Here's How to Unlock It
There is no iPad version of Apple's Calculator app, so you won't find it on your Home Screen, in your App Library, or as a shortcut in the Control Center. But that doesn't mean your iPad doesn't have an official calculator.

How To: Brute-Force Nearly Any Website Login with Hatch
The tactic of brute-forcing a login, i.e., trying many passwords very quickly until the correct one is discovered, can be easy for services like SSH or Telnet. For something like a website login page, we must identify different elements of the page first. Thanks to a Python tool for brute-forcing websites called Hatch, this process has been simplified to the point that even a beginner can try it.

Gaslighting 101: How to Turn People's Own Thoughts Against Them
This is evil and it destroys people. Let's just get that out of the way. Nonetheless, suppose you need to make someone distrust their own memory and perception of reality. Suppose you want someone to believe in you more than they believe in themselves.

How To: Enumerate SMB with Enum4linux & Smbclient
SMB (Server Message Block) is a protocol that allows resources on the same network to share files, browse the network, and print over the network. It was initially used on Windows, but Unix systems can use SMB through Samba. Today, we will be using a tool called Enum4linux to extract information from a target, as well as smbclient to connect to an SMB share and transfer files.

BT Recon: How to Snoop on Bluetooth Devices Using Kali Linux
While many people may use Bluetooth every day, the majority don't know how it works or that it can be hacked. Bluetooth hacking gives a clear window into the world of the target. Nearly every device has Bluetooth capabilities, and people store a great deal of personal info on their phones and tablets. Hack their Bluetooth connection, and you may be able to access all of that data.

How To: If 'Messages' Consumes Too Much iPhone or iCloud Storage, Don't Delete Your Conversations Just Yet
When iOS starts barking at you that you've run out of iCloud or iPhone storage, a quick trip to your settings to see what the culprit is may show that Messages is one of the worst offenders. But if deleting message after message doesn't free up your storage much, it's likely because "Messages" doesn't really mean messages.
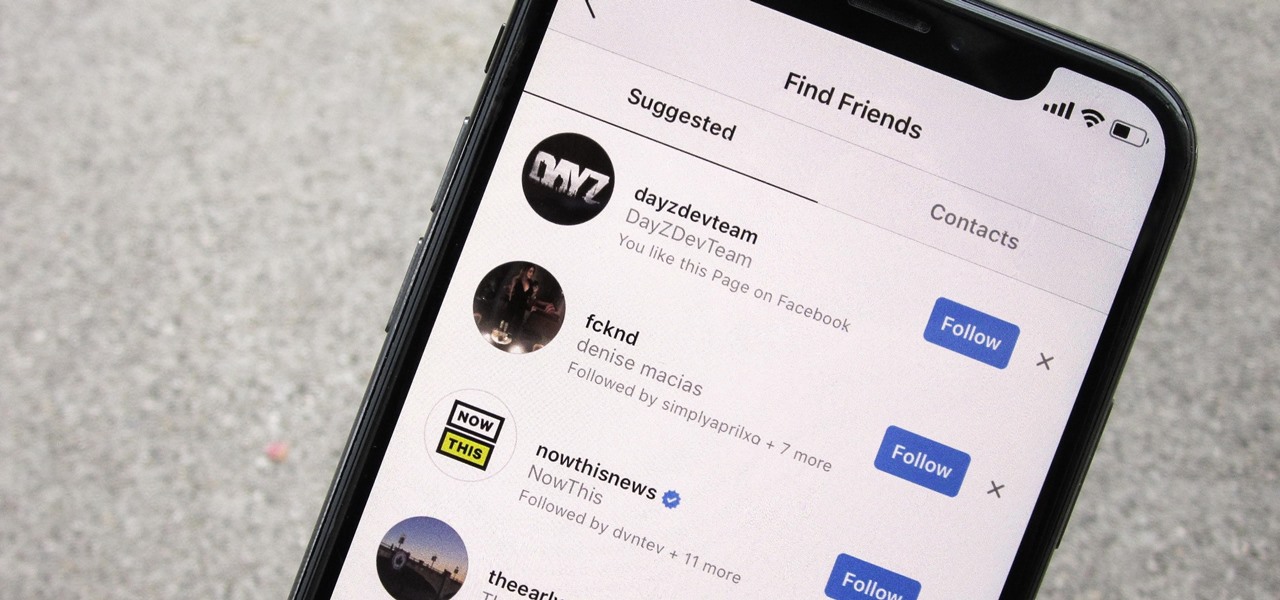
How To: Prevent People Who Have Your Contact Information from Finding Your Instagram Account
Sharing your personal information can come up for any number of reasons: you may want to get in touch with a colleague after work or you've been involved in a car accident and need to stay in contact with the other driver. Unfortunately, giving out information can be the key for others to find your social media accounts, such as Instagram, whether you want it to happen or not.

Modular Origami: How to Make a Cube, Octahedron & Icosahedron from Sonobe Units
Modular origami is a technique that can be used to build some pretty interesting and impressive models of mathematical objects. In modular origami, you combine multiple units folded from single pieces of paper into more complicated forms. The Sonobe unit is a simple example unit from modular origami that is both easy to fold and compatible for constructing a large variety of models. Below are a few models that are easy to make using this unit.

How To: 13 Tips Every Apple Pencil User Needs to Know for iPad
While it doesn't come with any iPad models out of the box, the Apple Pencil is perhaps the best iPad accessory you can get. It's a powerful writing and drawing tool with an intuitive design and user-friendliness that makes it easy to take notes, draw sketches, mark up documents, and more. And there's a lot you can do with it — some of which you may not have noticed yet.
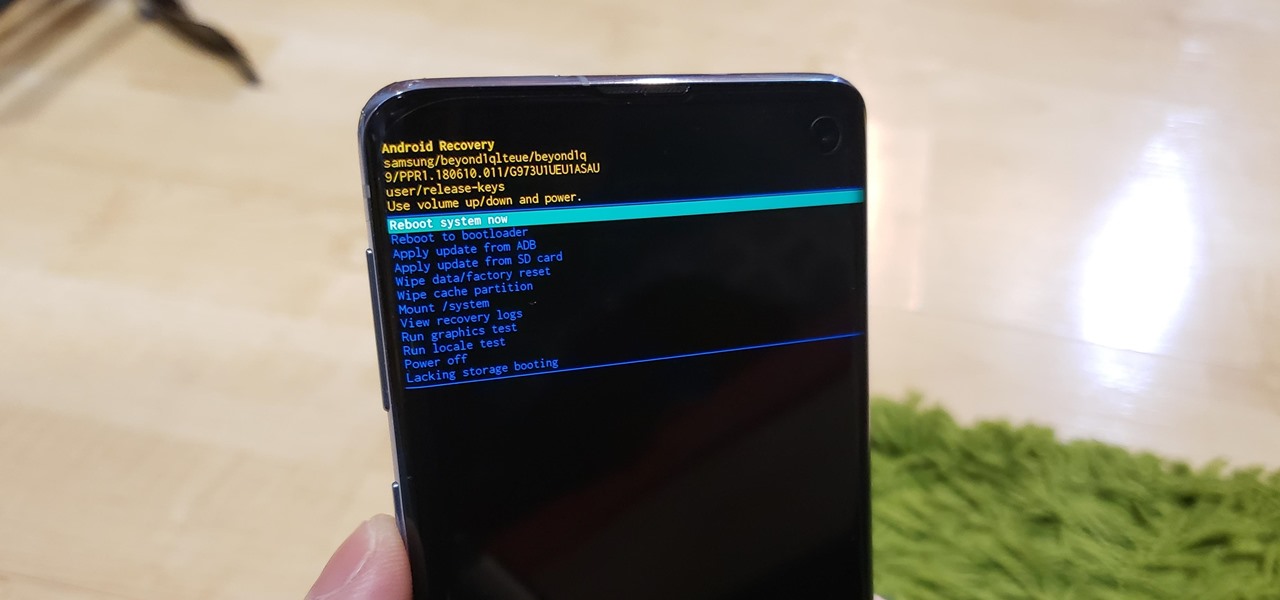
How To: Boot Your Galaxy S10 into Recovery Mode & Download Mode
You don't need to be a hardcore modder to know the importance of booting your S10 into either recovery mode or download mode. In fact, these pre-boot menus are something everyone should be familiar with. The former can help you get out of soft bricks, while the latter lets you use utilities like Odin and Smart Switch to flash firmware files and fix your phone when all other solutions fail.

How To: Exploit Shellshock on a Web Server Using Metasploit
One of the most critical bugs to come out in the last five years was Shellshock, a vulnerability which allows attackers to execute arbitrary code via the Unix Bash shell remotely. This vulnerability has been around for a while now, but due to the ubiquity of Unix machines connected to the web, Shellshock is still a very real threat, especially for unpatched systems.
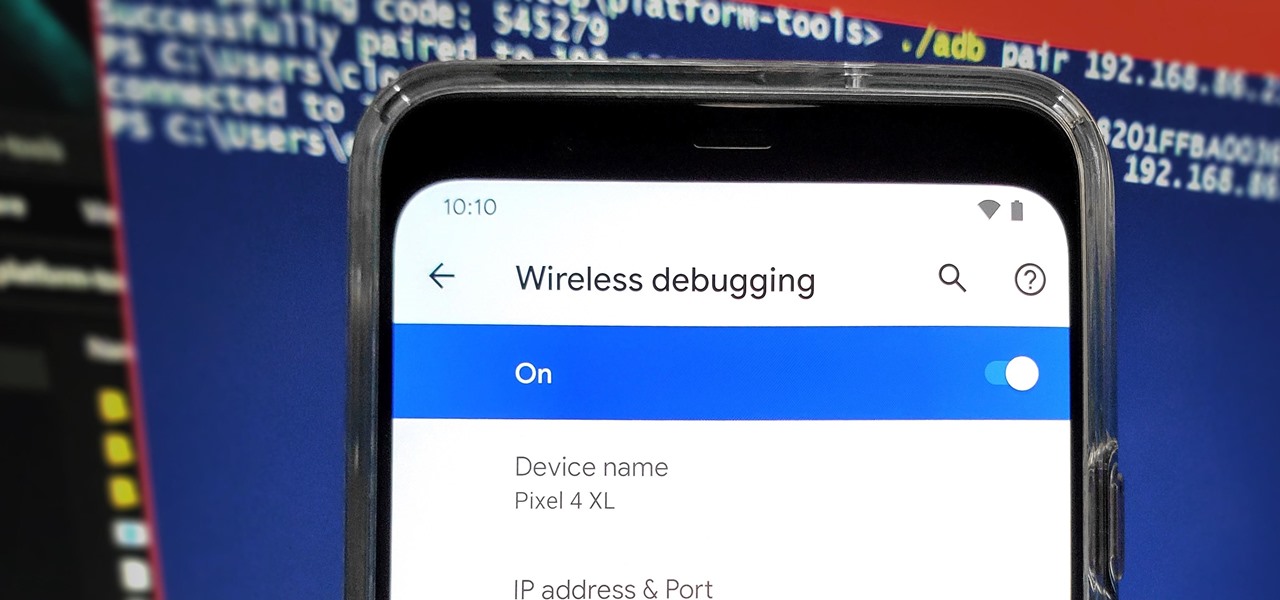
How To: Set Up Wireless Debugging on Android 11 to Send ADB Commands Without a USB Cable
From booting into Fastboot mode with a single command to installing mods without root access, there's no shortage of reasons to use ADB. The catch, though, you had to be tied to a computer with a USB connection. However, a new feature in Android 11 finally allows you to run ADB commands over Wi-Fi instead of being tethered.

How To: Bypass File Upload Restrictions on Web Apps to Get a Shell
One of the most promising avenues of attack in a web application is the file upload. With results ranging from XSS to full-blown code execution, file uploads are an attractive target for hackers. There are usually restrictions in place that can make it challenging to execute an attack, but there are various techniques a hacker could use to beat file upload restrictions to get a shell.

How To: Manually Switch to a Different LTE Band on Any Samsung Galaxy Phone
Your Galaxy uses information from your SIM card to communicate with nearby towers and facilitate a connection. Which LTE bands you are assigned depends on a number of factors, including available bandwidth and your device's supported signals. But if speeds aren't great on your auto-selected tower, you can improve things by manually choosing a band.